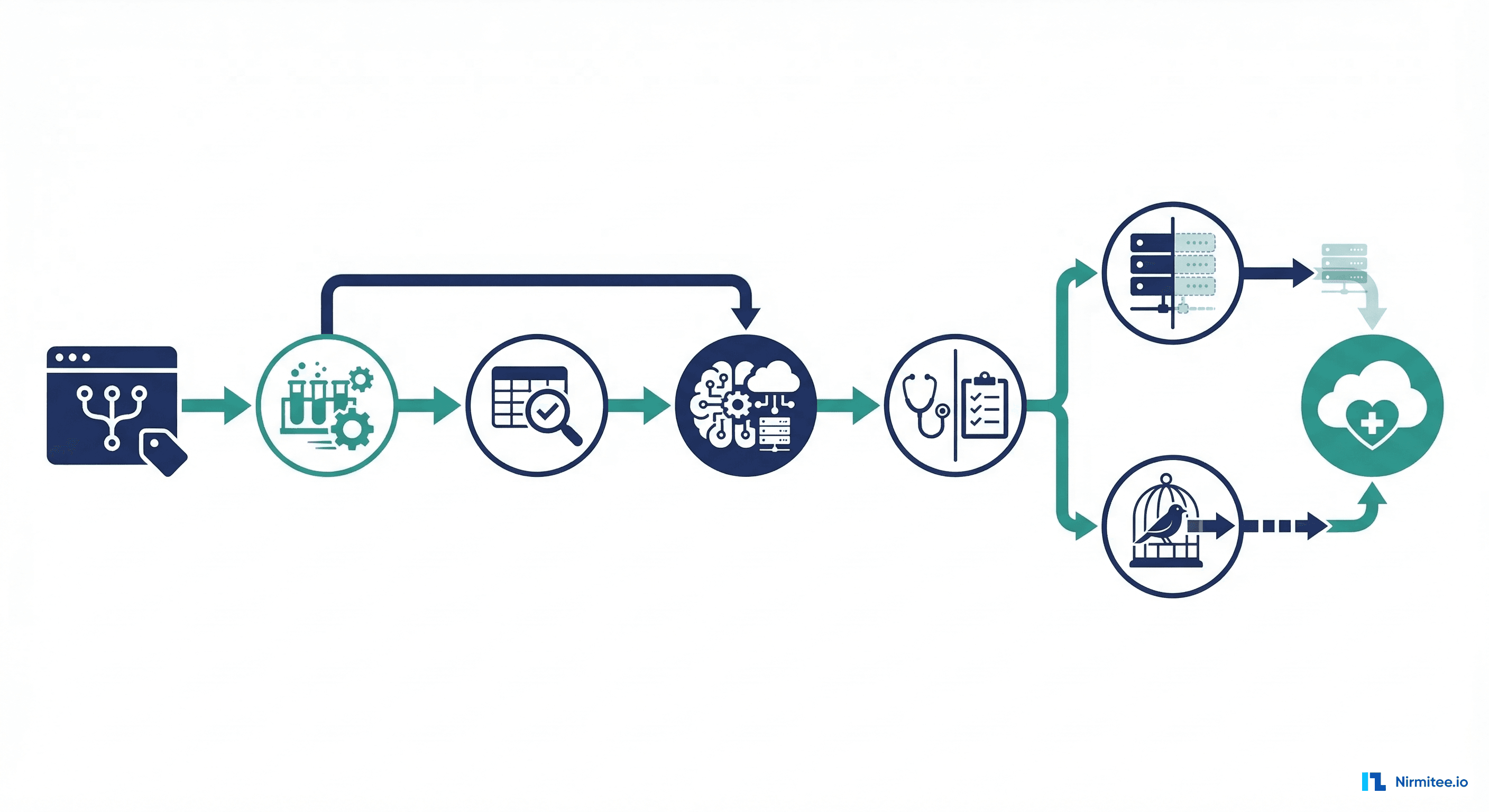
When healthcare organizations evaluate AI agents, HIPAA compliance is always near the top of the concern list. "How do we ensure the AI is HIPAA compliant?" "What happens if the agent accesses data it should not?" "How do we audit an AI's decisions?"
These are the right questions, but they lead to a surprising answer: AI agents are actually easier to make HIPAA compliant than human staff. Not marginally easier — fundamentally easier. And the reason is straightforward: every single thing an agent does is automatically logged with complete context, reasoning, and data access records. Humans do not — and realistically cannot — document their work at this level of detail.
