The Wake-Up Call: ABDM Compliance Is No Longer Optional
For years, Ayushman Bharat Digital Mission (ABDM) integration has been positioned as a forward-looking initiative — something hospitals could adopt at their own pace, if they chose to at all. That era is ending.
In early 2026, the CEO of Bihar’s Swasthya Suraksha Samiti issued a direct compliance directive to all private hospitals empanelled under the Ayushman Bharat Pradhan Mantri Jan Arogya Yojana (AB-PMJAY) in the state. The message was unambiguous: integrate with ABDM or face consequences, including de-empanelment.
Bihar is not an isolated case. It is a signal of what is coming nationally. The National Health Authority (NHA) has been laying the groundwork for mandatory ABDM compliance across all AB-PMJAY empanelled hospitals, and the enforcement machinery is now operational. With the Government of India having sanctioned INR 1,600 crores over five years (FY 2021–22 to FY 2025–26) for ABDM implementation, the investment thesis is clear: this infrastructure is here to stay, and participation is shifting from voluntary to mandatory.
If your hospital is empanelled under AB-PMJAY — or if you are a health-tech vendor serving such hospitals — the window to act is narrowing. This guide lays out exactly what is happening, what it means for you, and what you need to do about it.
Who This Affects: The Full Scale of the Mandate
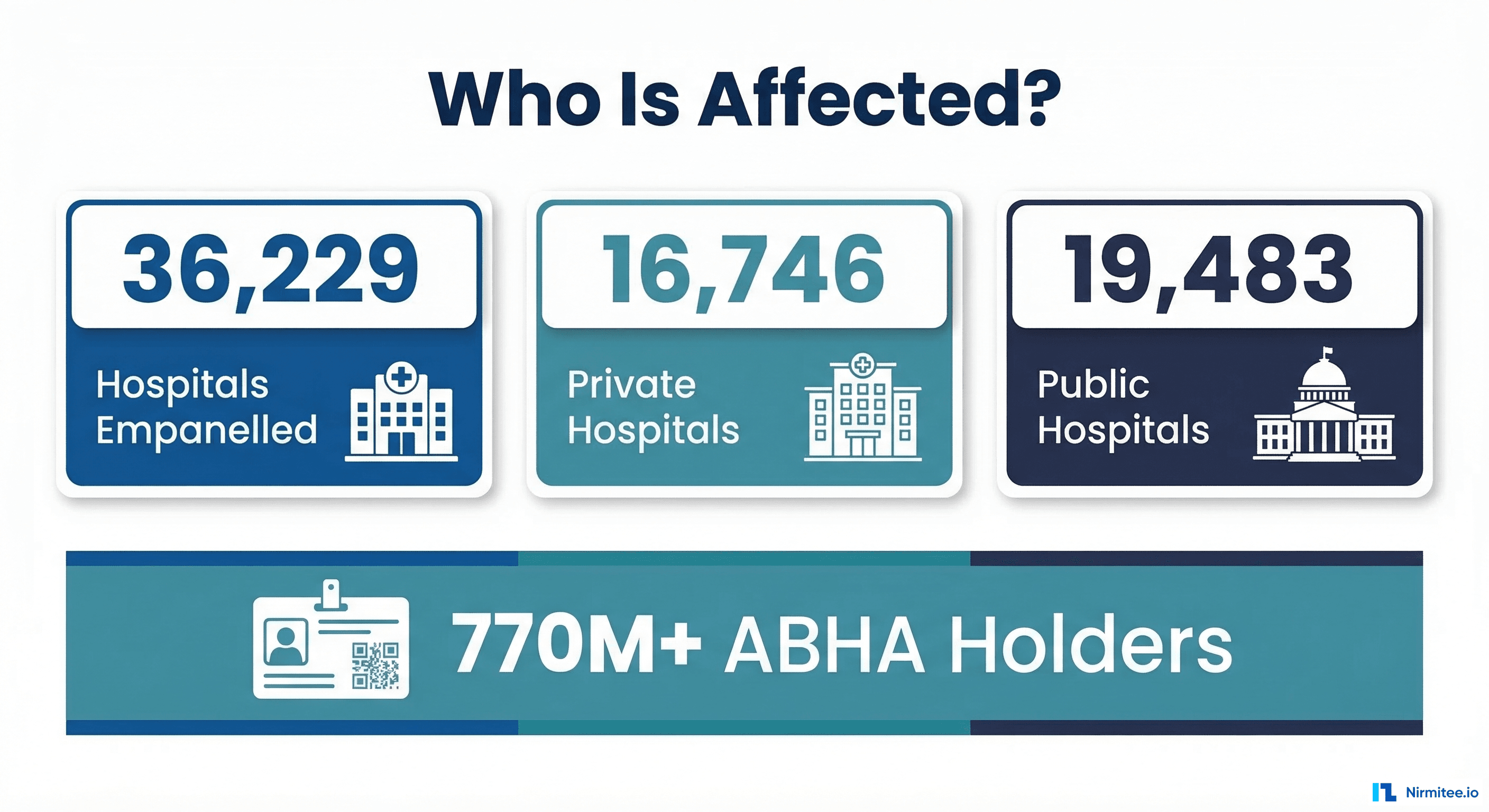
The scope of this mandate is staggering. As of February 28, 2026, there are 36,229 hospitals empanelled under AB-PMJAY across India:
- 19,483 public hospitals (district hospitals, sub-district hospitals, CHCs, PHCs)
- 16,746 private hospitals (from large multi-specialty chains to small single-specialty units)
Every one of these hospitals falls under the compliance umbrella. But the impact extends far beyond the hospitals themselves:
- Hospital Information System (HIS) vendors whose software powers these facilities must enable ABDM integration within their platforms
- Laboratory Information Systems (LIMS), Radiology Information Systems (RIS), and Pharmacy Management Systems must all be capable of sharing data in ABDM-compliant formats
- Health-tech startups and IT integrators serving the hospital ecosystem need to build or embed ABDM capabilities
- State health agencies administering AB-PMJAY at the state level are the enforcement arm of this mandate
The numbers tell the story of India’s digital health momentum: over 770 million Indians now hold an ABHA (Ayushman Bharat Health Account), and more than 530 million health records have been digitized and linked. The ecosystem is maturing rapidly, and the expectation is that hospitals will keep pace.
