Healthcare integration projects fail at a rate that would be unacceptable in any other engineering discipline. After building and rescuing integration implementations across 30+ health systems, we have cataloged the patterns that predict failure — and most of them happen before a single line of code is written.
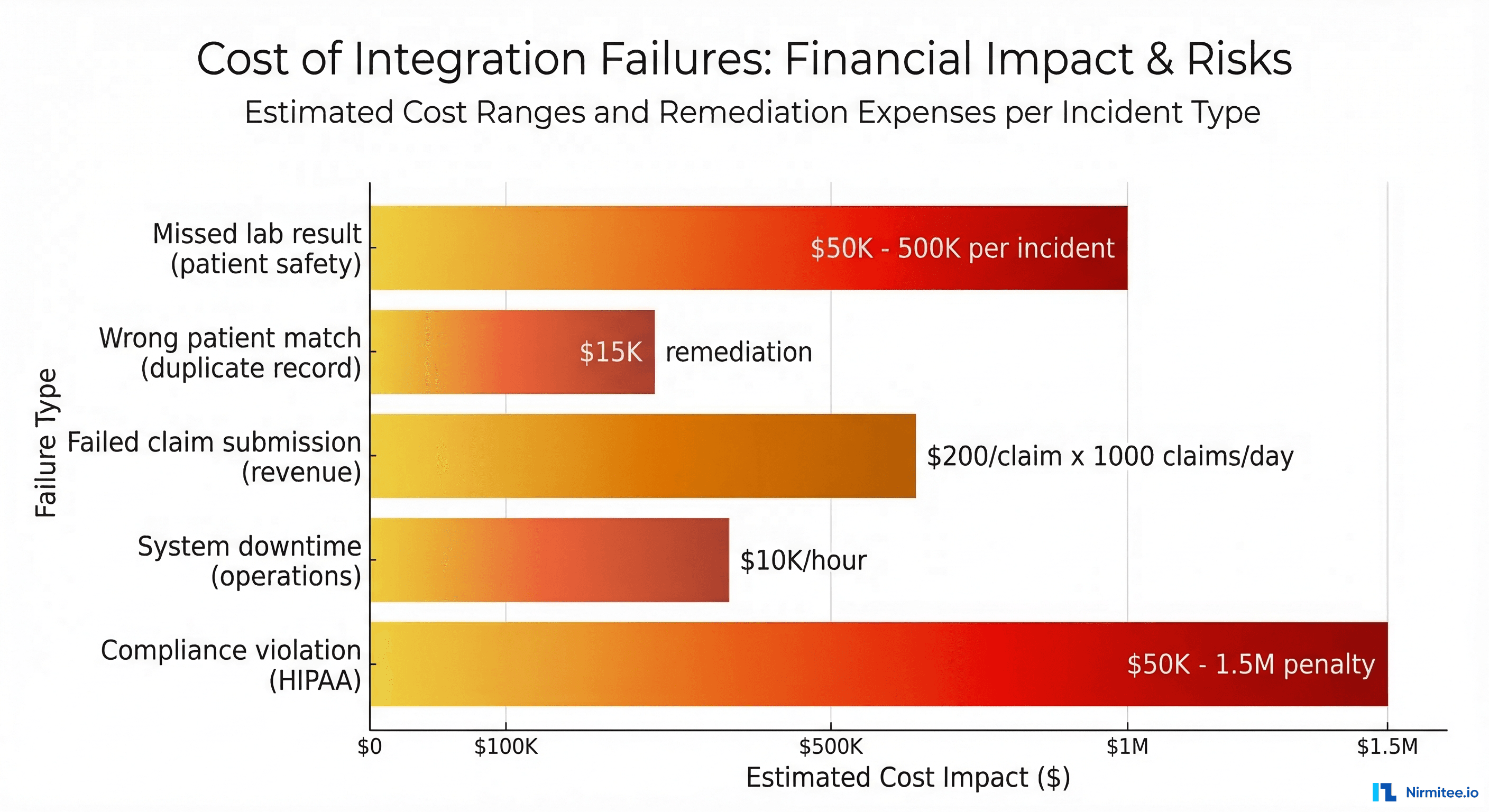
The consequences of integration failures in healthcare are not abstract. A dropped ADT message means a patient arrives at radiology and nobody knows they were admitted. A malformed ORU result means a critical lab value never reaches the ordering physician. A failed claim submission means revenue sits uncollected for months. According to a 2024 Ponemon Institute study, the average cost of a healthcare IT system failure is ,662 per minute — and integration failures are the leading cause of unplanned system downtime.
