Choosing a healthcare interoperability vendor is no longer a technology procurement decision. It is a strategic bet on your organization's ability to comply with federal mandates, exchange data across networks, and compete for value-based care contracts. Get it right, and you unlock seamless data exchange across your health system. Get it wrong, and you face regulatory penalties, integration failures, and a technical debt that takes years to unwind.
This guide gives you a structured, research-backed framework for evaluating interoperability vendors in 2026 — built specifically for CTOs, CIOs, and VPs of IT at US hospitals and health systems.
Why Interoperability Vendor Selection Is a Strategic Decision
The days of treating interoperability as a back-office IT project are over. Three forces have converged to make vendor selection a board-level concern:
1. Regulatory pressure is non-negotiable. CMS's Q1 2026 deadline for aligned payer networks means your systems must exchange standardized data with payers, other providers, and public health agencies — or face consequences. The ONC's information blocking rules carry penalties of up to $1 million per violation. This is not a future concern; enforcement is active.
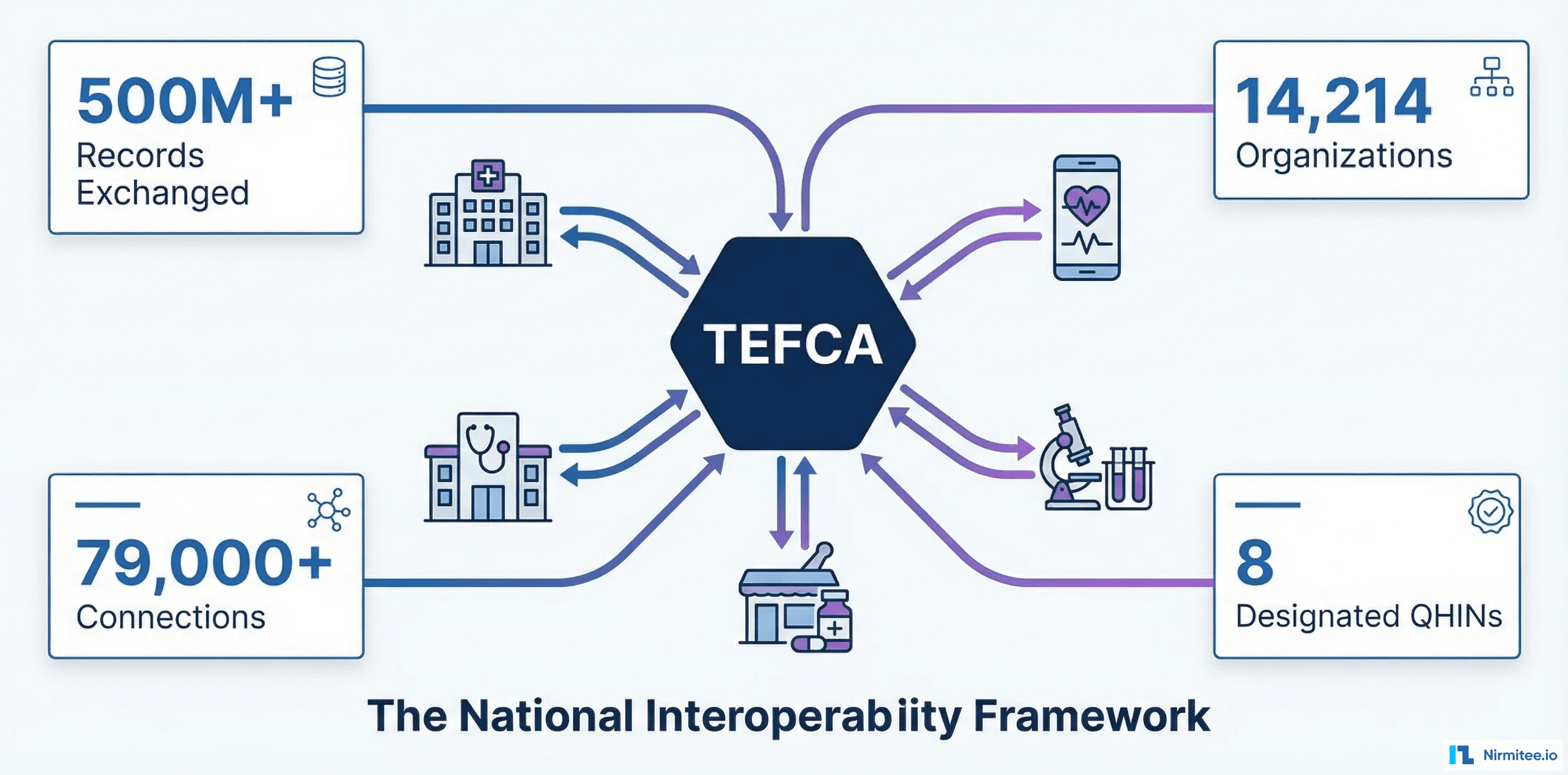
2. Network effects are accelerating. TEFCA now connects 14,214 organizations with over 500 million records exchanged. CommonWell Health Alliance and Carequality continue to expand. If your vendor cannot connect you to these networks, you are an island — and islands do not win referrals, contracts, or patients.
3. Clinical and operational ROI depends on data liquidity. Healthcare interoperability standards like FHIR, HL7, and C-CDA are not abstract — they directly enable use cases like real-time ADT notifications, closed-loop referral management, population health analytics, and prior authorization automation. The vendor you choose determines which of these use cases you can actually deliver.
The average US hospital spends between $1.2 million and $4 million on interoperability infrastructure over a 5-year period, according to CHIME survey data. A poor vendor choice does not just waste budget — it delays clinical programs, frustrates physicians, and puts your organization behind competitors who chose better.
The Hidden Cost of Getting It Wrong
A 2025 Ponemon Institute study found that healthcare organizations that switched interoperability vendors mid-contract spent an average of $2.3 million in transition costs — not including the 8-14 months of reduced integration capacity during the migration. These costs break down into three categories:
- Technical migration costs — Rebuilding interfaces, re-mapping data transformations, re-testing with every trading partner. If you have 50 active interfaces, each one needs to be rebuilt, tested, and validated in the new platform
- Operational disruption — During migration, your integration team is focused on rebuilding, not innovating. New interface requests from clinical teams get delayed by 6-12 months
- Organizational trust erosion — Clinical stakeholders lose confidence in IT when interoperability breaks during a migration. This trust takes years to rebuild and affects every subsequent technology initiative
The message is clear: choose carefully the first time. The evaluation framework in this guide is designed to help you avoid the most common selection mistakes.
