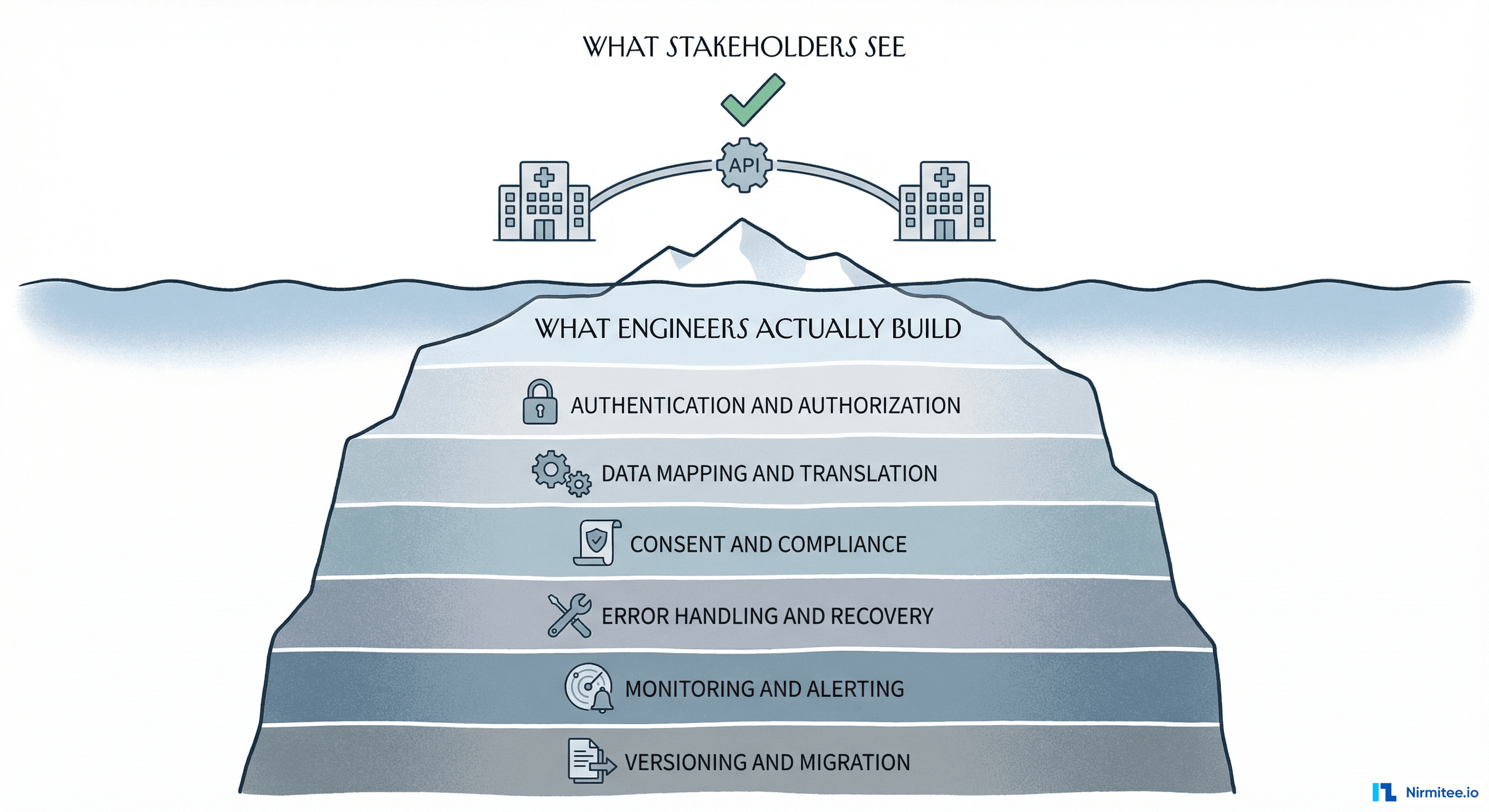
Every healthcare integration project starts the same way. Someone says: We just need to connect System A to System B. A product manager draws two boxes and an arrow on a whiteboard. Engineering estimates two sprints. Six months later, the team is drowning in HL7v2 message parsing, FHIR resource mapping, consent edge cases, and an error queue that grows faster than anyone can debug.
The problem is not that healthcare integrations are hard. The problem is that most teams do not have a mental model for thinking about them. They jump straight into the technical details — which API, which standard, which vendor — without first understanding the fundamental forces that make healthcare integrations different from any other kind of software integration.
At Nirmitee.io, we have built dozens of healthcare integrations across EHR systems, claims processors, lab networks, pharmacy platforms, and national health exchanges (ABDM in India, FHIR-based systems in the US). This article is the mental model we use internally — the framework that helps us estimate accurately, architect correctly, and avoid the traps that catch most teams.
Why Healthcare Integration Is Different
If you have built integrations in fintech, e-commerce, or SaaS, you might think healthcare is just another domain. It is not. Four forces make healthcare integration fundamentally different:
1. Regulated Data, Not Just Sensitive Data
Every other industry has sensitive data. Healthcare has regulated data. HIPAA, HITECH, state privacy laws, and 42 CFR Part 2 (substance abuse records) do not just say protect this data — they prescribe how you must protect it, who can access it, what you must log, and how long you must retain audit trails. A data breach in e-commerce costs money. A data breach in healthcare costs money AND triggers mandatory government reporting, potential criminal liability, and loss of the ability to operate.
2. Standards That Predate the Web
HL7v2 was designed in 1987 — two years before the World Wide Web was invented. It uses pipe-delimited segments, has 500+ message types, and every hospital implements it differently. FHIR was designed in 2014 and uses modern REST APIs with JSON. Most healthcare organizations run both simultaneously. Your integration must speak both languages.
3. No Universal Patient Identity
In the US, there is no national patient identifier. When a patient visits Hospital A and then Hospital B, there is no guaranteed way to link their records. Patient matching relies on probabilistic algorithms using name, date of birth, address, and SSN fragments — with documented error rates of 7-20%. Every integration that touches patient data must handle this ambiguity.
4. Life-Safety Consequences
A bug in an e-commerce integration means someone gets the wrong product. A bug in a healthcare integration can mean a patient gets the wrong medication, a critical lab result is lost, or an allergic reaction is not flagged. The error tolerance is fundamentally different. You cannot move fast and break things when things are people.