These seven mistakes are the ones we see most frequently. None of them are exotic technical failures. They are organizational, architectural, and process failures that compound into technical debt that becomes progressively harder to unwind.
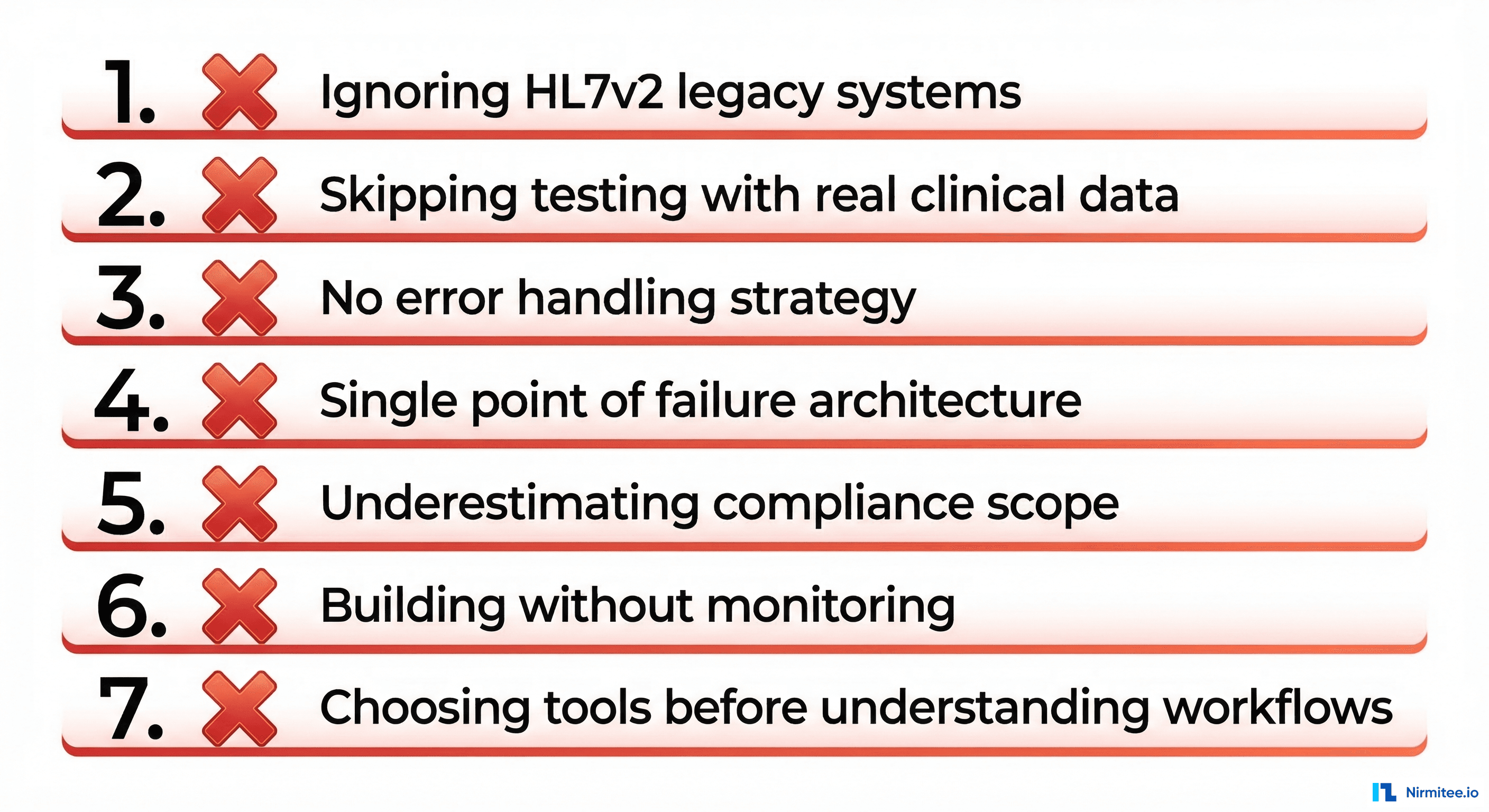
Mistake 1 — Treating Integration as an Afterthought
The most damaging mistake happens before the project starts: treating integration as a Phase 2 concern. Product teams build features for 6 months, then hand the integration requirement to a separate team with a 4-week deadline. By that point, the data model assumptions baked into the product are incompatible with the HL7v2 messages the hospital actually sends.