What ABDM Compliance Actually Means — In Plain Language
ABDM compliance is not a single checkbox. It is a structured set of technical and operational capabilities that your hospital’s digital systems must demonstrate. Let us break it down without the developer jargon.
Milestone 1 (M1): Patient Identity — The ABHA Layer
At its core, M1 is about ensuring every patient who walks into your hospital can be uniquely identified in India’s digital health ecosystem. This means:
- Creating ABHA numbers for patients who do not have one (via Aadhaar OTP or demographic verification)
- Capturing and verifying ABHA numbers at registration for patients who already have one
- Linking the ABHA to the patient’s record in your Hospital Information System
- Enabling QR-based profile share so patients can share their ABHA identity seamlessly
Think of M1 as giving every patient a universal health ID that works across hospitals, labs, pharmacies, and insurance — and your system needs to recognize and use it.
Milestone 2 (M2): Sharing Health Records — The HIP Role
M2 is where your hospital becomes a Health Information Provider (HIP). When a patient gives consent, your system must be able to share their health records digitally with other authorized entities. This involves:
- Creating care contexts (visit records, discharge summaries, prescriptions, lab reports) in FHIR R4 format
- Handling consent requests — when a patient grants consent to another provider, your system must respond with the requested data
- Encrypting and transmitting health records securely through the ABDM Health Information Exchange
- Supporting patient discovery — when other systems search for a patient’s records, your system must respond accurately
M2 is the heavy lift for most hospitals. It requires your EHR/HIS to produce structured, standards-compliant health data — not just store it in proprietary formats.
Milestone 3 (M3): Accessing Patient History — The HIU Role
M3 makes your hospital a Health Information User (HIU). This means your system can request and receive health records from other providers (with patient consent). Benefits include:
- Pulling patient history from other hospitals, labs, and clinics before a consultation
- Aggregating records from multiple sources into a unified patient view
- Initiating and managing consent requests to access external records
For hospital administrators, M3 is where the value proposition of ABDM becomes tangible: your doctors get a complete patient picture, reducing redundant tests and improving clinical outcomes.
Beyond the Milestones: Certification and Security
Completing M1, M2, and M3 in the ABDM sandbox is only part of the journey. To go live in production, you also need:
- Functional testing by an NHA-empanelled agency (currently FIME, Suma Soft, or Tata Consultancy Services)
- WASA (Web Application Security Audit) by a CERT-IN empanelled agency
- Safe-to-Host certificate for your production infrastructure
- NHA approval and issuance of production credentials
For a detailed walkthrough of each milestone’s technical requirements, see our comprehensive guide to ABDM milestones M1 through M4. For the full certification pipeline from sandbox to production, refer to our ABDM certification process guide.