The Standards Landscape: A Map, Not a List
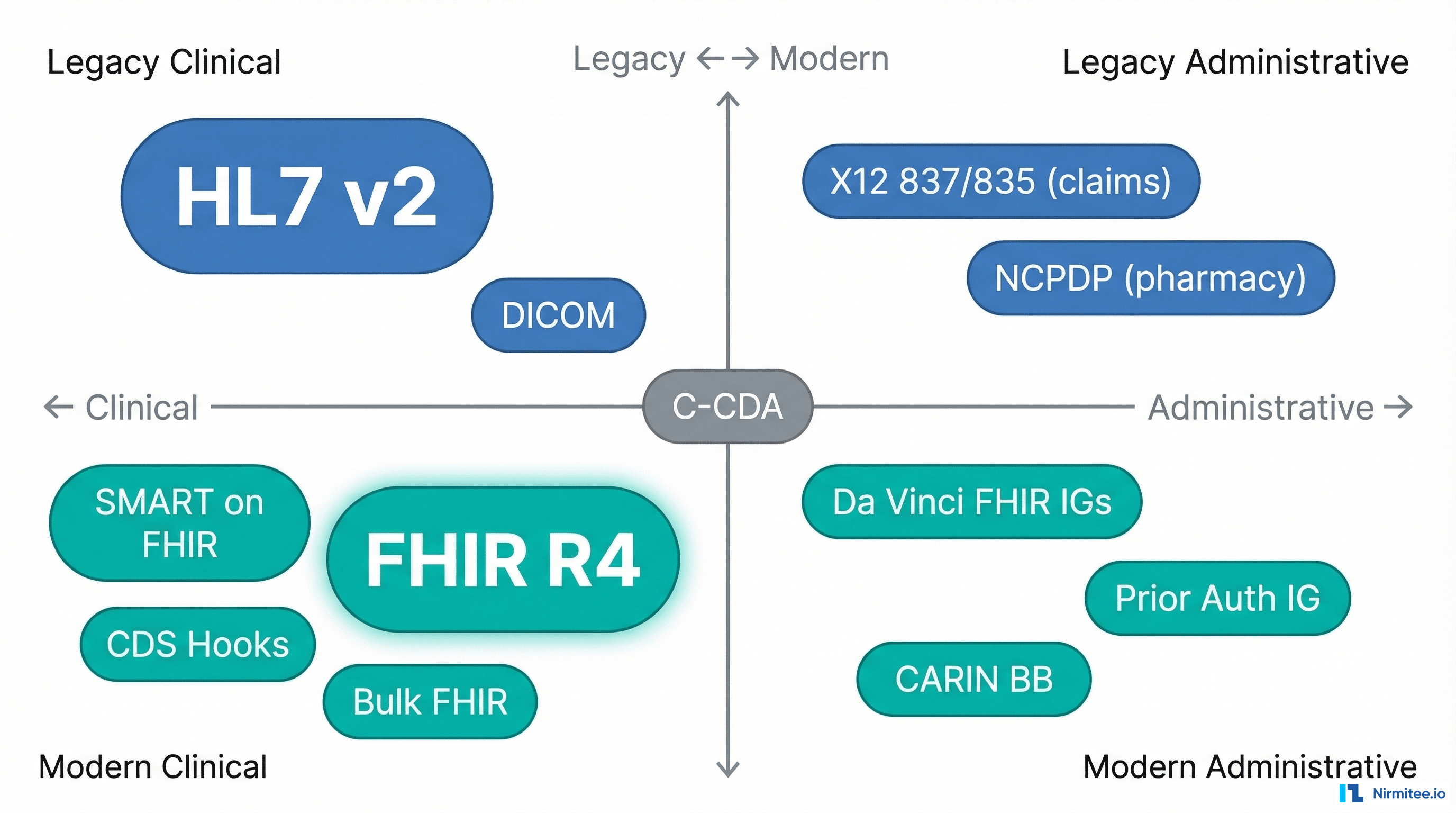
Most articles about healthcare integration give you a list of standards. A list does not help you make decisions. A map does. Here is how to think about the standards landscape along two axes:
Axis 1: Clinical vs. Administrative. Clinical standards handle patient health data — diagnoses, medications, lab results, clinical notes. Administrative standards handle the business of healthcare — insurance claims, eligibility verification, prior authorization, payment remittance.
Axis 2: Legacy vs. Modern. Legacy standards were designed before the web and use custom protocols. Modern standards use REST APIs, JSON, and OAuth 2.0.
What you will actually encounter:
- HL7v2 (1987) — still the dominant standard for real-time clinical data exchange inside hospitals. ADT messages (patient admit/discharge/transfer), ORM/ORU (orders and results), and SIU (scheduling). Uses MLLP (Minimal Lower Layer Protocol) for transport. Every hospital has slightly different message profiles.
- FHIR R4 (2019) — the modern standard. RESTful APIs, JSON resources (Patient, Observation, MedicationRequest, Encounter). Increasingly mandated for external-facing APIs. Epic, Cerner, and other major EHRs expose FHIR endpoints.
- C-CDA (2012) — XML-based clinical document format. Used for care summaries, discharge documents, and transitions of care. Think of it as the PDF of healthcare — widely exchanged but painful to parse programmatically.
- X12 837/835 — EDI transactions for insurance claims (837 = claim submission, 835 = payment remittance). Flat-file format with strict segment rules. Used by every payer in the US.
- NCPDP SCRIPT — the standard for electronic prescribing. Used for new prescriptions, refill requests, and medication history between pharmacies and prescribers.
- DICOM — the standard for medical imaging. CT scans, MRIs, X-rays. Binary format with metadata headers. Typically exchanged via DICOM networking protocols, not REST APIs.
The key insight: you will rarely use just one standard. A single integration — say, connecting a telehealth platform to a hospital EHR — might require FHIR for patient demographics, HL7v2 for real-time ADT feeds, C-CDA for care summaries, and X12 for insurance eligibility checks. The mental model must accommodate this reality.