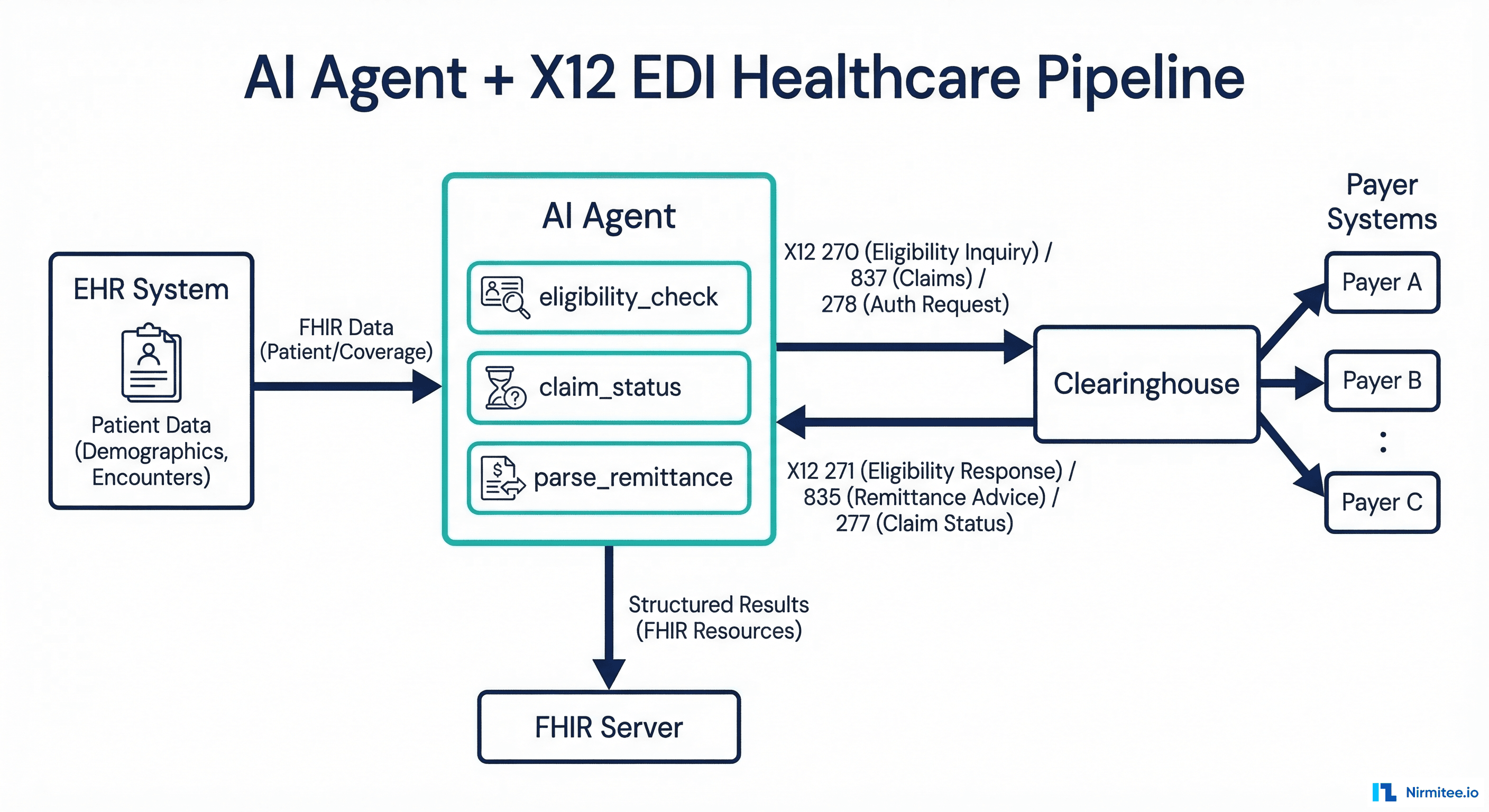
A real example: a telehealth startup built a patient intake form that collected insurance information as free text. When they integrated with a health system's eligibility checking API (X12 270/271), they discovered the payer requires structured data — specific fields for subscriber ID, group number, payer ID, and plan type. Retrofitting the product to collect structured data required redesigning 3 screens and migrating 40,000 existing records.
