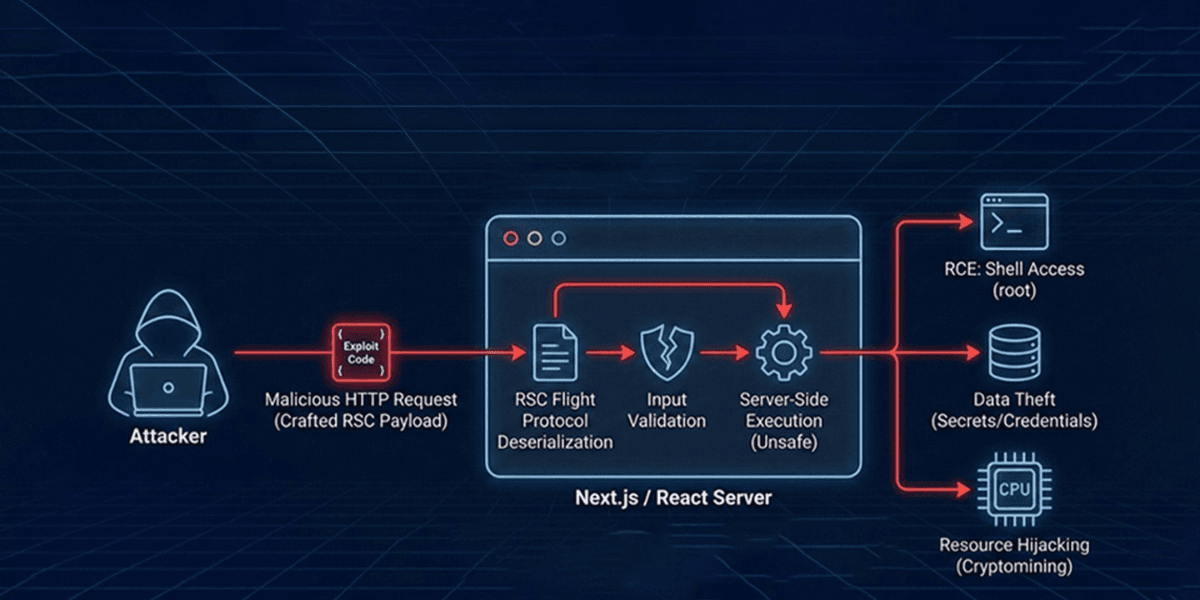
A critical security vulnerability, dubbed "React2Shell", was publicly disclosed, sending shockwaves through the JavaScript ecosystem. Tracked as CVE-2025-55182, this flaw carries a maximum CVSS score of 10.0 (Critical) and allows for unauthenticated Remote Code Execution (RCE) on affected applications. Given the severity and confirmed active exploitation, immediate patching is required.
What Makes React2Shell So Dangerous?
The vulnerability is fundamentally rooted in the implementation of React Server Components (RSC). Specifically, the issue is an unsafe deserialization flaw within the RSC "Flight" protocol, which handles communication between the server and client.
1. Arbitrary Code Execution: The server fails to validate the structure of incoming RSC payloads properly. By crafting a malicious HTTP request, an attacker can manipulate this deserialization logic, causing the execution of privileged JavaScript code on the server.
2. Zero Authentication Required: This is a crucial detail; an attacker requires no credentials, tokens, or user interaction to exploit the vulnerability. They only need network access to send a specially crafted HTTP request to any Server Function endpoint.
3. Default Configurations Are Vulnerable: Applications are at risk simply by supporting React Server Components, even if they do not explicitly define or use React Server Function endpoints.
Affected Products and Ecosystem Impact
This vulnerability originates in the upstream React implementation, impacting multiple frameworks that rely on React Server Components and the App Router pattern.
Affected React Packages (Versions 19.0.0 through 19.2.0)
The core vulnerability affects the packages used to implement RSC:
react-server-dom-webpack
react-server-dom-parcel
react-server-dom-turbopack
Affected Next.js Versions (Using the App Router):
The downstream impact on Next.js is tracked under CVE-2025-66478 (though later rejected as a duplicate of CVE-2025-55182, it identifies affected versions.)
Next.js 15.x and 16.x.
Specific ranges include: >=14.3.0-canary.77 <15.0.5, >=15.1.0 <15.1.9, >=15.2.0-canary.0 <15.2.6, >=15.3.0-canary.0 <15.3.6, >=15.4.0-canary.0 <15.4.8, >=15.5.0 <15.5.7, and >=16.0.0-beta.0 <16.0.7.