The Consequences of Non-Compliance
This is where the conversation shifts from “should we comply?” to “can we afford not to?” The consequences of failing to meet ABDM compliance requirements are not theoretical. State health agencies have already begun enforcement, and the penalty framework is clear:
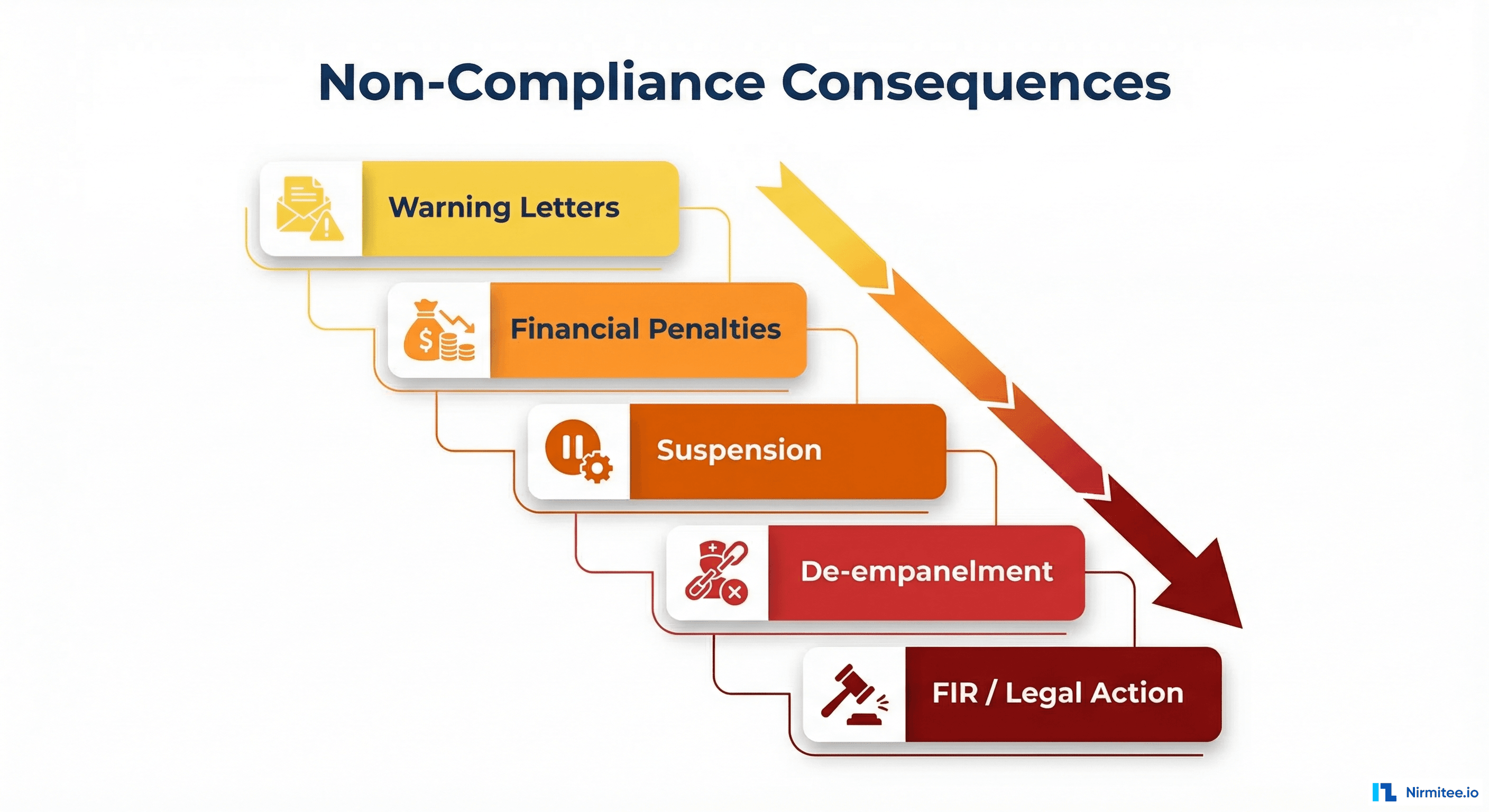
1. Warning Letters
The first step in enforcement. State agencies issue formal notices to hospitals that have not initiated or progressed on ABDM integration. These warnings come with deadlines and are documented — they are not informal reminders.
2. Financial Penalties
Hospitals that fail to respond to warnings face monetary penalties. The specifics vary by state, but the financial impact is designed to be significant enough to compel action, particularly for smaller hospitals operating on thin margins.
3. Suspension
Continued non-compliance can lead to temporary suspension from the AB-PMJAY network. During suspension, the hospital cannot process AB-PMJAY claims — which means no reimbursements for treatments provided to AB-PMJAY beneficiaries. For hospitals where AB-PMJAY patients constitute 20–40% or more of their volume, this is a direct hit to revenue.
4. De-empanelment from AB-PMJAY
The most severe administrative action: permanent removal from the AB-PMJAY empanelled hospital list. This cuts off access to the entire AB-PMJAY patient base and the associated revenue stream. Re-empanelment, if permitted, requires starting the process from scratch.
5. FIRs and Legal Action
In cases of deliberate non-compliance, fraud, or obstruction, state agencies have the authority to file First Information Reports (FIRs) against errant hospitals. While this is the most extreme enforcement mechanism, the fact that it exists in the framework signals the seriousness of the mandate.
The Revenue Risk Is Real
For many private hospitals in tier 2 and tier 3 cities, AB-PMJAY is not a minor revenue line — it is a foundational income stream. India’s AB-PMJAY scheme covers over 55 crore beneficiaries (roughly 40% of the population) with health coverage up to INR 5 lakh per family per year. Losing access to this patient pool is not something any hospital can absorb without significant financial impact.
The ABDM Compliance Roadmap: Step by Step
Understanding what needs to be done is one thing. Knowing the exact sequence of actions is another. Here is a practical, step-by-step roadmap for hospitals navigating ABDM compliance.