Integration architecture decisions — which standards to support, how data flows between systems, what identifiers to use — must be made in the first two weeks of a project, not the last two. At minimum, answer these questions before writing code: What EHR systems will this connect to? What message types will we receive and send? What patient identification strategy will we use?
Mistake 2 — Point-to-Point Architecture That Cannot Scale
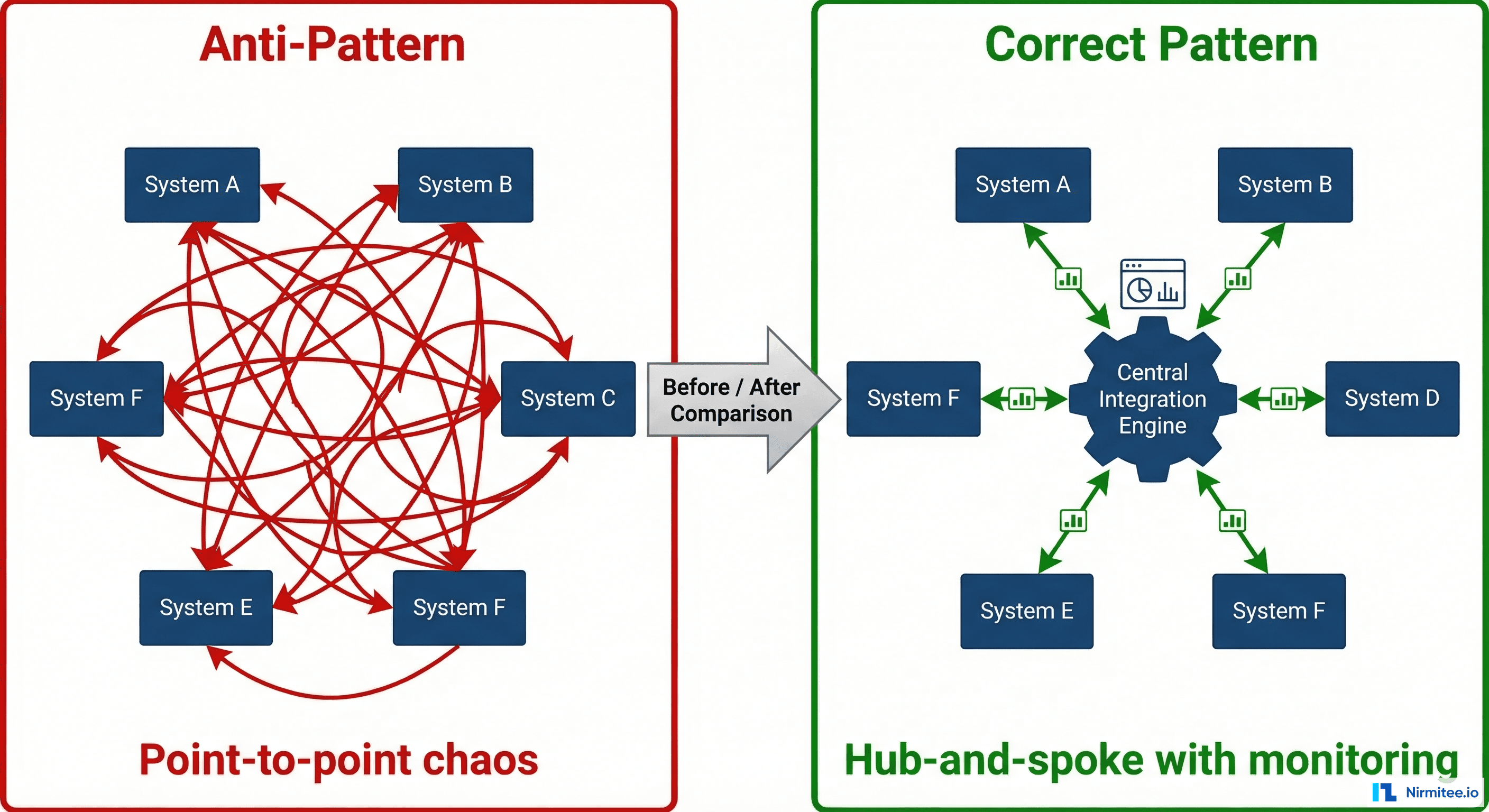
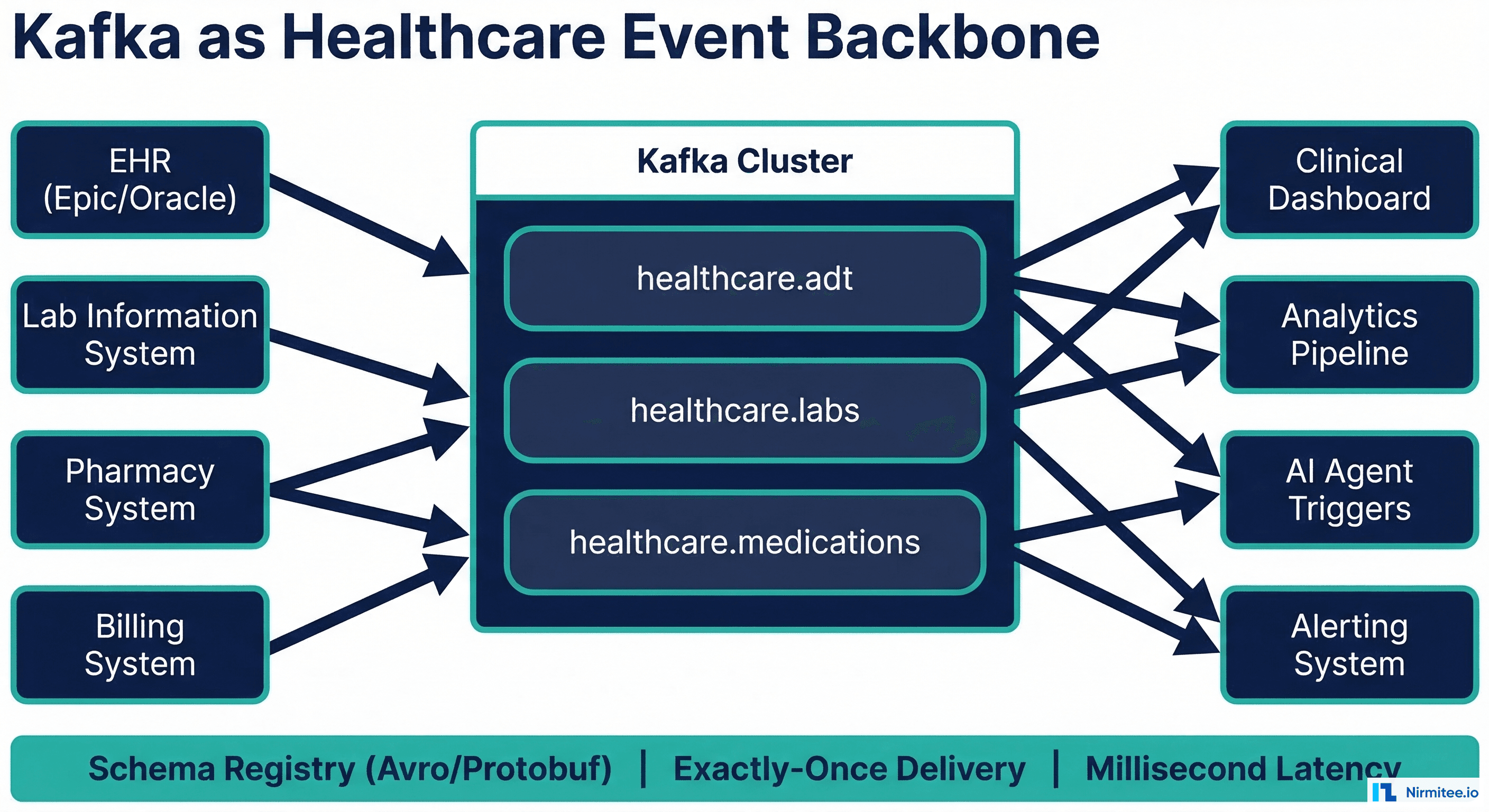
When the first integration is EHR-to-lab, the simplest approach is a direct connection. When the second is EHR-to-pharmacy, another direct connection seems reasonable. By the time you have 8 systems, you are managing 28 point-to-point interfaces (n*(n-1)/2), each with its own mapping logic, error handling, and monitoring.
We inherited a system at a 400-bed hospital that had 47 point-to-point interfaces. When the lab system upgraded from HL7 v2.3 to v2.5.1, 11 interfaces broke because each one had its own hardcoded parser for the lab's specific message format. The upgrade took 4 months instead of 2 weeks because every interface needed individual modification and testing.