The 2026 Regulatory Landscape: What You Must Comply With
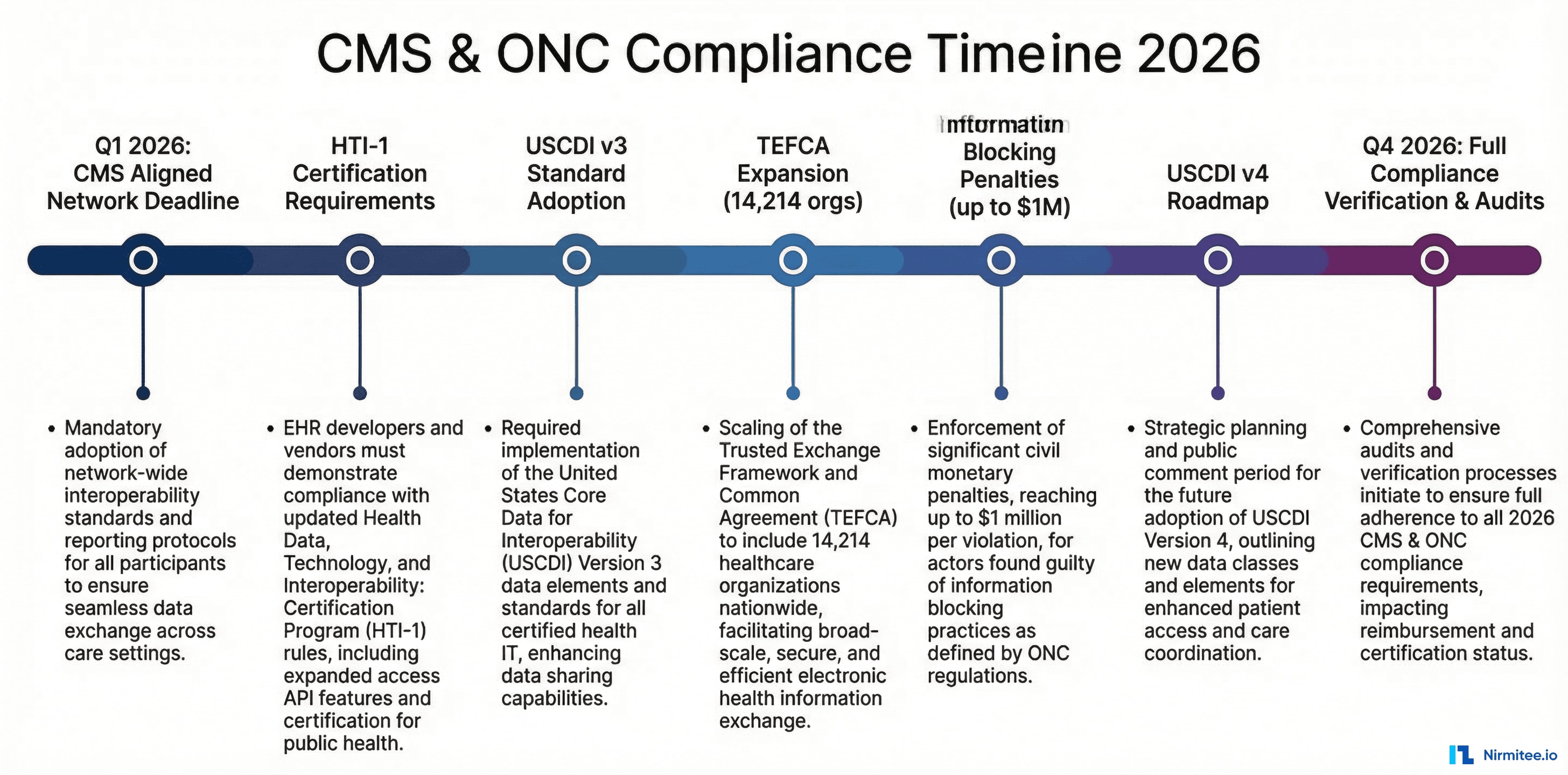
Before evaluating any vendor, you need to understand the compliance baseline. Here is what matters in 2026:
CMS Interoperability and Prior Authorization Final Rule
Effective Q1 2026, CMS requires impacted payers (Medicare Advantage, Medicaid, CHIP, QHP issuers on the exchanges) to implement:
- Patient Access API — FHIR-based API for patients to access claims and clinical data
- Provider Access API — Payer-to-provider data exchange for treatment
- Payer-to-Payer API — Patient data follows the patient when switching payers
- Prior Authorization API — Electronic prior auth with 72-hour/7-day response requirements
For hospitals and health systems, this means your interoperability vendor must support FHIR R4 APIs that align with these requirements. If your vendor only does HL7 v2 ADT feeds, you have a significant gap.
ONC Health IT Certification: HTI-1 and Beyond
The HTI-1 final rule updates the ONC Health IT Certification Program with:
- USCDI v3 as the minimum data standard (expanding to v4)
- Updated FHIR API requirements for certified EHR technology
- New decision support intervention requirements
- Mandatory SVAP (Standards Version Advancement Process) updates
Your vendor must either be ONC-certified or integrate cleanly with ONC-certified EHR systems. If they claim "FHIR-ready" but cannot demonstrate USCDI v3 compliance, they are selling you a roadmap, not a product.
Information Blocking Enforcement
The ONC and HHS Office of Inspector General now actively enforce information blocking provisions under the 21st Century Cures Act. Penalties include:
- Up to $1 million per violation for health IT developers and HIEs
- Disincentives (including CMS payment adjustments) for healthcare providers
- Required exception documentation if you limit data access
Your vendor must not create information blocking scenarios — intentional or accidental. Proprietary data formats, restrictive APIs, or excessive fees for data access all create compliance risk.
TEFCA: The National Network
The Trusted Exchange Framework and Common Agreement (TEFCA), managed by the Sequoia Project as the Recognized Coordinating Entity (RCE), is the federal government's framework for nationwide health information exchange. Key facts:
- 14,214 organizations now participate through Qualified Health Information Networks (QHINs)
- 500+ million records exchanged across the network
- Six designated QHINs: eHealth Exchange, Health Gorilla, KONZA, MedAllies, Epic Nexus, and CommonWell (via Carequality)
- TEFCA supports treatment, payment, healthcare operations, public health, and individual access use cases
If your vendor does not have a clear TEFCA participation story — either as a QHIN, through a QHIN, or via a concrete roadmap — that is a yellow flag.