The Five-Layer Mental Model
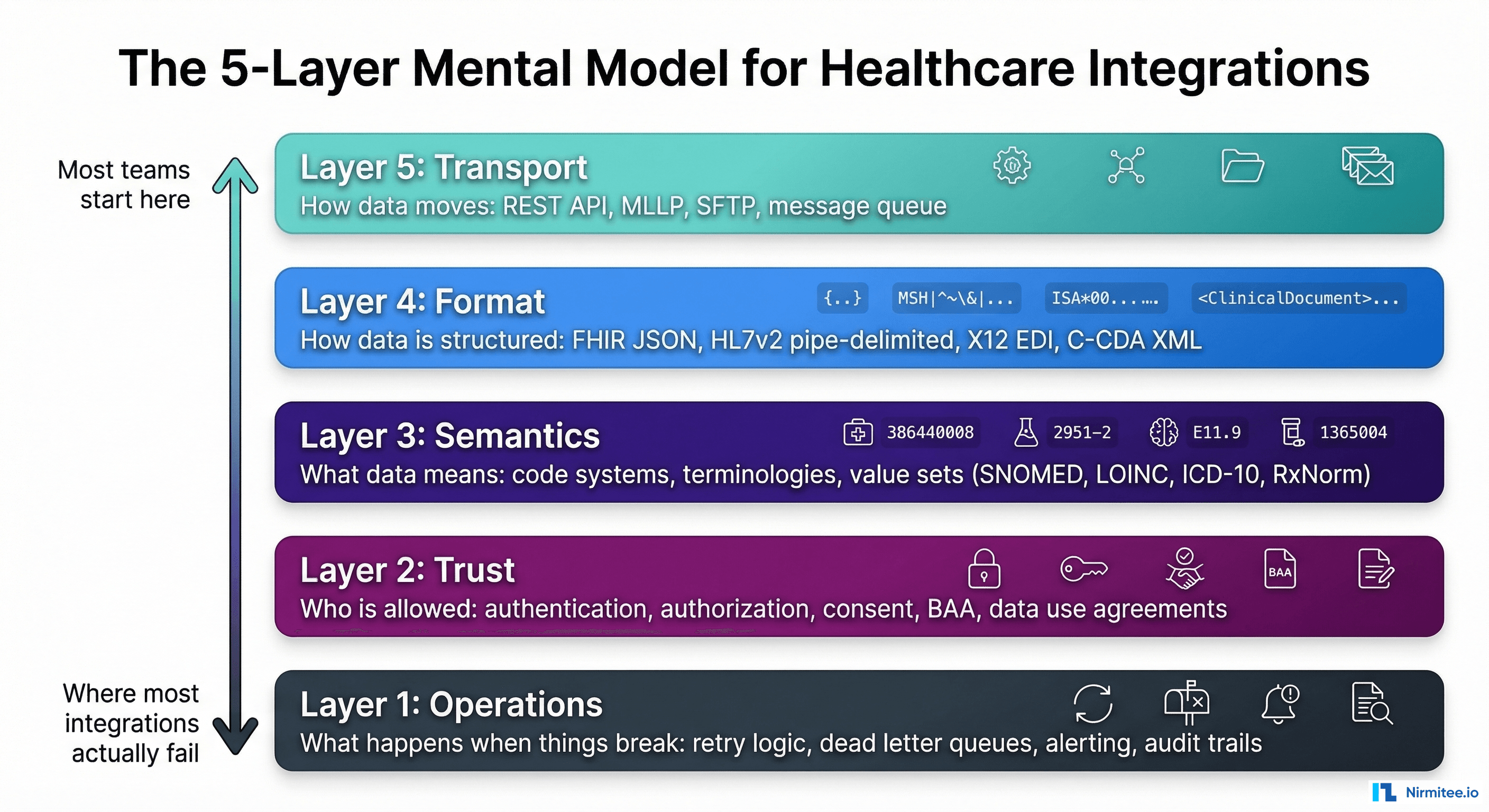
Every healthcare integration, regardless of the specific systems involved, has five layers. When teams struggle, it is almost always because they conflated layers or skipped one entirely.
Layer 1: Transport — How Data Moves
This is the layer most teams start with, and it is usually the simplest to solve.
- REST APIs (HTTPS) — for FHIR and modern integrations. Standard TLS, OAuth 2.0, JSON payloads.
- MLLP (Minimal Lower Layer Protocol) — for HL7v2. A thin TCP wrapper that adds header/trailer bytes. Usually runs on a dedicated port behind a VPN.
- SFTP — for batch file exchanges (claims, eligibility files, bulk data). Still widely used for payer integrations.
- Message queues — Kafka, RabbitMQ, or cloud equivalents for event-driven integrations. Increasingly used for real-time clinical event streaming.
- Direct (Direct Secure Messaging) — a healthcare-specific secure email protocol used for exchanging C-CDA documents between providers.
Common mistake: Choosing transport before understanding the other four layers. A team picks REST because it is modern, then discovers the source system only speaks HL7v2 over MLLP, requiring an integration engine in the middle.
Layer 2: Format — How Data Is Structured
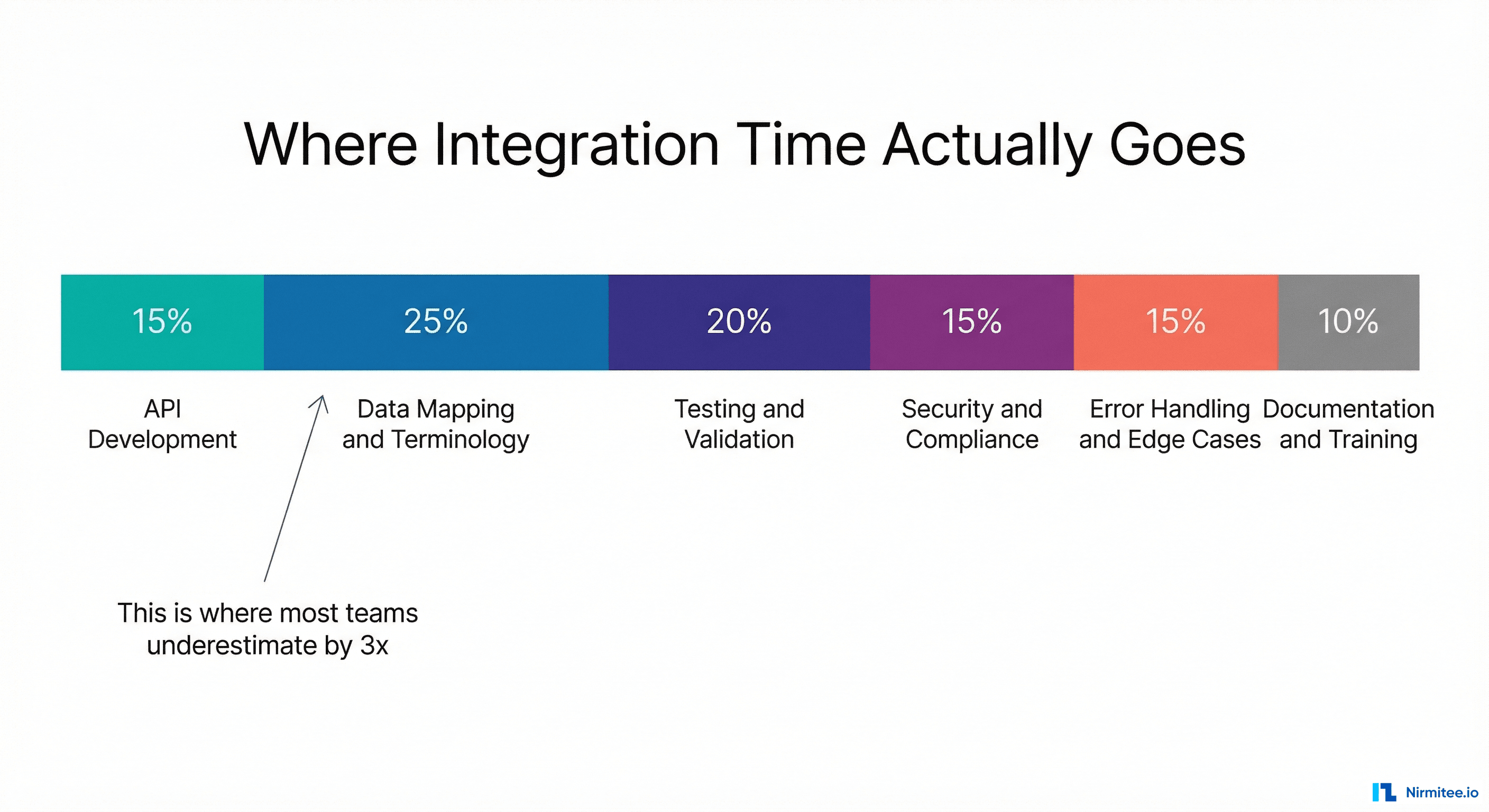
Format is where most teams spend the majority of their time — and underestimate by 3x.
