On February 21, 2024, the Blackcat/ALPHV ransomware group breached Change Healthcare — the clearinghouse processing 15 billion healthcare transactions annually. Attackers moved laterally for nine days before detonating ransomware that crippled claims processing, prescription fulfillment, and eligibility verification nationwide. Final tally: 192.7 million patient records exposed. The largest healthcare data breach in American history.
That was 2024. In March 2026 alone, Stryker suffered a destructive wiper attack — malware designed purely to destroy, not extort. CareCloud's SaaS platform was breached on March 31, exposing patient data from hundreds of practices that trusted a single cloud vendor with their PHI. Healthcare now accounts for 32% of all ransomware incidents — twice any other industry — with a 36% year-over-year increase in attacks on medical practices.
The average healthcare breach costs $11 million per incident (IBM, 2024), making it the most expensive industry to breach for fourteen consecutive years. Meanwhile, the proposed HIPAA Security Rule overhaul — mandating MFA, encryption at rest, and annual audits — faces opposition from over 100 hospitals arguing they cannot afford compliance.
This post presents the cybersecurity architecture healthcare organizations need, mapped to NIST CSF 2.0 controls. If you are a CISO, IT director, or security architect responsible for protecting PHI, this is your engineering blueprint.
The 2026 Threat Landscape
Organizations running a perimeter-firewall-and-antivirus strategy have a 2015 defense posture against 2026 adversaries. Four threat categories now dominate healthcare.
Ransomware remains the primary vector. The HHS HC3 reports 32% of all attacks targeting healthcare are ransomware, with double and triple extortion now standard — attackers encrypt systems, exfiltrate data, then contact affected patients demanding individual payments. RaaS (Ransomware-as-a-Service) platforms from Blackcat/ALPHV, LockBit 3.0, and Cl0p lower the barrier so that a teenager with a Telegram account can rent ransomware infrastructure. Modern variants specifically target backup systems before encrypting production, eliminating the alternative to paying.
Wiper attacks mark a category shift. The March 2026 Stryker attack deployed malware designed purely to destroy — no ransom demand, no decryption key. When a wiper hits a hospital's PACS, years of imaging studies vanish. When it hits medical device control systems, patient safety is immediately at risk.
Supply chain compromise exploits vendor concentration. The CareCloud breach exposed every practice on the platform simultaneously — none had independent security controls. This pattern repeats across clearinghouses, RCM platforms, telehealth vendors, and health information exchanges.
AI-enhanced reconnaissance uses LLMs for automated recon — scraping job postings to identify tech stacks, generating phishing emails that pass native-speaker scrutiny, and scanning vulnerabilities at scale. Healthcare is uniquely vulnerable because clinical communication patterns (urgent lab results, emergency credentialing) create a culture of rapid response that attackers exploit.
Anatomy of the Change Healthcare Attack
The Change Healthcare breach is the most consequential cyberattack in healthcare history — not because of its technical sophistication, but because of its scope. Understanding exactly what happened at the architectural level reveals the systemic failures that most healthcare organizations still have not addressed.
| Date | Event | Architectural Failure |
|---|---|---|
| Feb 12, 2024 | Initial access via compromised Citrix portal credentials | No MFA on remote access gateway |
| Feb 12-17 | Lateral movement through internal network | Flat network — no microsegmentation |
| Feb 17-20 | 6 TB data exfiltration (PHI, PII, financial records) | No DLP monitoring, no anomalous egress detection |
| Feb 21 | Blackcat/ALPHV ransomware detonation | No EDR capable of stopping encryption cascade |
| Feb 21 - Mar | National disruption — claims, prescriptions, eligibility halted | No business continuity failover for 15B annual transactions |
| Oct 2024 | 192.7 million records confirmed exposed | Excessive data retention, no minimization strategy |
Every failure had a corresponding NIST CSF control. The Citrix portal lacked MFA (PR.AC-7). The flat network had no segmentation (PR.AC-5). Six terabytes left the network without triggering DLP alerts (DE.CM-1). No business continuity architecture existed for a system processing 50% of US healthcare claims. UnitedHealth Group paid $22 million in ransom and reported over $870 million in direct costs. The SRE principles of error budgets and five-nines availability were entirely absent.
The attack was not a zero-day exploit or a nation-state APT using novel techniques. It was a textbook ransomware operation that succeeded because the target lacked basic security architecture. That is the uncomfortable truth for healthcare CISOs: most breaches exploit the gap between what organizations know they should do and what they have actually built.