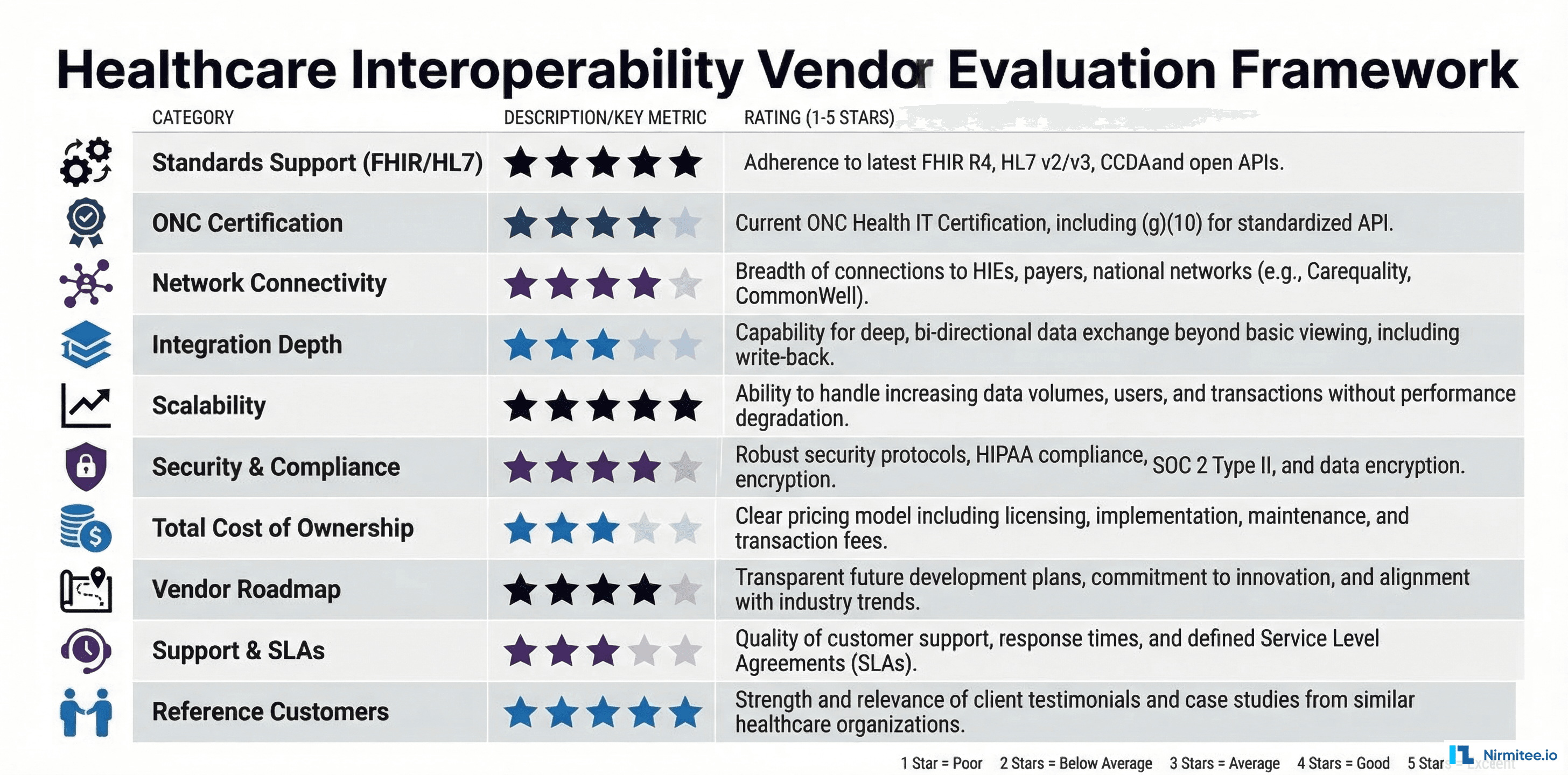
The 10-Point Vendor Evaluation Framework
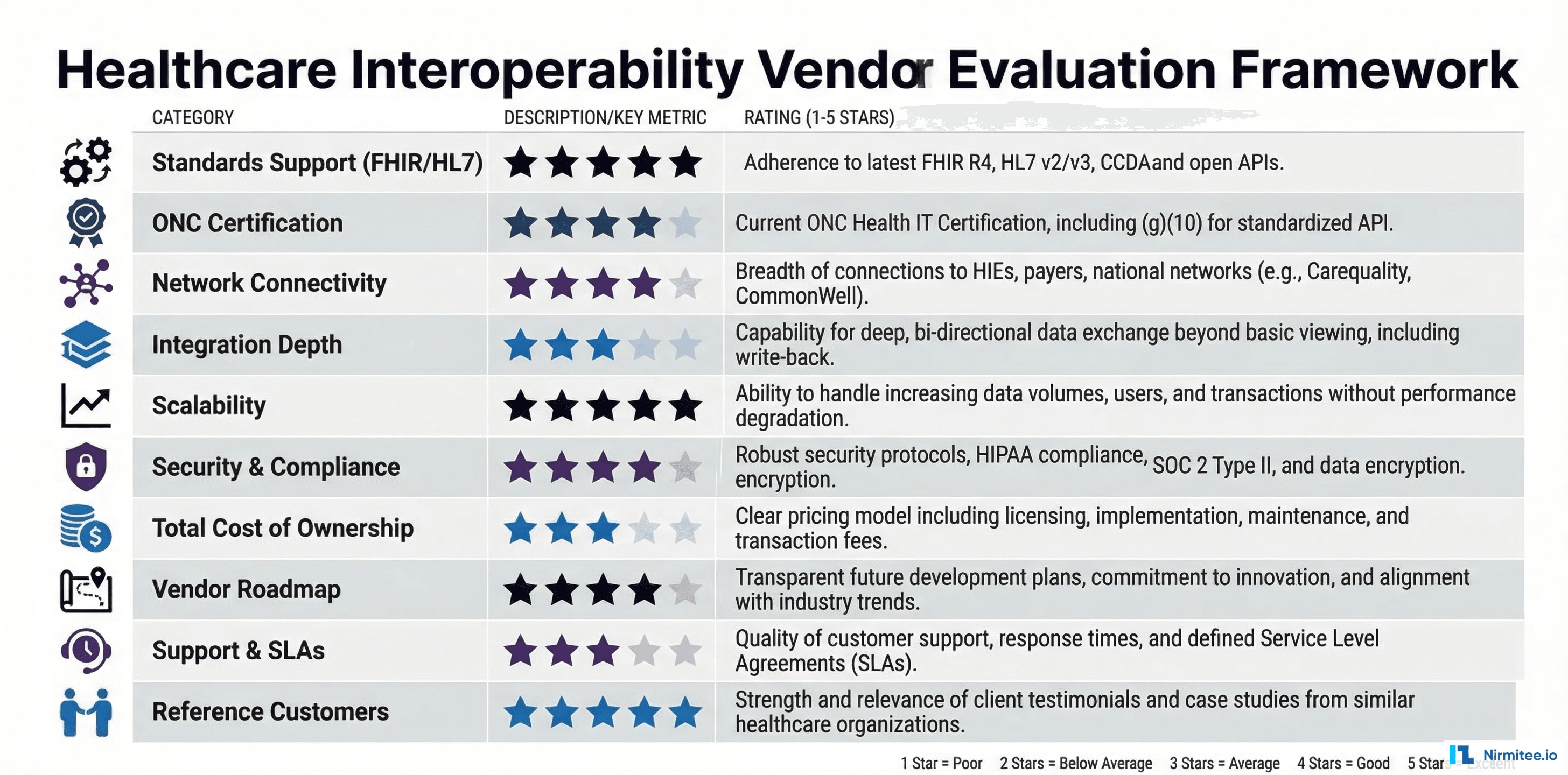
This framework gives you a structured, comparable way to evaluate any interoperability vendor. Score each criterion on a 1-5 scale during your evaluation process.