Other Vulnerable Frameworks:
Any framework or library bundling the react-server implementation is potentially vulnerable, including:
Waku
Vite RSC plugin (@vitejs/plugin-rsc)
Parcel RSC plugin (@parcel/rsc)
React Router (RSC preview)
Redwood SDK (rwsdk)
Note: Next.js 13.x, Next.js 14.x stable, Pages Router applications, and the Edge Runtime are not affected. Applications running React exclusively on the client side are also safe.
Active Exploitation: A Race Against Threat Actors
Exploitation attempts began within hours of the public disclosure on December 3, 2025. Snyk has reported successful attacks targeting this vulnerability.
Sophisticated Threat Groups Involved
Amazon threat intelligence teams observed active exploitation attempts by multiple China state-nexus threat groups, including Earth Lamia and Jackpot Panda. These groups quickly weaponize public proof-of-concept (PoC) exploits and conduct broad campaigns to maximize targets.
Attack Objectives Observed in the Wild
Threat actors are using this critical vulnerability to achieve several high-impact goals against vulnerable cloud workloads and internet-facing Next.js applications:
1. Credential Harvesting: Attackers aggressively scrape environment variables for cloud secrets (AWS, TOKEN, SECRET) and attempt to access cloud instance metadata services (like 169.254.169.254/latest/meta-data/iam/security-credentials/) to steal IAM credentials.
2. Cryptomining Deployment: Several distinct campaigns have been observed deploying Monero miners (e.g., XMRig, Kinsing, identified by malware signatures like kdevtmpfsi) into compromised containers to steal CPU resources.
3. Backdoor Installation: More advanced actors have been seen deploying fully featured backdoors, such as Sliver implants (64-bit ELF binaries), indicating a shift from opportunistic mining to securing long-term access.
4. Reconnaissance and Persistence: Attackers execute Linux commands like whoami and id, read sensitive files like /etc/passwd, and establish persistence via malicious cron jobs.
Wiz Research data highlights the scope, showing that 39% of cloud environments contain vulnerable instances, and approximately 2.15 million internet-facing services were potentially exposed according to Censys data.
Detailed Video:-
Immediate Action Required: Patch Now!
Patching is the single most important step; temporary protections are not a substitute.
- Upgrade Next.js Immediately
Upgrade Next.js to the latest patched version in your release line:
15.0.5
15.1.9
15.2.6
15.3.6
15.4.8
15.5.7
16.0.7If you are on a vulnerable canary release (>=14.3.0-canary.77), downgrade to the latest stable 14.x release or upgrade to a patched canary version like 15.6.0-canary.58. - Update React Packages
Update affected React Server Components packages to fixed versions:
19.0.1
19.1.2
19.2.1 - Post-Patching Hygiene
Suppose your application was running unpatched after December 4th, 2025. In that case, you must assume a compromise and take these actions:- Rotate All Secrets: Strongly encourage rotating all application secrets, environment variables, and cloud credentials, starting with the most critical ones. Attackers prioritize credential theft.
Scan for Indicators of Compromise (IOCs): Review application and web server logs for suspicious activity:
Network: HTTP POST requests containing next-action or rsc-action-id headers, or request bodies containing patterns like $@ or "status": "resolved_model".
Host-based: Unexpected execution of commands like whoami or id, attempts to read /etc/passwd, or suspicious file writes to the /tmp/ directory (e.g., pwned.txt).
- Implement Temporary Protections: If patching is delayed, deploy Web Application Firewall (WAF) rules (such as updated AWS WAF managed rules) and monitor traffic to Server Function endpoints, although WAF rules are known to have bypasses.
Conclusion
React2Shell (CVE-2025-55182) is one of the most severe RCE risks the React ecosystem has ever faced. With active exploitation already underway, the only real protection is immediate patching and full secret rotation for any app exposed after December 4th, 2025.
Teams that act fast will limit the damage; teams that delay risk credential theft, cryptomining, and long-term backdoors. Patch now, verify your environment, and strengthen your security posture going forward.
Links:-
https://nextjs.org/blog/CVE-2025-66478
https://react.dev/blog/2025/12/03/critical-security-vulnerability-in-react-server-components
From predictive models to clinical AI, our Healthcare AI Solutions practice helps healthcare organizations deploy AI that delivers real outcomes. Talk to our team to get started.