An integration engine like Mirth Connect centralizes transformation logic. When the lab upgrades, you update one inbound channel — not 11 interfaces. The upfront investment in a hub-and-spoke architecture pays for itself within the first 6 months of operation.
Mistake 3 — Ignoring HL7v2 While Chasing FHIR
FHIR R4 is the future. HL7v2 is the present. Over 95% of clinical messaging in US hospitals still uses HL7v2 for ADT notifications, lab results (ORU), orders (ORM), and scheduling (SIU). Building an integration layer that only supports FHIR means ignoring 95% of the data that actually flows through a hospital.
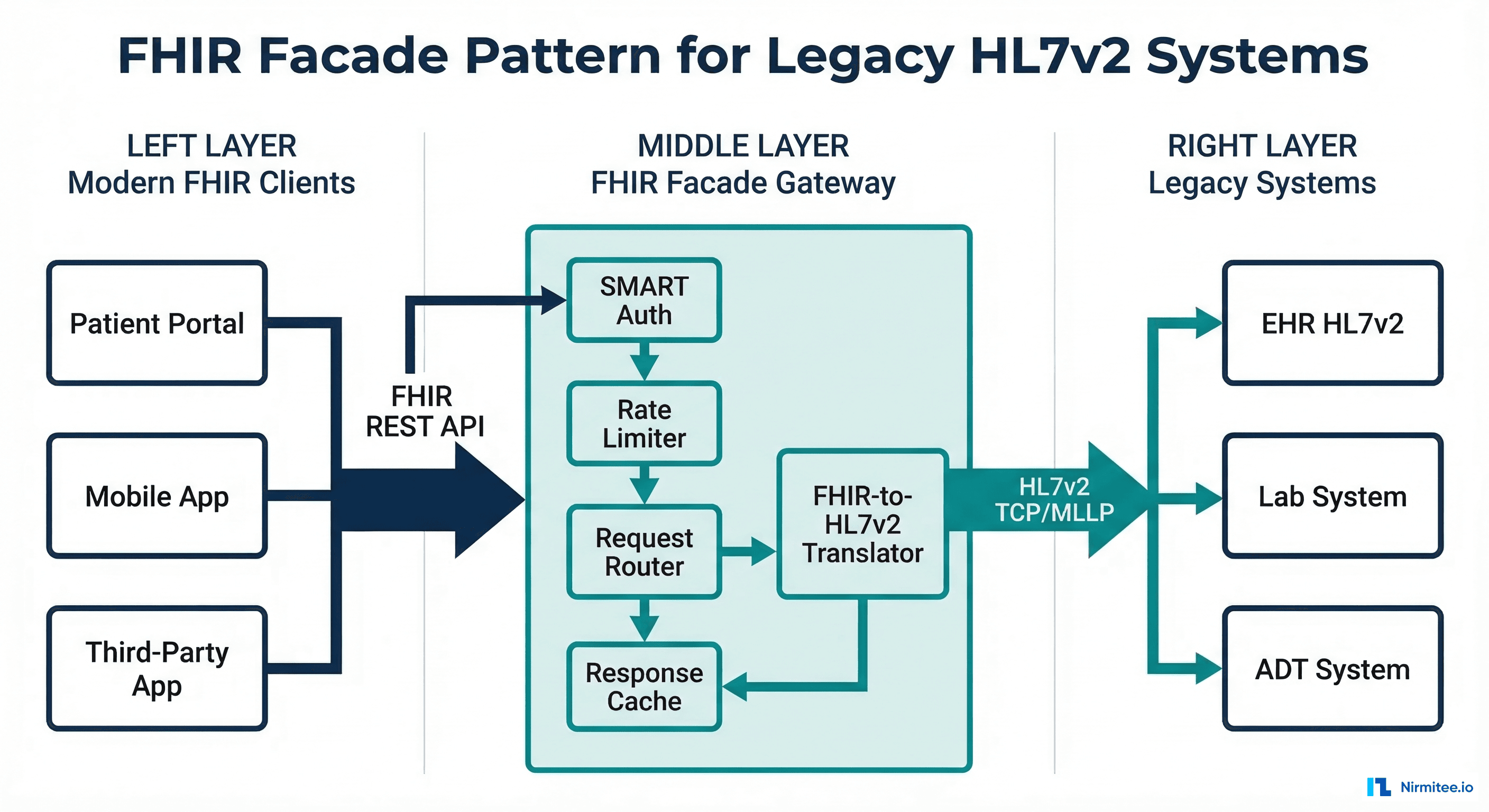
The practical approach is a dual-standard architecture: accept HL7v2 from legacy systems, transform to FHIR internally, and expose FHIR APIs for new applications. This requires understanding both standards deeply enough to build accurate V2-to-FHIR mappings — which is harder than it sounds because V2 is wildly inconsistent across implementations.