1. Standards Support (FHIR, HL7, C-CDA, USCDI)
This is the foundation. A vendor's standards support determines what data you can exchange, with whom, and how efficiently.
What to evaluate:
- FHIR R4 support — Not just "we support FHIR" but specific resource coverage: Patient, Encounter, Observation, Condition, MedicationRequest, DiagnosticReport, Procedure, AllergyIntolerance, Immunization, DocumentReference
- FHIR Bulk Data Export — Essential for population health and analytics. Does the vendor support the Bulk Data Access specification?
- USCDI v3/v4 data classes — v3 adds Health Insurance Information, Specimen, and expanded Clinical Notes. v4 adds Encounter Diagnosis, Facility Information, and more. Ask which version they support today and their v4 timeline
- C-CDA support — Continuity of Care Documents remain critical for transitions of care, especially with HIEs. The vendor should support C-CDA R2.1 at minimum
- HL7 v2 backward compatibility — Most hospital systems still run on HL7 v2 ADT, ORM, ORU, and SIU messages. Your vendor must handle v2 interfaces while supporting FHIR for new use cases
- SMART on FHIR — Application launch framework for clinical apps. Critical for third-party app ecosystems and patient-facing tools
Red flag: A vendor that only supports FHIR but cannot handle HL7 v2, or vice versa, is going to create integration gaps. Real-world interoperability requires both.
2. Certification Status (ONC, SOC 2 Type II)
Certifications are not just checkboxes — they represent verified, audited compliance.
What to evaluate:
- ONC 2015 Edition Cures Update certification — This is the current baseline. Check the CHPL (Certified Health IT Product List) to verify claims
- HTI-1 readiness — Ask for their certification timeline. If they do not have a clear date, they are behind
- SOC 2 Type II — Not Type I. Type I is a point-in-time assessment. Type II covers sustained operational controls over 6-12 months. Demand the report
- HITRUST CSF — Increasingly expected by enterprise health systems, especially for cloud-based solutions
Red flag: "We are pursuing certification" without a timeline. Certification takes 12-18 months. If they have not started, they will not have it when you need it.
3. Network Connectivity (TEFCA, CommonWell, Carequality)
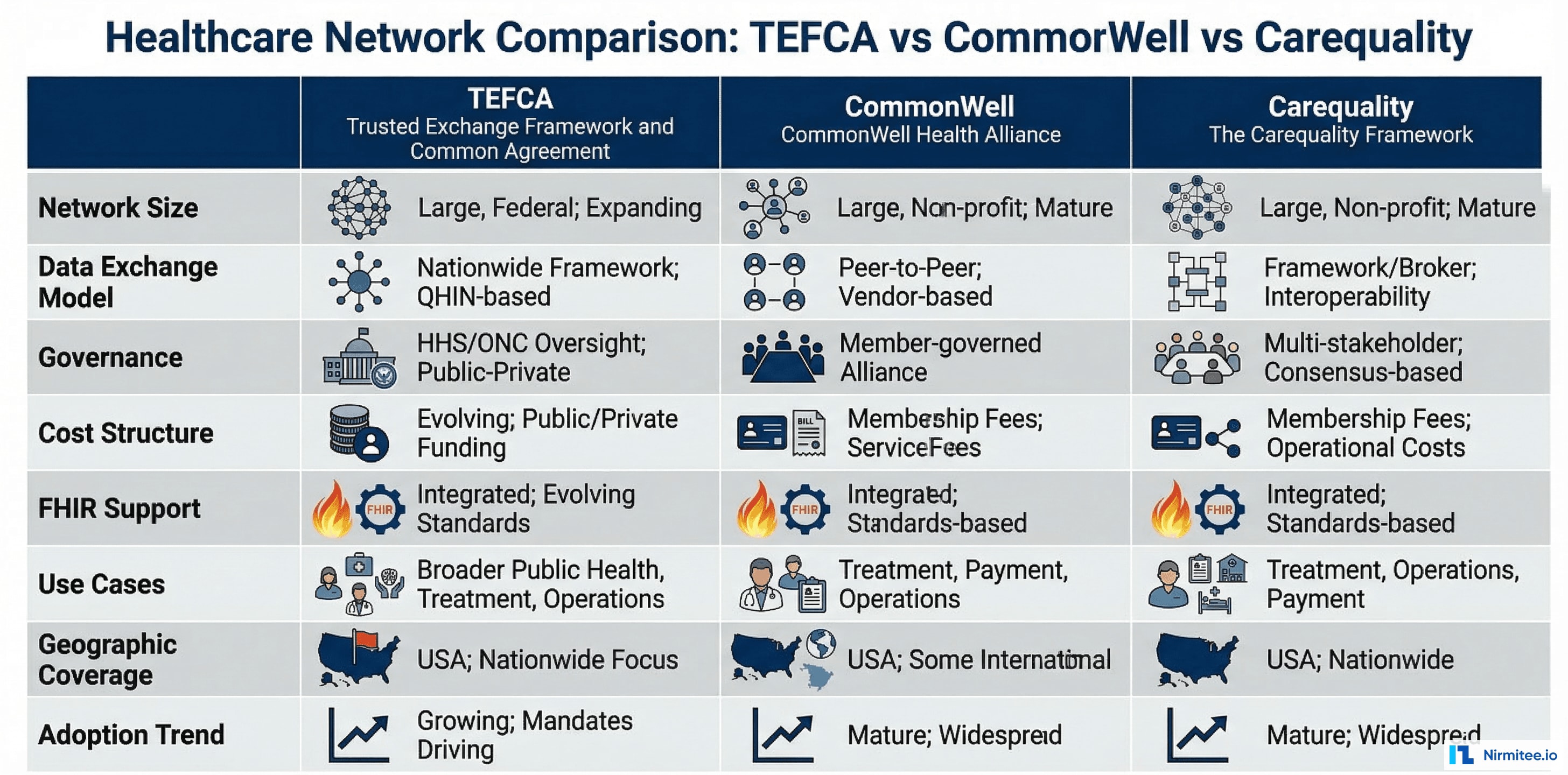
Network connectivity determines your reach. A vendor with deep network connections saves you from building point-to-point interfaces.