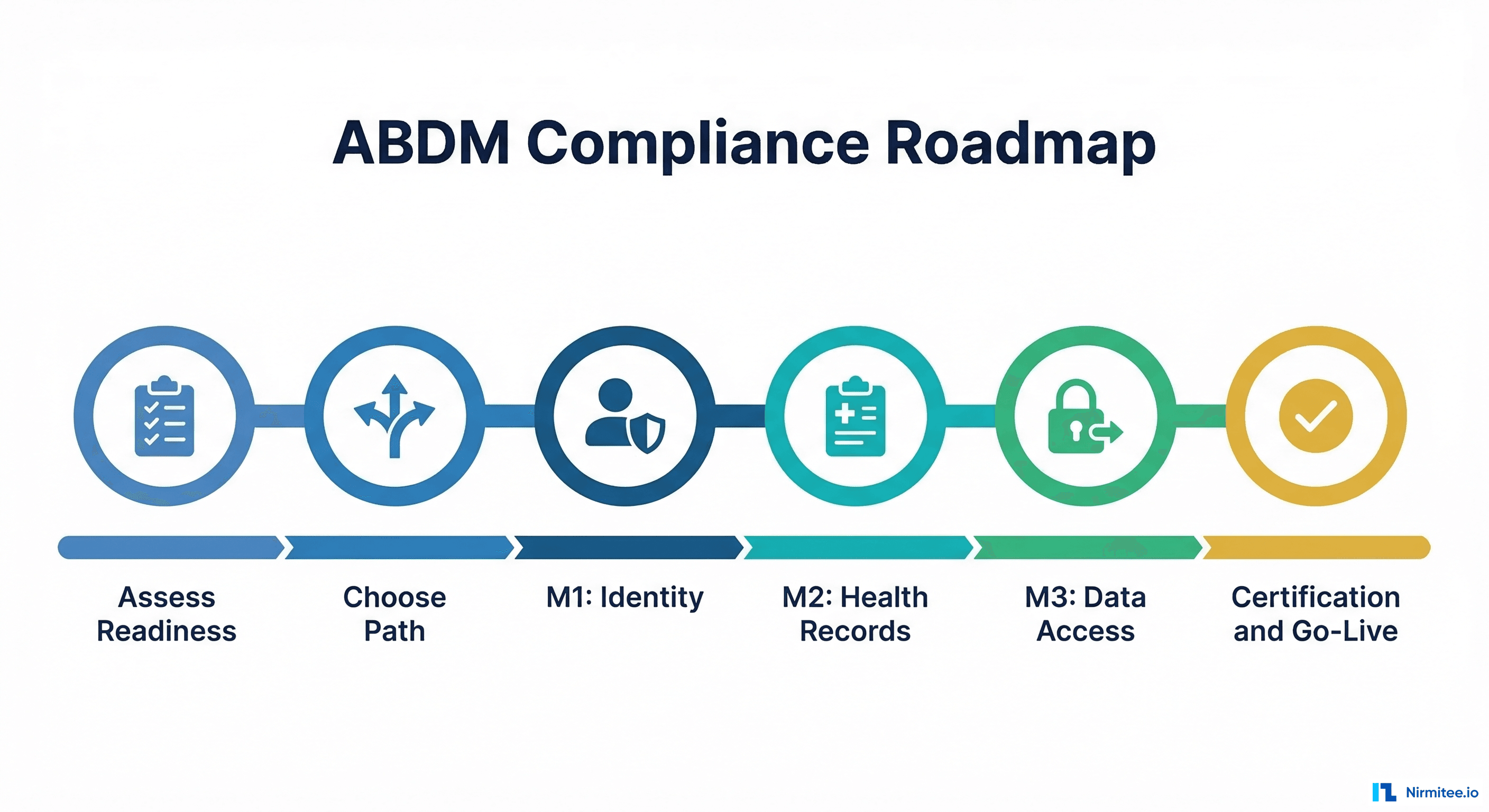
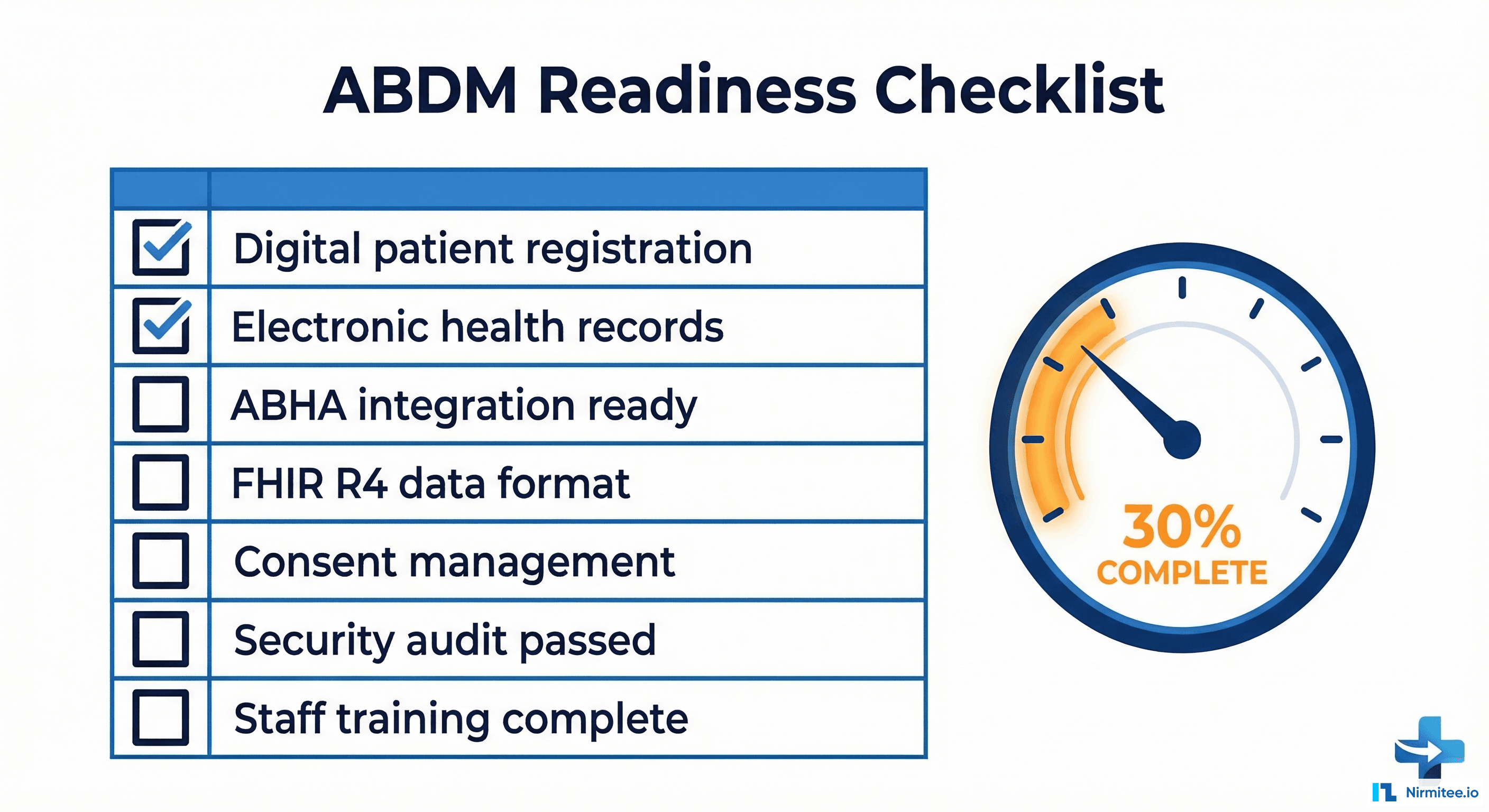
Step 1: Assess Your Current Digital Readiness
Before anything else, you need an honest evaluation of where your hospital stands today. Key questions:
- Do you have a digital Hospital Information System (HIS), or are you still on paper-based records?
- Can your HIS produce structured data (not just free-text notes)?
- Do you capture patient demographics digitally at registration?
- Is your system capable of generating FHIR R4-compliant health records?
- Do you have IT staff or a vendor relationship that can support integration work?
- Is your infrastructure (servers, network, security) adequate for production-grade ABDM integration?
Most hospitals in tier 2 and tier 3 cities will find gaps here. That is expected. The assessment is not about passing a test — it is about knowing the starting point so you can plan realistically.
Step 2: Choose Your Integration Path
Based on your readiness assessment, you will choose one of three paths (more on this in the next section):
- Build in-house — if you have a large IT team and want full control
- Buy from an ABDM-certified vendor — if you need speed and simplicity
- Middleware approach — if you want to keep your existing systems and add an ABDM layer
Step 3: Complete M1 (ABHA Integration)
Register on the ABDM sandbox, implement ABHA creation and verification APIs, and pass M1 functional testing. This is typically the fastest milestone to complete (2–4 weeks for an experienced team).
Step 4: Complete M2 (Health Information Provider)
This is the most technically demanding milestone. You need to implement care context creation, patient discovery, consent management, and health record sharing in FHIR R4 format. Timeline: 4–12 weeks depending on your system’s data maturity. See our step-by-step integration guide for technical setup details.
Step 5: Complete M3 (Health Information User)
Implement the ability to request and receive health records from other providers with patient consent. If you have completed M2 well, M3 shares much of the same infrastructure and typically takes 2–4 additional weeks.
Step 6: Certification and Go-Live
After completing all milestones in the sandbox:
- Apply for functional testing with an NHA-empanelled testing agency
- Complete WASA (Web Application Security Audit) with a CERT-IN empanelled agency
- Obtain Safe-to-Host certificate for your production environment
- Submit for NHA review and receive production credentials
- Go live on the ABDM production network
The certification process alone can take 4–8 weeks, so factor this into your planning. The total end-to-end timeline from kickoff to production is typically 3–6 months for hospitals with existing digital infrastructure, and 6–12 months for those starting from scratch.
Build vs. Buy vs. Middleware: The Three Paths to Compliance
One of the most consequential decisions a hospital will make in this journey is how to achieve ABDM compliance. There is no one-size-fits-all answer — the right path depends on your hospital’s size, technical maturity, budget, and timeline.