This is not a theoretical argument. After building compliance logging into 20+ healthcare AI agents, we have seen the audit evidence firsthand. Agent audit trails are more complete, more consistent, and more useful for compliance purposes than the audit trails of the human processes they replace.
Human Audit Trails — The Uncomfortable Reality
HIPAA requires covered entities to maintain audit trails that document who accessed what protected health information, when, and why. In practice, human audit trails have significant gaps:
Self-reported access justification. When a staff member accesses a patient record, the system logs that they accessed it. But the reason for access — the "why" that HIPAA cares about — is usually either not captured at all or captured via a dropdown menu that gets the same answer ("patient care") regardless of the actual reason. A 2024 HIMSS survey found that only 34% of healthcare organizations had audit systems that could reliably determine whether a specific record access was justified.
Incomplete decision documentation. When a billing specialist decides to appeal a claim denial, where is the record of their reasoning? Usually, it is in their head, or in a brief note in the claims system that says "appealing - medical necessity." The specific payer policy they referenced, the clinical evidence they reviewed, the alternative actions they considered — none of this is systematically captured.
Estimated coverage: 30-40%. Internal audits at healthcare organizations consistently find that 60-70% of PHI access events lack sufficient documentation to determine whether the access was appropriate. The access log shows that a user opened a record, but not whether they needed to, which fields they looked at, or what they did with the information.
Selective documentation. Humans document what they are trained to document and skip the rest. If the compliance training emphasizes documenting medication changes, those get documented. If it does not specifically cover documenting why a particular patient's lab results were reviewed, that access goes unrecorded. The audit trail reflects the training program, not the actual work.
Retrospective construction. When an audit occurs, staff often have to reconstruct their reasoning after the fact. "I accessed that record because..." becomes an exercise in plausible explanation rather than factual documentation. The audit trail is created retroactively, which inherently makes it less reliable.
Agent Audit Trails — Automatic, Complete, 100% Coverage
An AI agent's audit trail is fundamentally different because it is a byproduct of how the agent operates, not an additional task imposed on top of the work. The agent cannot function without generating a complete audit record.
Every data access is logged with purpose. Before the agent reads a FHIR resource, the compliance logger records: which resource is being accessed, which fields are needed, why they are needed (the workflow step and its purpose), and what data access policy authorizes this access. This happens automatically as part of the agent's orchestration — there is no additional documentation step.
Every decision includes its reasoning chain. When the agent decides to approve a prior authorization, appeal a denial, or classify a document, the full reasoning chain is captured: what data was considered, what rules or policies were applied, what alternatives were evaluated, what confidence level was assigned, and what action was taken. This is not a summary — it is the actual reasoning process the agent followed.
Every human interaction is captured. When a human reviews an agent recommendation, the audit trail records: what the agent recommended, what the human decided, whether they agreed or overrode the recommendation, and (through structured input fields) why. Both the AI and human contributions to the decision are fully documented.
Coverage is 100% by design. There is no mechanism for the agent to access data or make a decision without generating an audit entry. It is architecturally impossible. The logging is not a feature that can be turned off or bypassed — it is woven into the orchestration layer that the agent depends on to function.

What an Agent Audit Entry Looks Like
Here is a concrete example of an agent audit entry for a prior authorization workflow. This is an actual data structure, simplified for readability:
{
"timestamp": "2026-03-14T10:23:47.892Z",
"agent_id": "prior-auth-agent-v2.3",
"workflow": "prior_authorization_review",
"step": "clinical_evidence_evaluation",
"transaction_id": "pa-2026-0314-8847",
"data_accessed": [
{
"resource": "Patient/pat-29481",
"fields_read": ["name", "birthDate", "identifier"],
"purpose": "patient_identification",
"policy": "pa-workflow-data-access-v1"
},
{
"resource": "Condition/cond-84721",
"fields_read": ["code", "onsetDateTime", "clinicalStatus"],
"purpose": "diagnosis_verification",
"policy": "pa-workflow-data-access-v1"
},
{
"resource": "Encounter/enc-29583",
"fields_read": ["type", "period", "reasonCode"],
"purpose": "clinical_context",
"policy": "pa-workflow-data-access-v1"
}
],
"reasoning": {
"input_summary": "PA request for CPT 27447 (TKA) with primary diagnosis M17.11",
"policy_applied": "BlueCross PA Policy ORTHO-2025-12",
"criteria_evaluated": [
"Conservative treatment >= 6 months: YES (PT documented 2025-06 through 2025-12)",
"Imaging evidence of joint degeneration: YES (MRI 2025-11-15)",
"Functional limitation documented: YES (KOOS score 38/100)"
],
"decision": "APPROVE",
"confidence": 0.96,
"confidence_factors": "All three required criteria met with clear documentation"
},
"action": "auto_approved",
"human_review": "not_required",
"outcome": "submitted_to_payer"
}Compare this to a typical human audit trail for the same workflow: "User jsmith accessed Patient/pat-29481 at 10:23 AM. User jsmith submitted PA request PA-2026-0314-8847 at 10:31 AM." The human trail tells you what happened. The agent trail tells you what happened, why, based on what evidence, with what confidence, and under what policy authority.