What to evaluate:
- TEFCA participation — Are they a QHIN, a Participant, or a Sub-Participant? Each level has different capabilities and obligations
- CommonWell Health Alliance membership — Provides patient identity matching and record location across member organizations
- Carequality connection — The largest query-based exchange network. Many EHR vendors connect through Carequality for document exchange
- Direct Messaging — Still the standard for secure provider-to-provider communication and transitions of care. Support for Direct Standard is non-negotiable
- State HIE connections — Many states have mandatory HIE reporting requirements. Your vendor should have pre-built connections to your state's HIE
- eHealth Exchange — The largest QHIN, connecting federal agencies (VA, DoD) with private health systems
Ask: "How many unique endpoints can I reach through your network today, without building custom interfaces?" The answer tells you everything about their network value.
4. Integration Depth (Pre-Built Connectors vs. Custom)
The difference between a 3-month and a 12-month implementation often comes down to pre-built connectors.
What to evaluate:
- EHR connectors — Pre-built integrations with Epic, Oracle Health (Cerner), MEDITECH, Allscripts/Veradigm, athenahealth, and other EHRs in your ecosystem
- Lab system connectors — Interfaces to Quest, Labcorp, BioReference, and hospital LIS systems
- Payer connectors — For claims, eligibility, prior authorization, and member data exchange
- Specialty system connectors — Radiology (PACS/RIS), pharmacy, behavioral health, long-term care
- Public health reporting — Electronic case reporting (eCR), immunization registries, syndromic surveillance, reportable lab results
- API marketplace — Does the vendor offer a catalog of pre-built connectors, or is everything custom?
Red flag: "We can build any interface you need." That is a services company, not a platform. You want pre-built, tested, maintained connectors — not custom development for every integration.
5. Scalability (Single Facility vs. Multi-Site)
Your interoperability needs today are not your needs in 3 years. Evaluate for where you are going, not just where you are.
What to evaluate:
- Multi-site deployment — Can the platform manage integrations across 5, 50, or 500 facilities from a single pane of glass?
- Message volume — What is their peak throughput? A small critical access hospital processes 10,000 messages/day. A large IDN might process 10 million. Your vendor must handle your scale
- Multi-tenancy — For health systems with multiple entities, the platform should support tenant isolation while enabling cross-tenant analytics
- Geographic distribution — If you operate across states, the platform must handle different state regulations, HIE connections, and reporting requirements
- Cloud vs. on-premise — Cloud-native platforms scale more easily but some organizations have on-premise requirements. Hybrid support matters
6. Security and Compliance (HIPAA, Audit, BAA)
Every interoperability vendor handles PHI. Security is not optional — it is a disqualifying criterion.
What to evaluate:
- HIPAA compliance documentation — Not just a statement, but documented policies, procedures, and audit results
- Business Associate Agreement (BAA) — Must be willing to sign a BAA that covers their full platform, including subcontractors
- Encryption — Data at rest (AES-256 minimum) and in transit (TLS 1.2+). No exceptions
- Audit logging — Complete, immutable audit trails for all data access, modification, and transmission
- Access controls — Role-based access, multi-factor authentication, and principle of least privilege
- Incident response — Documented breach notification procedures that meet the 60-day HIPAA requirement
- Penetration testing — Annual third-party pen tests with remediation documentation
Red flag: A vendor that hesitates to share their SOC 2 report, BAA template, or pen test summary is hiding something.
7. Total Cost of Ownership
License fees are the visible part of the iceberg. The real cost includes implementation, maintenance, and opportunity cost.
What to evaluate:
- License model — Per-connection, per-message, per-bed, or flat platform fee? Each model has different scale economics
- Implementation cost — Professional services for setup, configuration, testing, and go-live. Typically 1-3x the annual license
- Ongoing maintenance — Version upgrades, connector updates, regulatory compliance updates. Who pays for these?
- Internal resource requirements — How many FTEs does your organization need to manage the platform day-to-day?
- Integration development costs — For custom interfaces not covered by pre-built connectors
- Training costs — Initial and ongoing training for integration engineers, analysts, and operations staff
- Exit costs — Data migration, interface rebuilding, and transition costs if you need to switch vendors
Ask for a 5-year TCO breakdown, not just year-one pricing. A vendor that is cheap to license but expensive to implement and maintain will cost more over time than a higher-priced platform with lower operational burden.
8. Vendor Roadmap (FHIR R6, USCDI v4, AI Capabilities)
Healthcare technology moves fast. Your vendor's roadmap tells you whether they will keep up.
What to evaluate:
- FHIR R5/R6 roadmap — R5 introduced subscriptions and workflow improvements. R6 development is underway. What is their adoption timeline?
- USCDI v4 readiness — The next expansion of the US Core Data for Interoperability standard adds critical data classes
- AI/ML capabilities — Intelligent routing, data quality scoring, anomaly detection, natural language processing for unstructured data. These are differentiators in 2026
- Cloud-native evolution — Microservices, containerization, serverless processing for elastic scaling
- Patient engagement — Consumer-facing APIs, patient matching improvements, consent management
- Transparency — Does the vendor share their roadmap publicly? Do customers have input into prioritization?
9. Support and SLAs
Interoperability is a 24/7 operation. When an ADT feed goes down at 2 AM, you need someone to answer.
What to evaluate:
- Uptime SLA — 99.9% is the minimum for production healthcare interfaces. 99.95% or higher for critical feeds
- Response time SLAs — P1 (system down): 15 minutes. P2 (degraded): 1 hour. P3 (non-critical): 4 hours. These are table stakes
- 24/7/365 support — Not "business hours with on-call." Actual 24/7 coverage with healthcare-experienced engineers
- Dedicated account management — A named technical account manager who understands your environment
- Monitoring and alerting — Proactive monitoring of interface health, message queues, and error rates — not just reactive support
- Documentation quality — Comprehensive, up-to-date API documentation, integration guides, and knowledge base
10. Reference Customers
The most reliable predictor of vendor performance is how they perform for organizations like yours.
What to evaluate:
- Similar organization type — If you are a 400-bed community hospital, a reference from a 20-physician practice is not relevant. Ask for references from organizations of similar size and complexity
- Similar use cases — If you need lab interoperability, ask for a reference that implemented lab interoperability — not just ADT feeds
- Implementation timeline accuracy — Ask the reference: "Was the project delivered on time? What caused delays?"
- Go-live stability — "How many critical issues occurred in the first 30 days after go-live?"
- Support quality — "When something breaks at 2 AM, how quickly do they respond, and do they fix it?"
- Contract satisfaction — "Would you sign the same contract again? What would you negotiate differently?"
Minimum: Get 3 references. Call them. Do not rely on vendor-provided case studies alone. Organizations willing to take a 30-minute reference call are genuinely satisfied customers.