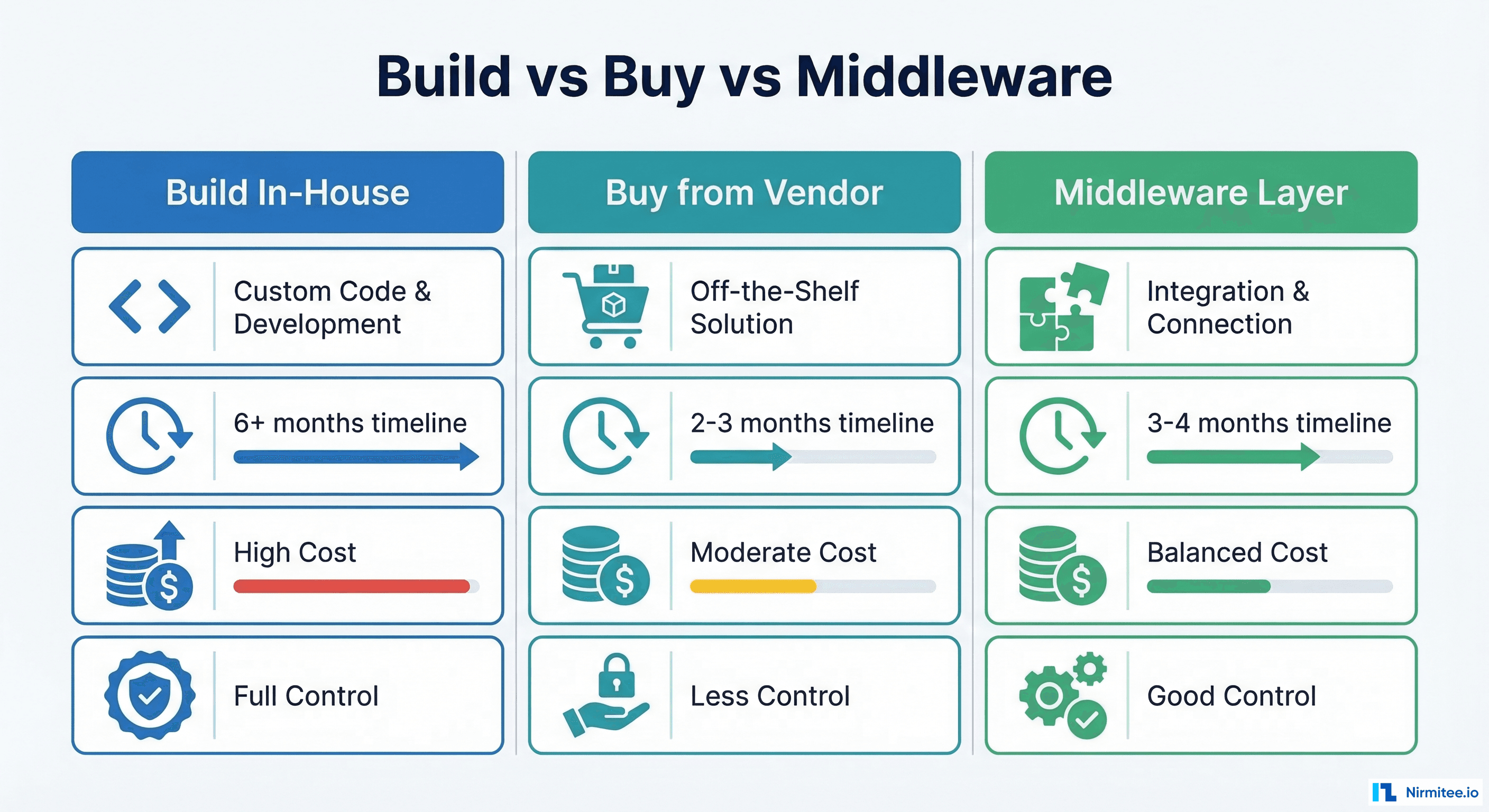
Path 1: Build In-House
Best for: Large hospital chains with dedicated IT teams, or hospitals that are also software companies.
What it involves: Your development team directly integrates ABDM APIs into your existing HIS/EHR. You build the FHIR conversion layer, consent management, encryption, and data exchange pipelines from the ground up.
Advantages:
- Full control over the implementation and data flow
- Deep integration with your existing workflows
- No dependency on third-party vendors for ongoing operations
- Ability to customize every aspect of the ABDM experience
Challenges:
- Requires significant in-house FHIR and ABDM expertise (which is rare and expensive)
- Timeline: 6–12+ months to full production readiness
- Ongoing maintenance burden as ABDM APIs evolve (the V3 migration is a recent example)
- Risk of rework if NHA changes specifications mid-development
Path 2: Buy from an ABDM-Certified Vendor
Best for: Hospitals that want the fastest path to compliance and are willing to adopt a new system or replace their existing one.
What it involves: You procure an HIS/EHR that already has ABDM certification (all milestones completed and NHA-approved). You migrate your data and workflows to the new system.
Advantages:
- Fastest time to compliance (2–4 months including deployment and training)
- Pre-certified — no need to go through sandbox testing and certification yourself
- Vendor handles ongoing ABDM updates and maintenance
Challenges:
- Data migration from your existing system can be complex and risky
- Staff retraining on a completely new system
- Vendor lock-in — you are dependent on their roadmap and pricing
- Less control over customization and data handling
- May not integrate well with your existing LIMS, RIS, or pharmacy systems
Path 3: Middleware Layer on Existing Systems
Best for: Hospitals that want to keep their existing HIS/EHR but need to add ABDM capabilities without rebuilding everything.
What it involves: A middleware platform sits between your existing hospital systems and the ABDM network. It pulls data from your HIS, LIMS, RIS, and pharmacy systems, converts it to FHIR R4 format, handles consent management, and manages the ABDM data exchange — all without requiring changes to your core systems.