The same clinical concept — a patient's blood pressure reading — is represented completely differently in each format:
- FHIR: An
Observationresource withcode.coding[0].code = "85354-9"(LOINC),component[0]for systolic,component[1]for diastolic, each withvalueQuantityin mmHg. - HL7v2: An OBX segment:
OBX|1|NM|85354-9^Blood pressure^LN||120/80|mmHg|||||F - C-CDA: A
<observation>element nested inside a<section>with template IDs, coded entries, and value elements using XML namespaces.
Building the mapper between these formats is where most of the engineering effort goes. And it is not just structural translation — it is semantic translation, which brings us to Layer 3.
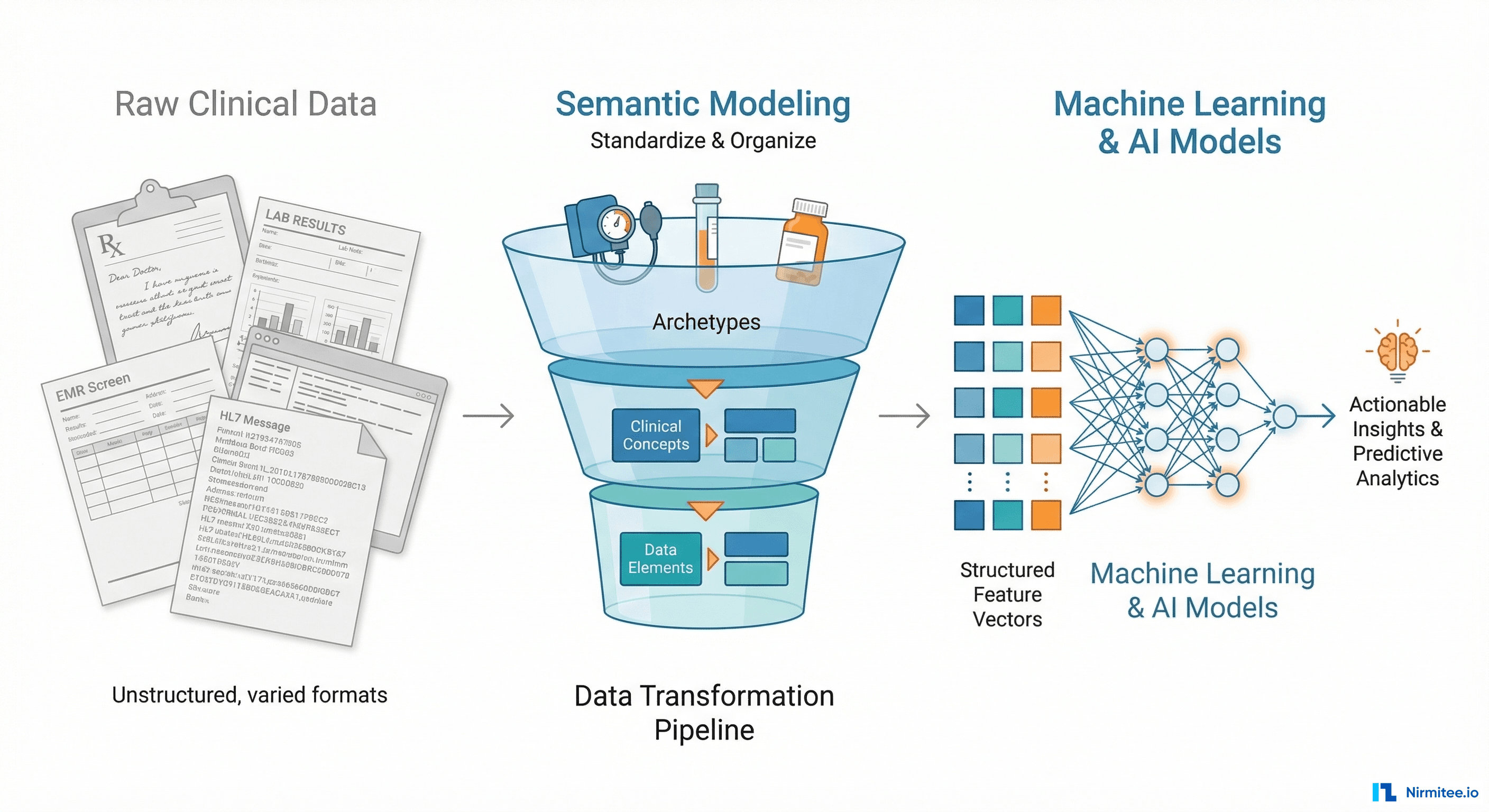
Layer 3: Semantics — What Data Means
This is the layer that separates experienced healthcare integration engineers from everyone else. Two systems can both use FHIR and still not understand each other if they use different code systems.
- SNOMED CT — clinical terminology for diagnoses, procedures, and clinical findings. 350,000+ concepts.
- ICD-10-CM — diagnosis codes used for billing. Required for insurance claims. 72,000+ codes.
- LOINC — laboratory and clinical observation codes. Used in lab results, vital signs, and clinical assessments.
- RxNorm — medication terminology. Maps between brand names, generic names, and ingredient-level representations.
- CPT — procedure codes used for billing. Owned by the AMA, requires a license.
The challenge: Hospital A might record a diagnosis as SNOMED code 73211009 (Diabetes mellitus). Hospital B might use ICD-10 code E11.9 (Type 2 diabetes mellitus without complications). These refer to the same condition but are different code systems with different granularity. Your integration must map between them — and the mapping is not always one-to-one.
The rule of thumb: if two systems use the same code system (both use LOINC for labs, for instance), the integration is dramatically simpler. If they use different code systems, budget 3x more time for terminology mapping.
Layer 4: Trust — Who Is Allowed
In most software integrations, trust means authentication and authorization. In healthcare, trust is a multi-dimensional problem:
- System authentication — is this application who it claims to be? (OAuth 2.0 client credentials, mutual TLS, API keys)
- User authorization — does this specific user have permission to access this specific patient's data? (SMART on FHIR scopes, role-based access control)
- Patient consent — has the patient authorized this data sharing? (Consent directives, opt-in/opt-out, granular vs. broad consent)
- Legal agreements — is there a BAA (Business Associate Agreement) in place? Data Use Agreement? Are the permitted purposes documented?
- Regulatory compliance — does this exchange comply with HIPAA minimum necessary standard? Are substance abuse records (42 CFR Part 2) properly segmented?