Mistake 4 — No Error Handling Strategy
Messages fail. Systems go down. Networks partition. Data arrives malformed. The question is not whether failures will happen — it is whether your system handles them gracefully or silently drops data.
The most dangerous failure mode is the silent one: a message is received, parsing fails on a non-critical segment, and the system logs a warning that nobody monitors. Meanwhile, the patient's allergy information — which was in the segment that failed to parse — never reaches the downstream system. Two weeks later, a pharmacist fills a prescription without seeing the allergy flag.
Every integration channel needs: a dead letter queue for messages that cannot be processed, automatic retry with exponential backoff for transient failures, alerting that escalates based on failure volume and duration, and a reconciliation process that detects gaps in message sequences. Building these patterns into Mirth Connect from day one prevents the silent failures that create patient safety risks.
Mistake 5 — Testing with Synthetic Data Only
Unit tests with synthetic HL7v2 messages are necessary but insufficient. Real clinical messages contain edge cases that synthetic data generators never produce: segments in unexpected order, fields populated with values outside the defined value set, timestamps in non-standard formats, and character encoding issues from systems that predate Unicode.
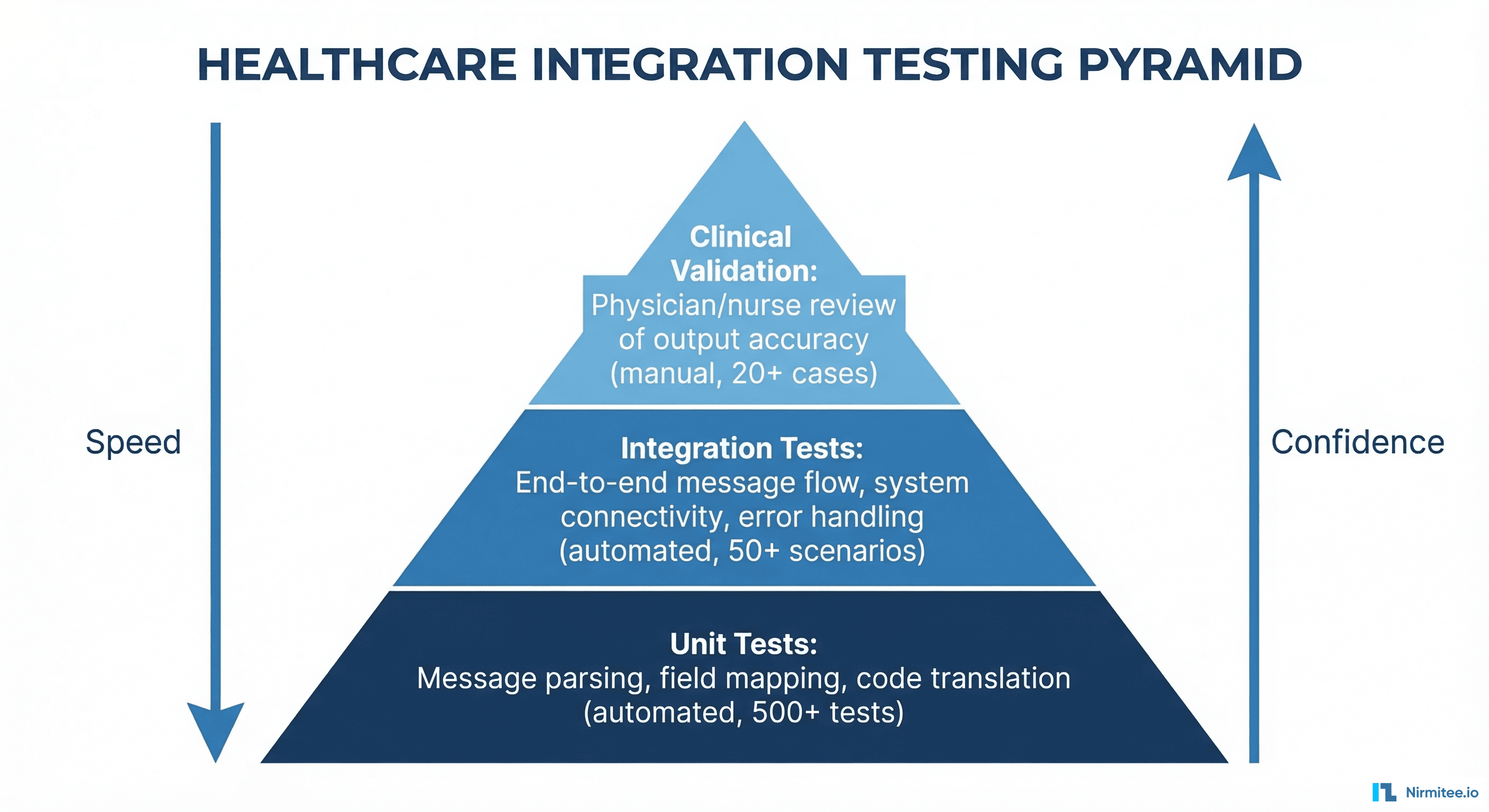
We recommend a three-level testing pyramid. Base level: automated unit tests with synthetic messages covering every field mapping (500+ test cases for a typical ADT channel). Middle level: integration tests using anonymized production message samples from the actual sending system (50+ scenarios covering message types, edge cases, and error conditions). Top level: clinical validation where a physician or nurse reviews 20+ output records to confirm clinical accuracy and completeness.
The middle level — testing with real (anonymized) messages — is where most teams skip, and where most production failures originate.
Mistake 6 — Building Without Monitoring
An integration engine processing 50,000 messages per day without monitoring is a liability, not an asset. When a downstream system stops accepting messages at 2am, you need to know within minutes — not when a clinician reports missing data the next morning.
Essential monitoring for healthcare integrations: message throughput per channel (with anomaly detection for sudden drops), error rate per channel with severity classification, end-to-end message latency (time from source system to final destination), queue depth (messages waiting to be processed — a growing queue means a system is falling behind), and compliance dashboard showing message delivery confirmation rates.
Monitoring is not a Phase 2 feature. Deploy it alongside your first integration channel.