Advantages:
- No disruption to existing workflows — your staff keeps using the systems they know
- Works with multiple systems simultaneously (HIS + LIMS + RIS + Pharmacy)
- Typically 3–5 months to production readiness
- Handles FHIR conversion and consent management centrally
- Easier to maintain as ABDM evolves — updates happen in the middleware, not across every system
Challenges:
- Requires good API or database access to your existing systems
- Adds a new component to your technology stack that needs monitoring
- Data transformation quality depends on the middleware vendor’s understanding of your data models
Which Path Is Right for You?
| Factor | Build In-House | Buy from Vendor | Middleware |
|---|---|---|---|
| Timeline to compliance | 6–12+ months | 2–4 months | 3–5 months |
| Disruption to current operations | Low–Medium | High | Low |
| IT team requirement | Large, specialized | Small | Medium |
| Control over implementation | Full | Limited | Moderate |
| Ongoing maintenance | Your responsibility | Vendor managed | Shared |
| Works with existing systems | Yes | Replacement | Yes |
| Multi-software support | Complex | Single system only | Native strength |
Timeline: How Long You Actually Have
Let us be direct about timelines. While the exact national enforcement deadline has not been published as a single date, the signals are clear:
- State-level enforcement has begun. Bihar’s directive is live. Other states are expected to follow in 2026.
- NHA’s five-year ABDM budget cycle (FY 2021–22 to FY 2025–26) concludes this year. The next cycle will likely come with harder compliance requirements.
- The ABDM infrastructure is production-ready. With 770M+ ABHA holders and 530M+ linked records, the “it’s not ready yet” argument no longer holds.
- AB-PMJAY claim processing is increasingly being linked to digital health compliance. Hospitals that cannot demonstrate ABDM readiness may face claim processing delays even before formal de-empanelment.
A Realistic Timeline Breakdown
| Phase | Duration (Estimate) | Key Activities |
|---|---|---|
| Readiness Assessment | 1–2 weeks | Audit current systems, identify gaps, choose integration path |
| Vendor/Partner Selection | 2–4 weeks | Evaluate options, negotiate terms, sign contracts |
| M1 Implementation | 2–4 weeks | ABHA creation, verification, profile share |
| M2 Implementation | 4–12 weeks | FHIR conversion, care contexts, consent handling, HIP role |
| M3 Implementation | 2–4 weeks | HIU role, consent requests, data aggregation |
| Functional Testing | 2–4 weeks | Testing by NHA-empanelled agency |
| WASA + Safe-to-Host | 2–4 weeks | Security audit, infrastructure certification |
| NHA Approval | 2–4 weeks | Review and production credential issuance |
Total: 3–8 months from start to production go-live.
If you are reading this in March 2026 and have not started, you are already behind. Starting today gives you the best chance of being compliant before enforcement reaches your state.
What Small and Mid-Size Hospitals Should Do Differently
The guidance above applies broadly, but hospitals in tier 2 and tier 3 cities face unique challenges that require a different approach. These hospitals often form the backbone of AB-PMJAY service delivery in their regions, yet they are the least prepared for ABDM compliance.
Challenge 1: Outdated or Partially Digital Systems
Many hospitals in smaller cities run legacy HIS software that was never designed for interoperability. Some still operate on a mix of paper and basic digital records. The jump to ABDM-compliant FHIR R4 data exchange can feel insurmountable.
What to do: Do not try to upgrade your entire HIS. Instead, adopt a middleware approach that can extract data from your existing system (even via database queries if APIs are not available) and handle the ABDM translation layer externally. This gets you compliant without a full system overhaul.
Challenge 2: Limited IT Staff and Expertise
A 50-bed hospital in a tier 3 city does not have a team of FHIR developers. They may have one IT administrator who manages the HIS, networking, and everything else technology-related.
What to do: Partner with an ABDM integration specialist rather than trying to build internally. Look for partners who have completed multiple ABDM certifications and can handle the end-to-end process, including sandbox testing, functional testing coordination, and WASA.
Challenge 3: Staff Awareness and Training
Front-desk staff, nurses, and even doctors may not understand what ABHA is, why patients need it, or how to use the new digital workflows. This is not a technology problem — it is a change management problem.
What to do: Invest in targeted training programs. Front-desk staff need to know how to create and verify ABHA numbers. Clinical staff need to understand that their documentation practices directly affect ABDM compliance (structured clinical notes become FHIR resources). Start training early, even before the technical integration is complete.
Challenge 4: Consent Management Is Operationally Complex
ABDM’s consent framework is patient-centric, which is excellent for patients but operationally demanding for hospital staff. Managing consent artifacts, responding to consent requests from external entities, and ensuring data is shared only within the boundaries of granted consent requires process discipline that many hospitals have not built yet.
What to do: Choose integration solutions that automate consent management as much as possible. The best middleware solutions handle consent artifacts, expiry tracking, and data filtering automatically, reducing the operational burden on your staff.
Challenge 5: Infrastructure Limitations
Reliable internet connectivity, server uptime, and cybersecurity are prerequisites for ABDM compliance that some hospitals in smaller cities may struggle with. The WASA (security audit) alone requires a certain baseline of infrastructure maturity.
What to do: Consider cloud-hosted ABDM integration solutions that minimize on-premise infrastructure requirements. If your middleware or integration layer runs in the cloud, the infrastructure burden shifts to the provider, and your hospital only needs a stable internet connection.