Common mistake: Treating trust as a one-time setup. In reality, consent can be revoked, BAAs expire, and regulatory requirements change. The integration must handle trust as an ongoing, dynamic layer — not a checkbox during onboarding.
Layer 5: Operations — What Happens When Things Break
This is the layer most teams think about last and regret first. Healthcare integrations fail in production. Networks go down. Interfaces return malformed data. Certificate rotations happen at 2 AM on a Saturday.
- Retry and idempotency — if a message fails, can you safely retry? Is the receiving system idempotent, or will a retry create a duplicate order?
- Dead letter queues — messages that fail validation or processing must go somewhere. You need a queue, a dashboard, and a workflow for human review.
- Monitoring and alerting — not just is the interface up but is data flowing at the expected volume? A lab interface that normally sends 200 results per hour and suddenly drops to zero is a critical issue even if the connection is healthy.
- Audit trails — HIPAA requires logging of who accessed what data, when, and for what purpose. Every data exchange must be auditable.
- Versioning and migration — what happens when the source system upgrades from HL7v2 to FHIR? Or updates their FHIR implementation guide? The integration must handle version transitions gracefully.
The hard truth: the majority of integration failures happen at Layer 4 (trust) and Layer 5 (operations), but the majority of engineering time is spent at Layer 2 (format) and Layer 3 (semantics). The mental model helps you allocate attention where failures actually occur.
Four Integration Patterns and When to Use Each
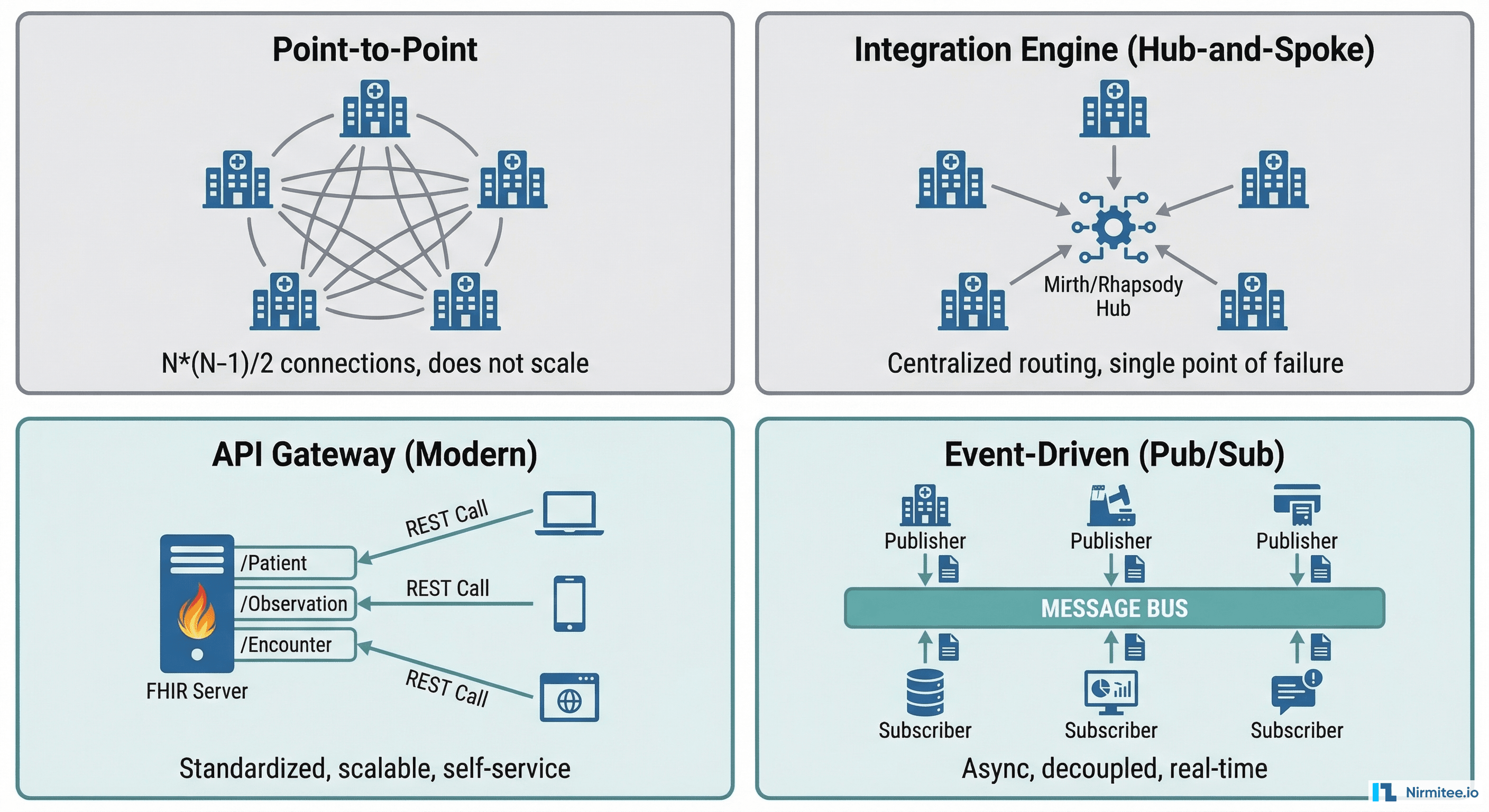
Pattern 1: Point-to-Point
What it is: System A connects directly to System B with a custom interface.
When to use: Exactly one integration between two systems, with no expectation of adding more. A radiology PACS connecting to one specific EHR.
Why it breaks: The number of connections grows as N*(N-1)/2. Five systems need 10 connections. Ten systems need 45. Twenty systems need 190. The complexity becomes unmanageable fast.
Pattern 2: Integration Engine (Hub-and-Spoke)
What it is: A central engine (Mirth Connect, Rhapsody, InterSystems HealthShare) routes and transforms messages between systems.
When to use: Multiple HL7v2 interfaces within a hospital or health system. Batch file processing. Legacy system connectivity where you need protocol and format translation.
Strengths: Centralized message routing, built-in HL7v2 parsing, visual message mapping, good for operations teams familiar with healthcare integration engines.
Limitation: Single point of failure. The engine becomes critical infrastructure. If Mirth goes down, every interface goes down.
Pattern 3: API Gateway (Modern)
What it is: A FHIR server or API gateway exposes standardized endpoints. Consuming systems connect via REST APIs with OAuth 2.0.
When to use: External-facing integrations. Patient-facing applications. Third-party developer access. Any new integration where you can mandate FHIR.
Strengths: Self-service onboarding, standardized contracts, scalable, developer-friendly. This is where healthcare is heading.
Limitation: Requires both sides to support FHIR. If the source system only speaks HL7v2, you still need an engine or adapter in the middle.
Pattern 4: Event-Driven (Pub/Sub)
What it is: Systems publish events to a message bus (Kafka, cloud pub/sub). Consumers subscribe to events they care about.