Build vs. Buy vs. Partner: The Decision Matrix
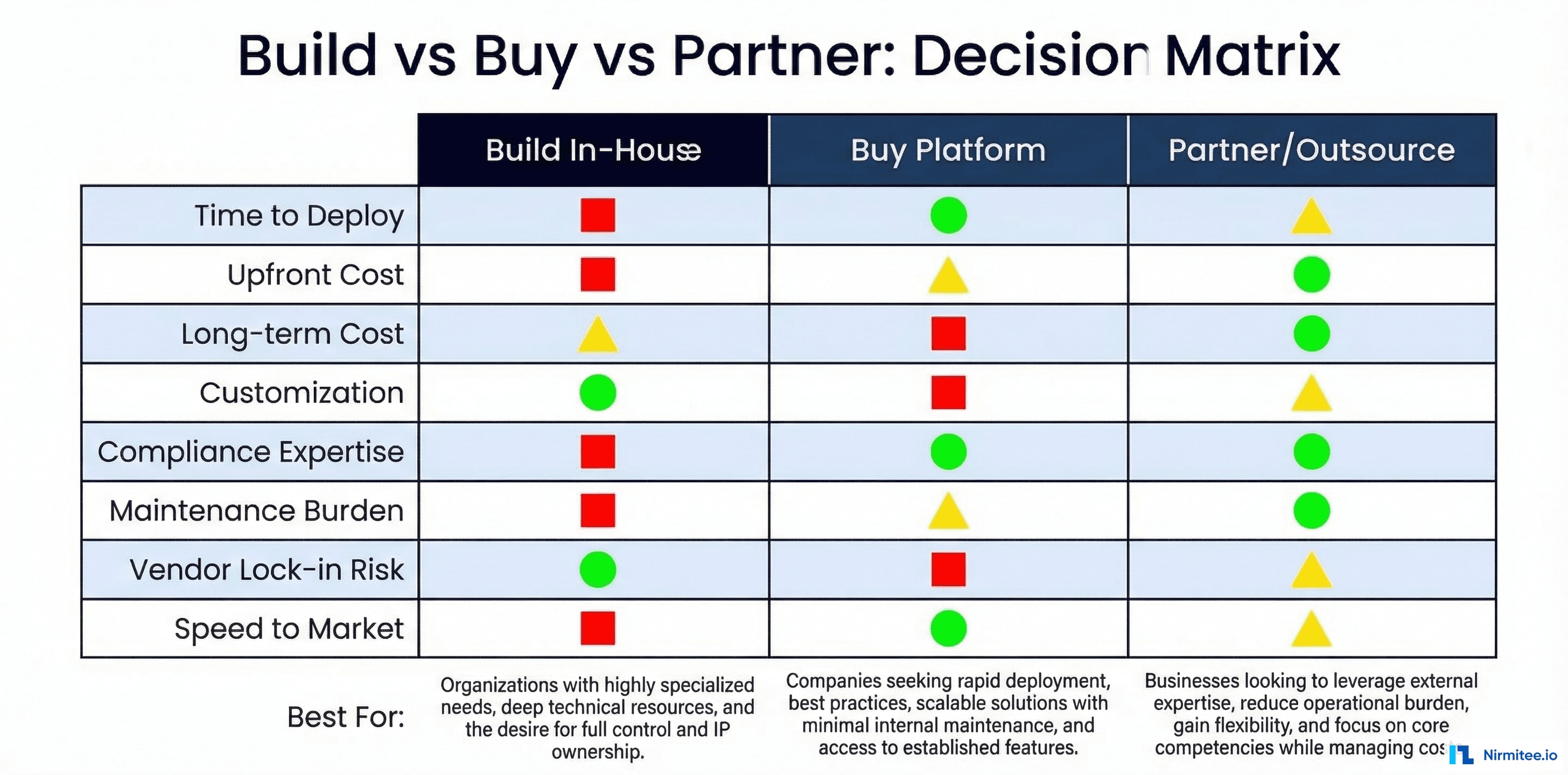
Before you evaluate vendors, you need to decide your approach. Each has distinct trade-offs:
Build In-House
Best for: Large IDNs with 10+ integration engineers, unique workflow requirements, and existing middleware expertise.
- Advantages: Full control, deep customization, no vendor lock-in, internal IP ownership
- Disadvantages: 12-24 month build time, ongoing maintenance burden, difficulty staying current with standards, recruiting specialized talent
- Typical cost: $2-5M over 3 years (engineering salaries + infrastructure)
Buy a Platform
Best for: Mid-size health systems (200-1,000 beds) that need proven, standards-compliant interoperability without building from scratch.
- Advantages: Faster deployment (3-6 months), pre-built connectors, vendor-managed compliance updates, proven at scale
- Disadvantages: License costs, potential vendor lock-in, less customization, dependency on vendor roadmap
- Typical cost: $500K-$2M over 3 years (license + implementation + maintenance)
Leading platforms in this category include Rhapsody (formerly Corepoint), Mirth Connect (NextGen), InterSystems HealthShare, Redox, and Health Gorilla. For organizations already on Epic or Oracle Health, their native interoperability tools (Epic Nexus/Care Everywhere, Oracle Health Bridge) deserve evaluation as well.
Partner/Outsource
Best for: Organizations with limited IT staff, critical access hospitals, specialty practices, or those needing to move fast on specific use cases.
- Advantages: Fastest time to value (weeks, not months), expertise without hiring, flexible engagement, lower upfront investment
- Disadvantages: Less internal knowledge transfer, ongoing dependency, common mistakes in healthtech integrations if you choose the wrong partner
- Typical cost: $300K-$1.5M over 3 years (engagement + platform + support)
The right choice depends on your IT maturity, timeline, budget, and strategic priorities. Many organizations use a hybrid approach — buying a platform and partnering for implementation and optimization.
Red Flags: When to Walk Away from a Vendor
In our experience delivering 30+ healthcare integrations across US health systems, we have seen patterns that reliably predict vendor problems. Walk away if you see these:
- "We support all standards" — without being able to demonstrate specific FHIR resource implementations, HL7 v2 message types, or C-CDA document templates. Vague claims signal vague capabilities.
- No SOC 2 Type II report — If they only have Type I, or if they claim it is "in progress" without a completion date, their security program is immature.
- Customer concentration — If 50%+ of their revenue comes from one or two customers, a single customer loss could destabilize the company.
- Proprietary data formats — Any vendor that stores your data in a proprietary format, or charges extraction fees, is creating information blocking risk and vendor lock-in.
- No reference customers willing to talk — If they cannot produce 3 references at organizations similar to yours, something is wrong.
- Implementation timeline of "4-6 weeks" — For a meaningful interoperability deployment, this is unrealistic. A vendor promising this is either oversimplifying or underdelivering.
- Hidden fees for standards compliance updates — USCDI version updates, FHIR spec updates, and regulatory compliance updates should be included in maintenance. If they are priced as add-ons, your TCO will spiral.
- No TEFCA strategy — TEFCA is the direction of national interoperability. A vendor without a clear TEFCA participation plan is not investing in the future.