Minimum Necessary Access — Agents Do It Better
The HIPAA minimum necessary standard requires that covered entities limit PHI access to the minimum amount necessary to accomplish the intended purpose. This is one of the most commonly violated HIPAA requirements because it is nearly impossible to enforce consistently with human staff.
When a billing specialist opens a patient record to check insurance eligibility, they can see the patient's entire chart — diagnoses, medications, lab results, clinical notes. The system cannot prevent them from reading information that is not relevant to eligibility verification. The minimum necessary standard is enforced through training and policy, not through technology.
Agents are different. Each agent workflow has a data access policy that specifies exactly which FHIR resources and which fields the agent is authorized to access for that workflow. The FHIR connector enforces this policy before retrieving any data:
- An eligibility verification agent accesses Patient demographics, Coverage, and Organization. It does not access Conditions, Medications, or Clinical Notes because the data access policy for eligibility verification does not include them.
- A prior authorization agent accesses the clinical data relevant to the specific procedure — the diagnosis, relevant imaging and lab results, and treatment history. It does not access unrelated clinical data.
- A document classification agent reads the document content and basic patient demographics. Notably, it access the patient's full medical record.
That represents theoretical access control — it is enforced at the code level. The agent literally cannot access data outside its authorized scope because the FHIR connector will reject the request. And every authorized access is logged with the specific fields retrieved and the policy that authorized the retrieval.
Try implementing this with human staff. You would need to create a separate EHR view for every workflow, showing only the relevant fields. Most EHR systems do not support this level of granular access control. And even if they did, staff would resist the friction of switching between restricted views for different tasks.
The HIPAA Security Rule — Agents Address Every Requirement
The HIPAA Security Rule has three categories of safeguards. Here is how agent architecture addresses each one:
Administrative Safeguards
- Access authorization (164.312(a)(1)): Agent access is defined by data access policies that specify exactly which resources and fields each workflow can access. These policies are version-controlled, reviewed, and auditable. Change history is maintained.
- Workforce training (164.308(a)(5)): Agents do not need training — they execute their policies consistently every time. Specifically, there risk of a new employee not yet completing compliance training or a veteran employee developing shortcuts that bypass policy.
- Security incident procedures (164.308(a)(6)): Any anomalous agent behavior (unexpected data access patterns, confidence score distribution shifts, unusual error rates) triggers automated alerts. Detection is faster and more consistent than relying on human reporting of security incidents.
Physical Safeguards
- Workstation security (164.310(c)): Agents run in controlled cloud environments with defined security configurations. There is no risk of an unlocked workstation, a stolen laptop, or PHI displayed on a screen in a public area.
- Device and media controls (164.310(d)): Agent data flows through defined, encrypted channels. There are no USB drives, printed documents, or screenshots to manage.
Technical Safeguards
- Audit controls (164.312(b)): As described above — 100% coverage, automatic, tamper-evident. This is the strongest compliance advantage agents have over human processes.
- Integrity controls (164.312(c)): Agent decisions are deterministic given the same inputs and prompts. Decision integrity can be verified by replaying the inputs through the same agent version.
- Transmission security (164.312(e)): All agent communications use TLS encryption. In practice, there unencrypted email, fax, or phone call to worry about — communication channels that are notoriously difficult to secure in human workflows.
Breach Notification — Faster Detection, Precise Scope
When a data breach occurs, HIPAA requires notification within 60 days. The two critical questions are: how quickly do you detect the breach, and how precisely can you determine its scope?