When to use: Real-time clinical event streaming. Notifying multiple downstream systems when a patient is admitted, a lab result is finalized, or a medication is prescribed. Analytics and population health platforms that need a stream of clinical events.
Strengths: Decoupled systems, natural scalability, supports multiple consumers without modifying the publisher. Enables event sourcing for audit trails.
Limitation: Eventual consistency. Not appropriate for synchronous request/response patterns (like real-time eligibility checks). Requires operational maturity in message broker management.
The Decision Matrix: Choosing Your Approach
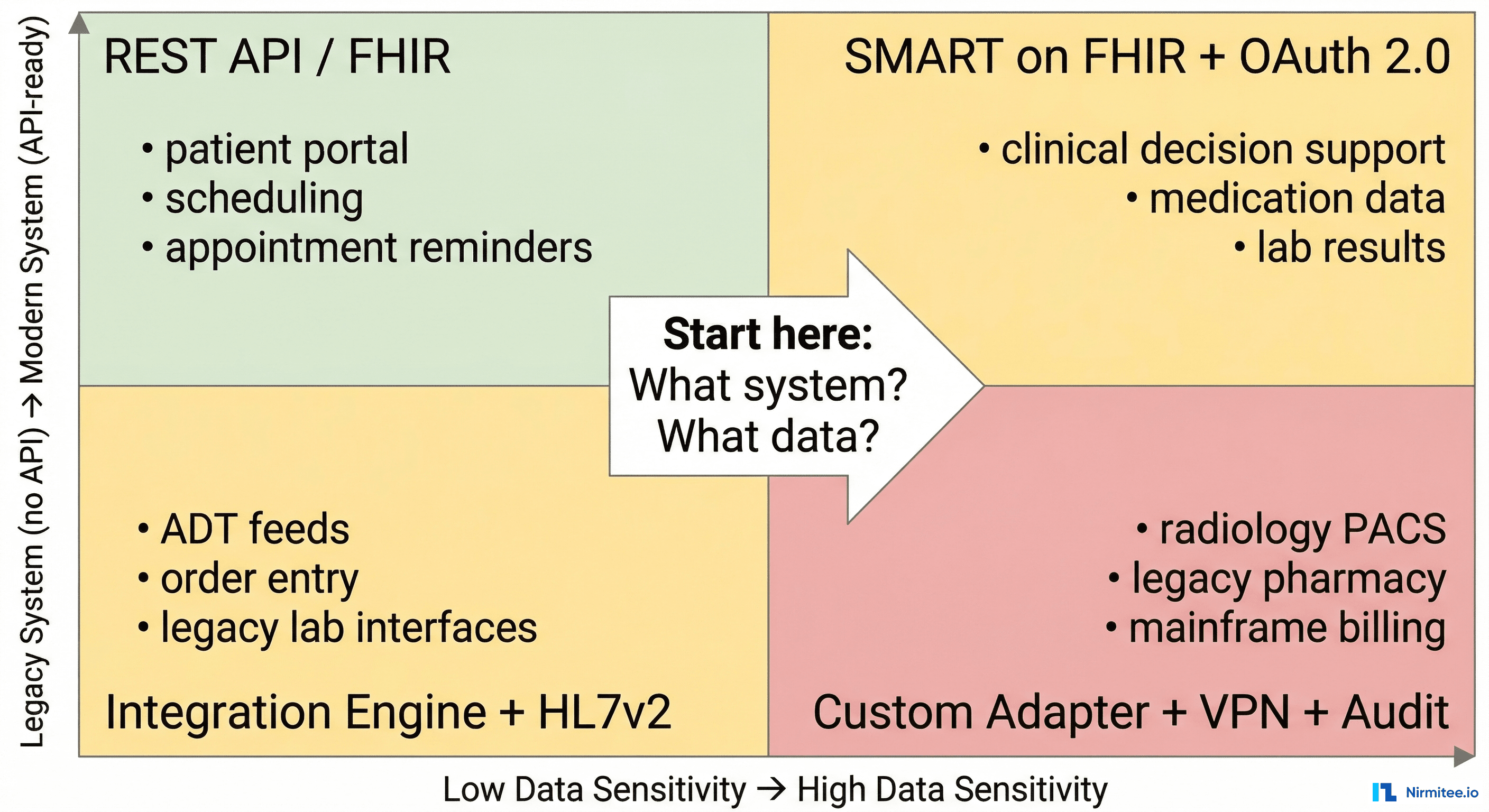
When a new integration request arrives, run it through two questions:
- What is the data sensitivity? Low sensitivity (scheduling, appointment reminders) requires simpler trust mechanisms. High sensitivity (medications, diagnoses, substance abuse records) requires granular consent, encryption, and audit trails.
- What is the system modernity? A modern system with FHIR APIs is fundamentally different to integrate with than a legacy system that only speaks HL7v2 over MLLP behind a hospital VPN.
The intersection of these two dimensions tells you which pattern, which standards, and roughly how much effort to expect:
- Modern + Low Sensitivity: REST API with API key or basic OAuth. Two-week project. Example: appointment scheduling integration.
- Modern + High Sensitivity: SMART on FHIR with granular OAuth scopes, patient consent, and HIPAA audit logging. Six-week project. Example: clinical decision support pulling medication data.
- Legacy + Low Sensitivity: Integration engine with HL7v2 ADT feeds. Four-week project. Example: patient admit/discharge notifications to a bed management system.
- Legacy + High Sensitivity: Custom adapter with VPN, message encryption, integration engine, terminology mapping, and full audit trail. Twelve-plus week project. Example: connecting a legacy pharmacy system to exchange medication records.