RFP Template: 20 Questions to Ask Every Vendor
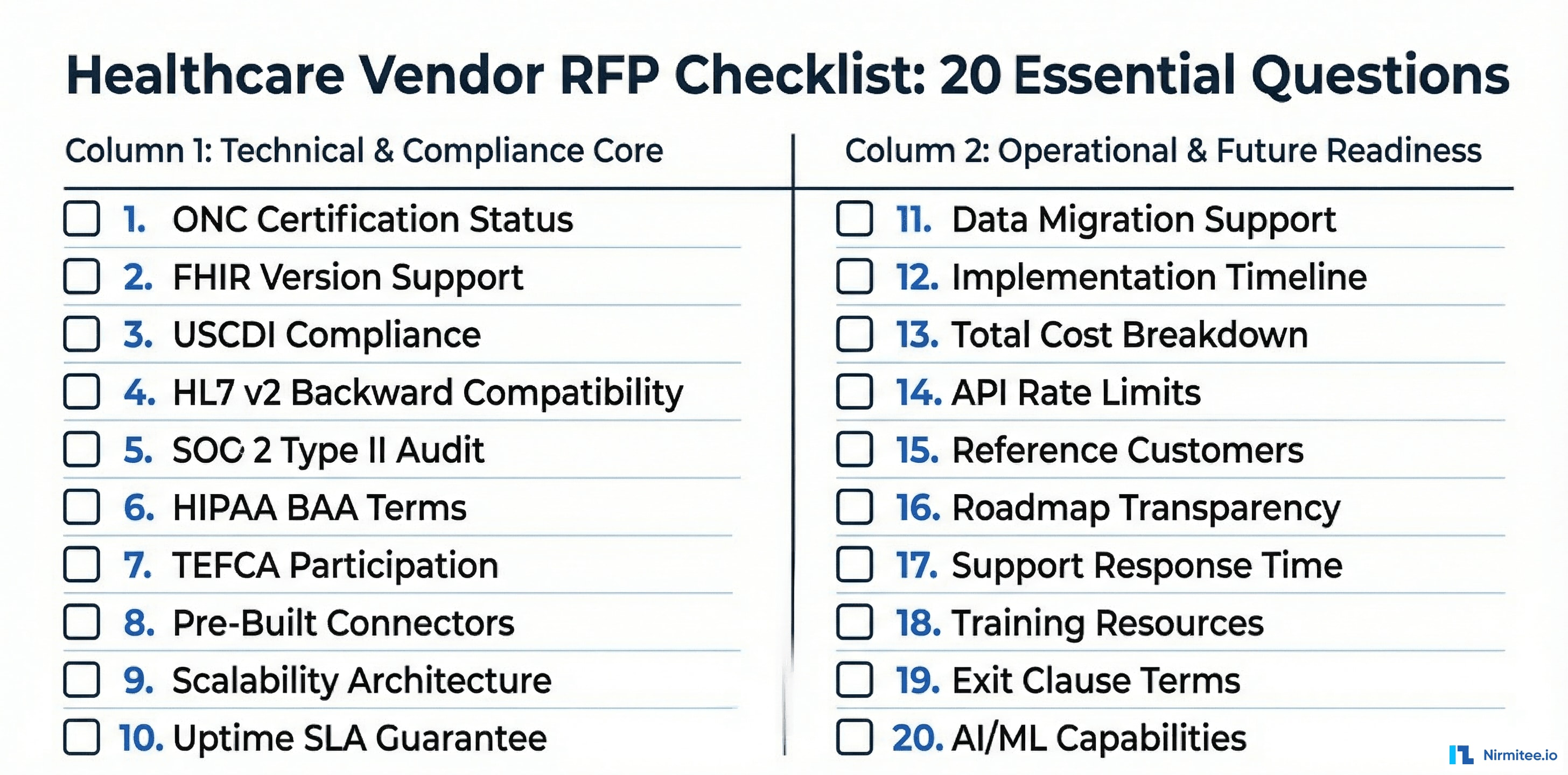
Copy this template directly into your RFP. These questions are designed to surface real capabilities, not marketing claims.
Standards and Certification
- What specific FHIR R4 resources does your platform support natively? Provide the complete list with read/write/search capabilities for each.
- What is your current ONC certification status? Provide your CHPL listing number and certified module list.
- Do you support USCDI v3 today? What is your timeline for USCDI v4 compliance?
- Which HL7 v2 message types and versions do you support? (ADT, ORM, ORU, SIU, MDM, DFT — specify versions 2.3, 2.4, 2.5.1, 2.7)
- Do you support SMART on FHIR application launch? Which launch contexts (EHR, standalone, backend services)?
Security and Compliance
- Provide your most recent SOC 2 Type II audit report. What was the audit period and were there any exceptions?
- What is your HIPAA compliance program? Provide your BAA template and list all subcontractors who handle PHI.
- Describe your encryption standards for data at rest and in transit. What key management approach do you use?
- When was your last third-party penetration test? Provide a summary of findings and remediation status.
- What is your breach notification process? What is the guaranteed notification timeline?
Network and Integration
- What is your TEFCA participation status? Are you a QHIN, Participant, or Sub-Participant? Through which QHIN(s)?
- How many pre-built EHR connectors do you maintain? Provide the list with supported versions (e.g., Epic 2024, Oracle Health Millennium, MEDITECH Expanse).
- How many unique endpoints can we reach through your network today without custom interface development?
- What is your Direct Messaging implementation? Do you operate your own HISP or use a third-party?
Cost and Commercial Terms
- Provide a 5-year total cost of ownership breakdown: license, implementation, annual maintenance, per-interface costs, training, and any volume-based pricing tiers.
- What are your contract terms for data portability? If we terminate, what format is our data exported in, and what are the associated costs?
- Are regulatory compliance updates (USCDI version updates, FHIR spec updates, new CMS requirements) included in maintenance, or priced separately?
Support and Track Record
- What is your uptime SLA for production interfaces? What are the financial penalties for SLA violations?
- Provide 3 reference customers at organizations of similar size and complexity to ours. We will conduct independent reference calls.
- What is your product roadmap for the next 18 months? How do customers provide input into roadmap prioritization?
Pro tip: Send these questions before the demo. A vendor that can answer all 20 comprehensively in writing has a mature product and organization. A vendor that wants to "discuss on a call" for basic questions is either unprepared or evasive.
Implementation Timeline Expectations
Realistic timelines for healthcare interoperability implementations:
| Implementation Phase | Duration | Key Activities |
|---|---|---|
| Discovery and Planning | 2-4 weeks | Current state assessment, interface inventory, use case prioritization, technical architecture review |
| Contract and Procurement | 4-8 weeks | BAA execution, security review, legal review, procurement approval |
| Platform Setup | 2-4 weeks | Environment provisioning, network connectivity, certificate exchange, user access setup |
| Interface Development | 4-12 weeks | Interface configuration, mapping, transformation rules, custom development for non-standard interfaces |
| Testing | 4-6 weeks | Unit testing, integration testing, end-to-end testing with trading partners, volume testing, failover testing |
| Go-Live and Stabilization | 2-4 weeks | Production cutover, parallel running, monitoring, issue resolution, performance tuning |
| Optimization | Ongoing | Error rate reduction, new interface onboarding, compliance updates, performance optimization |
Total realistic timeline: 4-9 months for a meaningful interoperability deployment. Anyone promising 4-6 weeks is either scoping a trivial project or setting you up for disappointment.