Common Mistakes Hospitals Make on the ABDM Journey
Having worked with hospitals at various stages of ABDM integration, we see the same mistakes repeated. Here are the ones that cost the most time and money:
Mistake 1: Treating ABDM as a Pure IT Project
ABDM compliance touches registration, clinical documentation, nursing workflows, lab reporting, pharmacy dispensation, and billing. Handing it to your IT team without involving operations, clinical leadership, and administration leads to technically correct but operationally broken implementations.
Mistake 2: Starting with M2 Before Getting M1 Right
M1 (ABHA integration) seems simple, so hospitals rush through it to get to the “real work” of M2. But a sloppy M1 implementation — incorrect ABHA linking, missing demographic verification, poor QR handling — creates cascading problems in M2 when you try to create care contexts for patients whose identities are not properly established.
Mistake 3: Underestimating FHIR Conversion Complexity
Converting your existing clinical data into FHIR R4 bundles is not a simple field-mapping exercise. It requires deep understanding of both your source data model and the FHIR resource specifications (Patient, Encounter, DiagnosticReport, MedicationRequest, etc.). Hospitals that treat this as a weekend project end up with months of rework.
Mistake 4: Ignoring the V3 API Migration
ABDM has migrated from V0.5 to V3 APIs, and the differences are significant. V3 introduces synchronous discovery (instead of async callbacks), linking tokens during profile share, and new endpoint structures. If your integration work is based on outdated documentation or V0.5 patterns, you will need to refactor substantially.
Mistake 5: Delaying the Security Audit
The WASA (Web Application Security Audit) is not a formality. CERT-IN empanelled agencies conduct thorough assessments, and many applications fail on their first attempt. Common failures include insecure data storage, missing encryption, inadequate access controls, and unpatched vulnerabilities. Start your security remediation early — do not wait until the functional testing is complete.
Mistake 6: Not Planning for Multi-Software Integration
Real hospitals do not run on a single software system. A typical mid-size hospital operates 4–8 separate systems (HIS, LIMS, RIS/PACS, pharmacy management, billing). ABDM expects a unified view of the patient’s data across all these systems. Hospitals that only integrate their HIS and ignore LIMS and RIS data will have incomplete care contexts and may fail functional testing.
Mistake 7: Waiting for a “Final” Deadline
Some hospital administrators are waiting for a single, clear, national deadline before taking action. This is a dangerous strategy. Enforcement is happening state by state, and by the time a national deadline is formally announced, the hospitals that waited will face a bottleneck — every testing agency, security auditor, and integration partner will be overwhelmed with last-minute requests. The hospitals that started early will already be compliant and operating normally.
Frequently Asked Questions
Is ABDM compliance legally mandatory for all AB-PMJAY hospitals in 2026?
State-level enforcement has begun, with Bihar leading the way. While a single national deadline has not been published, the NHA has made clear that ABDM integration is a condition of continued AB-PMJAY empanelment. The direction is unambiguous: compliance is mandatory, and enforcement is being rolled out state by state. Hospitals should treat this as a when-not-if scenario and begin preparation immediately.
What happens if our hospital software vendor does not support ABDM?
If your current HIS/EHR vendor cannot support ABDM integration, you have two options: switch to a vendor whose product is ABDM-certified, or adopt a middleware solution that adds an ABDM layer on top of your existing system. The middleware approach is often preferred because it avoids the disruption and cost of a full system replacement. However, you should have a serious conversation with your current vendor about their ABDM roadmap — if they have no plans for ABDM support, that is a strategic risk for your hospital.
How much time does it realistically take to become ABDM-compliant from scratch?
For a hospital with existing digital infrastructure (a functioning HIS with structured data), the realistic timeline is 3–6 months from start to production go-live. This includes implementation of M1, M2, and M3, followed by functional testing, security audit, and NHA approval. For hospitals starting from paper-based or very basic digital systems, the timeline extends to 6–12 months because foundational digitization work must happen first. These are ranges — actual timelines depend on system complexity, data quality, and the chosen integration approach.
Can we achieve compliance without replacing our existing Hospital Information System?
Yes. This is the most common approach, especially for hospitals that have invested significantly in their current systems and do not want to disrupt established clinical workflows. A middleware solution integrates with your existing HIS, LIMS, RIS, and pharmacy systems via APIs or database connections, handles the FHIR R4 data conversion, manages consent artifacts, and communicates with the ABDM network on your behalf. Your staff continues using the systems they are familiar with while the middleware handles compliance behind the scenes.
What are the ongoing obligations after achieving ABDM compliance?
ABDM compliance is not a one-time event. After going live, your hospital must continue to: (1) create and link ABHA numbers for every new patient, (2) generate and share health records for every episode of care, (3) respond to consent requests from other providers and patients, (4) keep your systems updated as ABDM APIs evolve (version upgrades, new features), and (5) maintain security standards and pass periodic audits. This is an ongoing operational commitment that requires dedicated processes and, ideally, automated systems to handle the volume.
The Bottom Line
ABDM compliance for AB-PMJAY hospitals is not a future consideration — it is a present requirement. The states are enforcing. The penalties are real. And the hospitals that act now will not only avoid penalties but will also be better positioned to deliver higher quality care through interoperable digital health records.
The question is not whether to comply, but how fast you can get there.
Whether you are a hospital evaluating compliance options or a health-tech vendor preparing your platform, our team can help you navigate ABDM integration from assessment to go-live. Talk to us →