The Integration Maturity Ladder
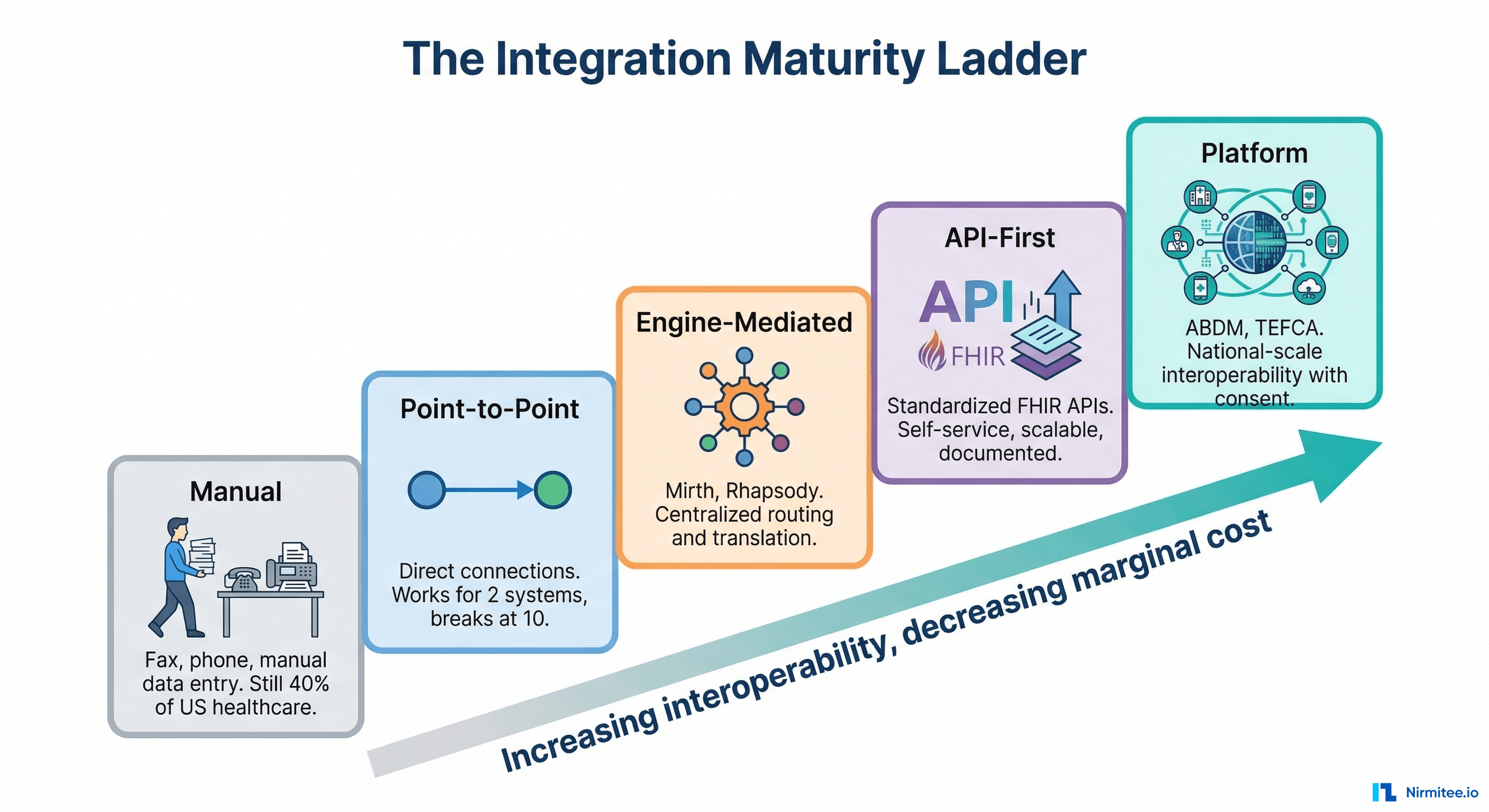
Healthcare organizations sit at different levels of integration maturity. Understanding where you are — and where you are going — prevents over-engineering and under-engineering:
- Manual (Fax and Phone). Still 40% of US healthcare data exchange. A referral is faxed. A lab result is called in. Data is manually re-entered into the EHR. Error-prone, slow, but requires zero technical infrastructure.
- Point-to-Point. Direct connections between specific systems. Works for 2-3 integrations. Becomes unmaintainable beyond that. Most small practices are here.
- Engine-Mediated. A central integration engine (Mirth, Rhapsody) routes and transforms messages. Most mid-size hospitals operate at this level. Good operational tooling, but the engine becomes a bottleneck.
- API-First. Standardized FHIR APIs with OAuth 2.0, developer documentation, and self-service onboarding. Large health systems and EHR vendors are moving here. This is where the industry needs to be.
- Platform. National-scale interoperability with identity, consent, and exchange built into the platform. India's ABDM operates here. TEFCA is attempting to reach this level in the US. This is the end state — but most organizations will not reach it directly. They will climb through the intermediate levels.
The key insight: do not try to jump from Level 1 to Level 5. Each level builds capabilities that the next level depends on. An organization that has never managed an integration engine is not ready for API-first architecture. Meet teams where they are and help them climb one level at a time.
Seven Rules We Follow on Every Integration
After building healthcare integrations across two countries and multiple health systems, these are the rules Nirmitee.io follows on every project:
- Map all five layers before writing code. Spend the first week understanding transport, format, semantics, trust, and operations. The cheapest bugs to fix are the ones you find on a whiteboard.
- Start with the error path. Before building the happy path, design what happens when a message fails. Dead letter queue? Retry with backoff? Alert to on-call? If you cannot answer these questions, you are not ready to build.
- Never trust the spec. Every HL7v2 implementation is a snowflake. The vendor says they send ADT-A01 messages per the standard. They do not. Get sample messages from the actual production system and validate every field.
- Test with real volume. An integration that works with 10 messages per minute may fail at 1,000. Healthcare systems have peak loads (Monday morning lab results, end-of-day batch processing). Load test at 3x expected peak volume.
- Log everything, expose nothing. Every message must be logged for audit purposes. But log the metadata (message ID, timestamp, patient MRN hash, status) — not the clinical content. Audit trails that contain PHI create more compliance risk than they solve.
- Version your interfaces. The source system will upgrade. The message format will change. A code system will add new values. Build versioning into your integration from day one — not as a retrofit when the first breaking change arrives.
- Own the monitoring story. Do not rely on the other system to tell you when things break. Monitor your side: message volume trends, error rates, latency percentiles, and data freshness. If your lab interface normally delivers results within 5 minutes and suddenly takes 2 hours, you should know before the clinicians do.
Build Integrations That Last
Healthcare integrations are not projects — they are products. They run for years, handle life-safety data, and must evolve as standards, regulations, and systems change around them. The mental model in this article — five layers, four patterns, a maturity ladder, and a decision matrix — is the framework that helps teams build integrations that survive contact with reality.
At Nirmitee.io, we bring this framework to every healthcare integration engagement. Whether you are connecting an EHR to a clinical trial platform, building ABDM-compliant health information exchange in India, or standing up FHIR APIs for a digital health startup, we have done it — in production, with real patient data, under real compliance requirements.
Starting a healthcare integration? Talk to our interoperability team. We will help you map all five layers before you write a single line of code.