Key factors that extend timelines:
- Trading partner readiness (you cannot control their timeline)
- Security review and BAA negotiation (legal teams move slowly)
- EHR vendor cooperation for API access and endpoint configuration
- Data quality issues discovered during testing
- Change management and clinical workflow adjustments
How to Accelerate Your Timeline
While 4-9 months is realistic, organizations that execute well can compress timelines by following these practices:
- Start security review during vendor evaluation — Do not wait until contract negotiation to engage your CISO. Begin the security questionnaire and BAA review during the RFP process. This can save 4-6 weeks
- Pre-identify trading partners — Know which organizations you need to connect with before selecting a vendor. Validate that your top 10 trading partners are already connected to the vendor's network
- Assign a dedicated project manager — Interoperability implementations that share a PM with other projects consistently run 30-50% over timeline. Dedicate one PM full-time
- Parallel test environments — Set up testing environments for 3-5 interfaces simultaneously rather than sequentially. This requires more resources upfront but compresses the testing phase significantly
- Executive sponsorship — Active CMIO or CTO involvement removes organizational blockers that stall implementations. When a trading partner is slow to respond, executive-to-executive outreach moves things faster
Post-Go-Live: The First 90 Days
The implementation does not end at go-live. The first 90 days are critical for stabilization and optimization:
- Days 1-30: Stabilize. Monitor error rates, message throughput, and latency. Expect a 5-10% error rate in the first week that should drop below 1% by day 30. Establish a daily stand-up between your integration team and the vendor's support team
- Days 31-60: Optimize. Address edge cases, tune transformation rules, improve data quality. Review clinical feedback on data completeness — are clinicians getting the information they need at the point of care?
- Days 61-90: Expand. Onboard the next wave of interfaces. Document lessons learned. Establish operational runbooks for common issues. Transition from project mode to operational support mode
Set clear success metrics before go-live: interface uptime percentage, message error rate, mean time to resolution for interface issues, and clinical user satisfaction scores. Review these weekly for the first 90 days.
The Vendor Landscape: Key Players to Evaluate
The US healthcare interoperability market includes several categories of vendors. Understanding where each fits helps you scope your evaluation:
EHR-Native Interoperability
- Epic — Nexus (TEFCA QHIN), Care Everywhere (provider-to-provider), MyChart (patient access), App Orchard (third-party apps). The strongest ecosystem if you are an Epic shop
- Oracle Health (Cerner) — CommonWell founding member, CommunityWorks, open APIs. Strong in the federal space (VA, DoD)
Integration Platforms (Middleware)
- Rhapsody (Corepoint) — Mature integration engine with strong HL7 v2 and FHIR support. Widely used in mid-size health systems
- Mirth Connect (NextGen) — Open-source foundation with commercial support. Large installed base, flexible, cost-effective for organizations with integration engineering talent
- InterSystems HealthShare — Enterprise-grade platform with strong analytics capabilities. Common in large academic medical centers and IDNs
Cloud-Native Interoperability Platforms
- Redox — Cloud-based integration platform with 500+ health system connections. Strong API-first approach and developer experience
- Health Gorilla — TEFCA-designated QHIN. Strong in clinical data exchange, lab results, and patient matching
- 1upHealth — FHIR-native platform focused on payer interoperability and CMS compliance
- Particle Health — Clinical data access across networks. Strong in point-of-care data retrieval
- Datavant — Focused on health data connectivity and de-identification. Strong in life sciences and real-world evidence
The right choice depends on your existing infrastructure, use cases, budget, and technical maturity. An interoperability solutions partner with deep EHR integration expertise can help you navigate this landscape based on your specific requirements.
Market Trends Shaping Vendor Selection in 2026
Several market dynamics should influence your evaluation:
- Vendor consolidation is accelerating. Private equity and strategic acquirers are rolling up interoperability companies. Rhapsody acquired Corepoint in 2021. NextGen acquired Mirth Connect. Oracle acquired Cerner. When evaluating a vendor, assess their ownership structure and acquisition risk — if they get acquired, your roadmap and support model may change dramatically
- AI-powered integration is emerging. Leading vendors are introducing machine learning for interface mapping, anomaly detection, and data quality improvement. While these capabilities are still maturing, they represent the next frontier of interoperability. Ask vendors about their AI strategy, but weight current capabilities over future promises
- Patient-mediated exchange is growing. Apple Health Records, CommonHealth, and patient-facing FHIR apps are creating new data flows that your interoperability platform must support. Evaluate whether the vendor supports patient-generated health data (PGHD) and consumer APIs
- Value-based care is driving new use cases. Risk stratification, quality measure reporting, and care gap identification all depend on comprehensive, timely data exchange. Your interoperability vendor must support these analytics-driven use cases, not just clinical messaging
- Cybersecurity requirements are tightening. The HHS 405(d) program, potential HIPAA updates, and increasing ransomware attacks on healthcare mean your interoperability platform is a critical attack surface. Evaluate vendors on their security posture as rigorously as their interoperability capabilities
Making the Decision: A Practical Approach
After evaluating vendors against the 10-point framework, here is how to drive a decision:
- Weight the criteria — Not all 10 points are equal for your organization. If you are a community hospital joining TEFCA, network connectivity might be 3x more important than scalability. If you are a multi-state IDN, scalability and multi-tenancy are critical
- Score independently — Have 3-5 stakeholders (CTO, CISO, integration lead, clinical informatics, finance) score each vendor independently, then compare
- Conduct a technical proof of concept — Before signing a contract, run a 30-60 day POC with your top 2 vendors on a real (non-production) use case. This surfaces integration issues that demos never reveal
- Negotiate the contract — Key negotiation points: data portability clause, SLA penalties with teeth, compliance update inclusion, exit provisions, price protection for volume growth
- Plan for the first 90 days — Define success criteria for the initial deployment. What interfaces will be live? What error rate is acceptable? What is the rollback plan if things go wrong?
The vendor you choose today will be your interoperability backbone for 5-7 years. Take the time to evaluate thoroughly. The cost of switching vendors mid-stream — in money, time, clinical disruption, and team morale — far exceeds the cost of a thorough evaluation process.
Looking for an interoperability partner who understands both the technical depth and the regulatory landscape? Our team has delivered 30+ healthcare integrations across US health systems. Talk to us to discuss your specific requirements and get a tailored evaluation framework.