Mistake 7 — Underestimating Compliance Requirements
Every healthcare integration processes Protected Health Information (PHI). HIPAA compliance is not a checkbox — it is an architectural requirement that affects how you log messages (PHI in logs must be encrypted or tokenized), how you handle errors (error queues containing PHI need the same access controls as production data), how you manage credentials (no hardcoded passwords in channel configurations), and how you audit access (who accessed which messages, when, and why).
The 21st Century Cures Act adds information blocking requirements: you must make clinical data available through standardized APIs within defined timeframes. Refusing to share data — even for technical reasons like "our API is down" — can result in penalties of up to 75% of Medicare payments.
Compliance is not something you bolt on after the integration works. The architecture decisions you make in week 1 (logging strategy, encryption approach, access control model) determine whether compliance is achievable or requires a rebuild.
Building interoperable healthcare systems is complex. Our Healthcare Interoperability Solutions team has deep experience shipping production integrations. We also offer specialized Custom Healthcare Software Development services. Talk to our team to get started.
Frequently Asked Questions
What is the most common cause of healthcare integration project failure?
Treating integration as an afterthought. When integration requirements are discovered late in the development cycle, the product architecture often cannot accommodate them without significant rework. Early integration planning — in the first 2 weeks of any healthcare project — prevents the most expensive failures.
How long should a typical healthcare integration take to implement?
A single HL7v2 interface (e.g., ADT from Epic to a downstream system): 4-8 weeks including testing and go-live. A FHIR API integration with a major EHR: 6-12 weeks including SMART on FHIR authentication, scope negotiation, and vendor approval. A full integration platform deployment with 20+ interfaces: 6-12 months.
Do we need a dedicated integration team?
For organizations with more than 10 active interfaces: yes. Healthcare integration requires a specific skill set — HL7 parsing, clinical workflow understanding, database administration, and network engineering — that is difficult to develop as a side responsibility. A dedicated team of 2-3 integration engineers can manage 30-50 interfaces effectively.
Healthcare integration is not a solved problem — it is an ongoing engineering discipline. At Nirmitee, we have built, rescued, and scaled integration platforms for health systems and healthtech companies across Mirth Connect, FHIR-native architectures, and custom builds. If your integration layer is a source of pain instead of progress, talk to our team.