Share
Related Posts
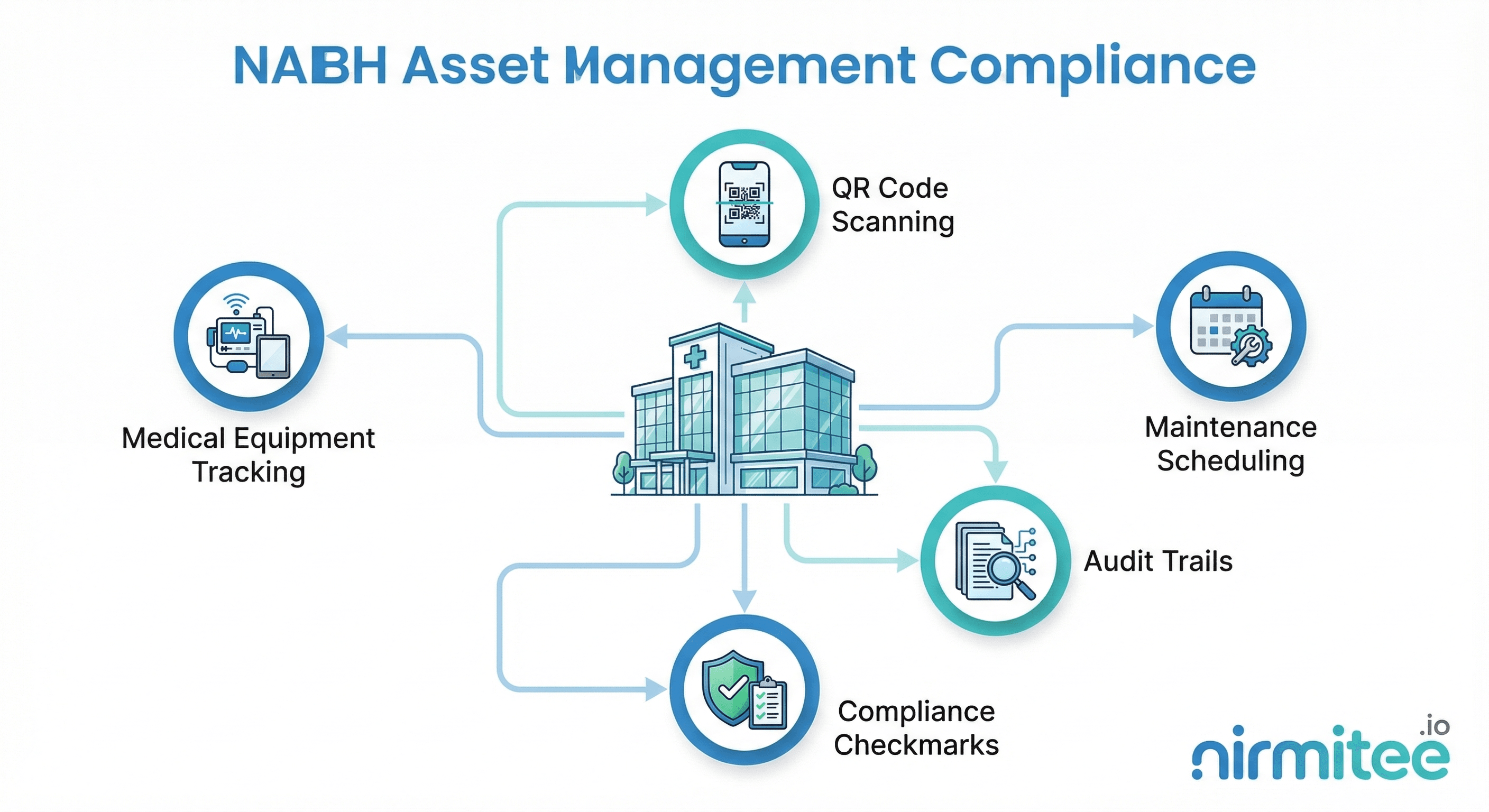
NABH Asset Management Compliance: A Complete Guide for Indian Hospitals
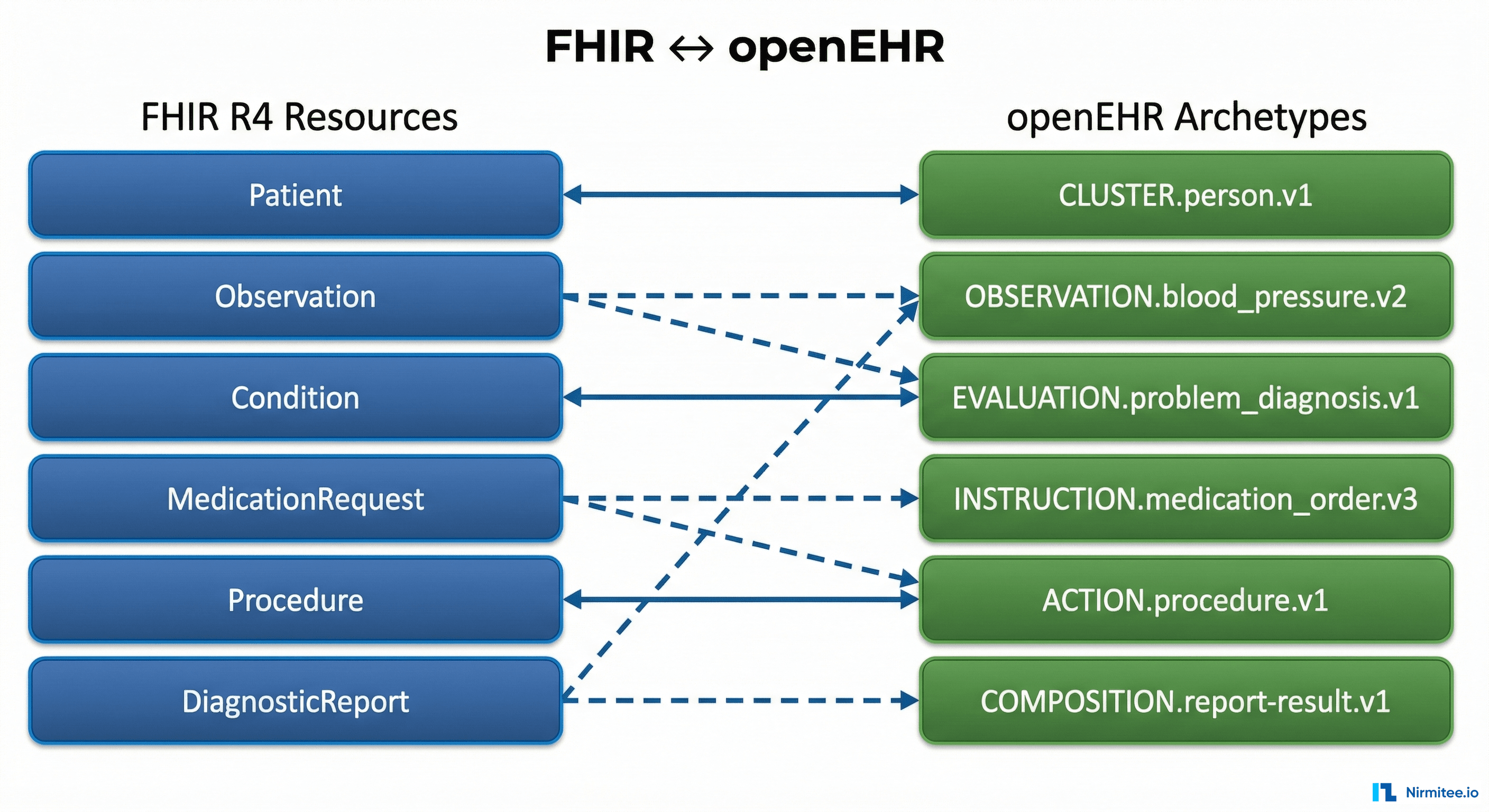
The Complete FHIR-to-openEHR Resource Mapping Matrix (2026 Reference)