Human process breach detection: The average time to detect a healthcare data breach in 2025 was 194 days (source: IBM/Ponemon Institute). Detection often depends on external reports — a patient notices unauthorized activity, or an auditor discovers anomalous access patterns months after the fact. Determining scope requires forensic analysis of access logs that may be incomplete.
Agent process breach detection: Anomalous agent behavior is detectable in real time. If an agent accesses data outside its authorized scope (which should be architecturally impossible but could occur through a software defect), the compliance logger flags it immediately. If an agent's decision patterns shift unexpectedly (potentially indicating prompt injection or data poisoning), statistical monitoring catches it within hours, not months.
Scope determination is equally different. With complete audit trails, you can determine precisely which records were accessed, which fields were read, what was done with the data, and when. Notably, there forensic reconstruction required — the information is already captured in the compliance log. A breach that takes weeks to scope in a human process takes hours with agent audit trails.
This matters for breach notification compliance, but it also matters for breach containment. The faster you detect and scope a breach, the faster you can contain it and notify affected individuals. And the more precise your scope determination, the fewer individuals you need to notify — reducing both the legal exposure and the reputational damage.
Practical Implementation of Compliance Logging
Building an effective compliance logging system for healthcare agents requires specific architectural decisions:
Append-only storage. Audit logs must be immutable. Use an append-only data store — whether that is a purpose-built audit log service, an immutable database table, or a cloud storage bucket with object lock enabled. No process should be able to modify or delete audit entries after they are written.
Structured, queryable format. Audit entries should be structured data (JSON), not free text. Auditors need to query the log by patient, by time range, by workflow type, by confidence level, by data access type. Unstructured logs require manual review, which defeats the purpose of comprehensive logging.
Separate from application databases. Compliance logs should be stored in a separate system from the application's operational data. This prevents accidental deletion during database maintenance, ensures that log access can be independently controlled, and allows the audit system to be available even when the application is down.
Retention policies aligned with HIPAA. HIPAA requires retention of audit logs for six years. Design your storage and archival strategy for this retention period from day one. Cloud storage costs for six years of audit logs are trivial compared to the cost of discovering that you cannot produce audit records for a period that is under regulatory review.
Real-time monitoring. Do not just store logs — monitor them. Set up alerts for anomalous patterns: unusual data access volumes, unexpected workflow types, confidence score distributions that shift, error rates that spike. The value of comprehensive logging increases dramatically when combined with real-time monitoring.
Field-level access logging. Log not just which FHIR resources the agent accessed, but which fields. This supports minimum necessary access auditing and enables precise breach scope determination. The overhead of field-level logging is minimal — the FHIR connector already knows which fields it retrieved — and the compliance value is significant.
The Compliance Officer's Perspective
We have presented agent audit trail capabilities to compliance officers at healthcare organizations ranging from small practices to large health systems. The reaction is consistently the same: initial skepticism, followed by recognition that agent audit trails solve problems they have been struggling with for years.
The questions shift from "how do we ensure the AI is compliant" to "can we extend this logging to our human processes too?" When a compliance officer sees a complete reasoning chain for every decision, with field-level data access logging and real-time anomaly detection, they compare it to the sparse, self-reported audit trails they get from human processes — and they want the agent version for everything.
This is perhaps the most counterintuitive aspect of healthcare AI compliance: the AI is not the compliance risk. It is the compliance solution. The risk was always in the unmonitored, undocumented human processes. Agents do not introduce new compliance challenges — they solve existing ones by making comprehensive audit trails a structural feature rather than an aspirational goal.
The Bottom Line
HIPAA compliance for AI agents is not a problem to solve — it is an advantage to leverage. Every agent decision is automatically logged with complete reasoning, every data access is documented with field-level precision, minimum necessary access is enforced by code rather than policy, and breach detection happens in real time rather than months after the fact.
The organizations that frame AI compliance as a barrier are looking at it backwards. The question is not "how do we make the AI compliant." The question is "why are we still relying on human processes that produce incomplete audit trails, cannot enforce minimum necessary access, and take months to detect breaches?" Agent audit trails do not just meet HIPAA requirements — they exceed them in ways that human processes never could.
Ready to deploy AI agents in your healthcare workflows? Explore our Agentic AI for Healthcare services to see what autonomous automation can do. We also offer specialized Healthcare AI Solutions services. Talk to our team to get started.