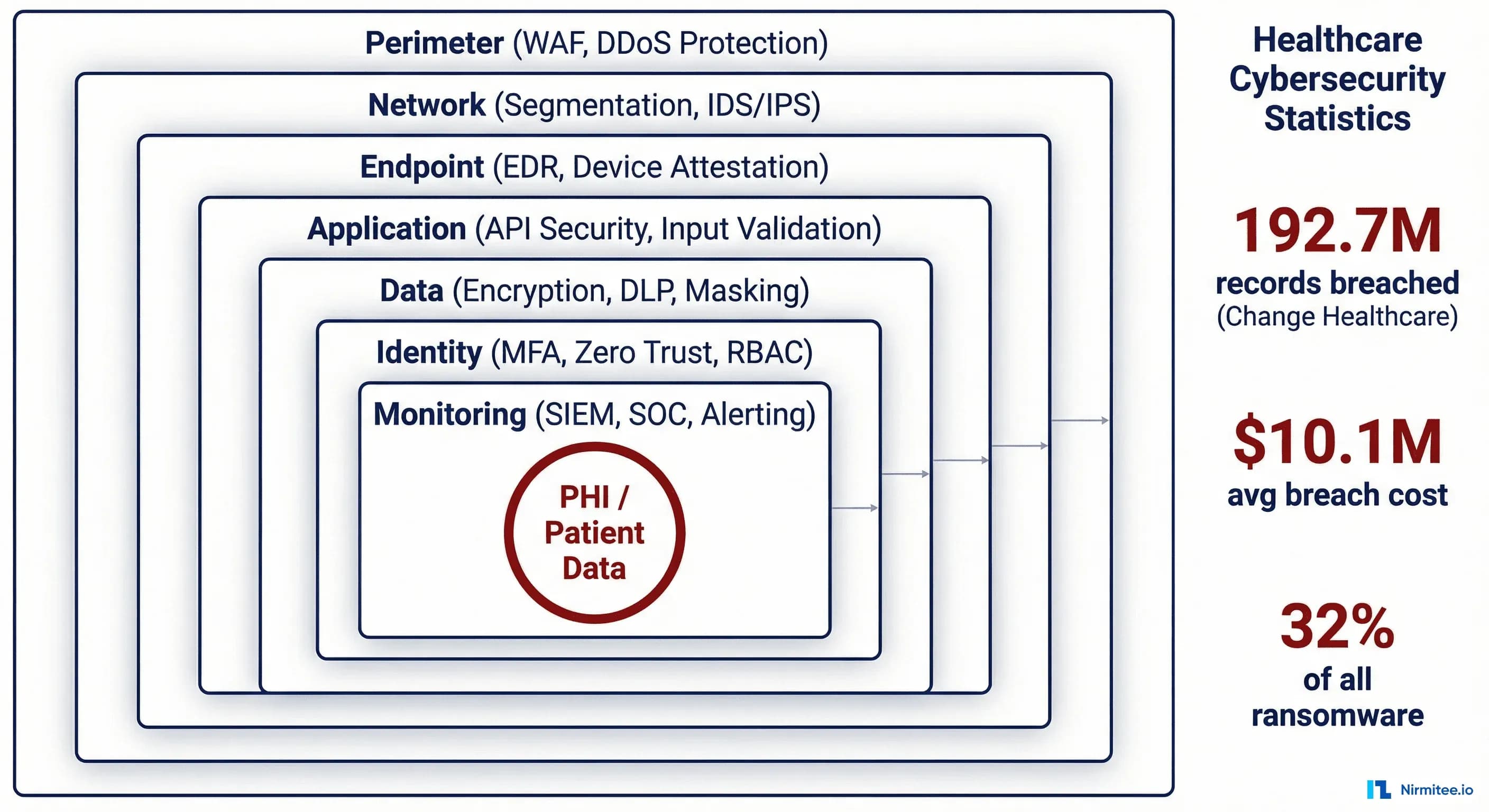
Defense-in-Depth Architecture for Healthcare
Defense-in-depth is the foundational security architecture principle: multiple independent layers of defense, each capable of stopping or slowing an attack even if other layers fail. No single control is assumed to be sufficient. Every layer operates on the assumption that the layers above it have already been compromised. The following seven-layer architecture is mapped to NIST CSF 2.0 functions and designed specifically for healthcare organizations managing PHI under HIPAA.
Layer 1 — Perimeter (PR.AC-3): WAF in front of all internet-facing applications including FHIR endpoints, configured with OWASP Top 10 plus healthcare-specific rules. DDoS mitigation — attackers increasingly time DDoS to overwhelm the SOC while ransomware moves through the network. DNS filtering to block C2 infrastructure. All remote access gateways enforce phishing-resistant MFA (FIDO2/WebAuthn, not SMS OTP).
Layer 2 — Network Segmentation (PR.AC-5): The control that prevents a single credential from compromising the entire organization — the exact control missing at Change Healthcare. Implement healthcare-specific segmentation zones:
| Zone | Contents | Access Policy |
|---|---|---|
| Clinical DMZ | Patient portals, telehealth, external FHIR APIs | Internet-facing, WAF-protected, no direct DB access |
| Clinical Production | EHR, CPOE, nursing systems | Internal only, role-based, MFA required |
| Medical Devices | IoMT devices, PACS, infusion pumps | Isolated VLAN, no internet egress, allowlist-only |
| Data Warehouse | Analytics, reporting, research databases | Read-only from clinical production, no internet |
| Administrative | HR, finance, email, productivity | Segmented from clinical, standard corporate security |
| Backup / DR | Immutable backups, recovery infrastructure | Air-gapped, break-glass access only |
East-west firewalls between zones enforce allowlist-based communication. A compromised workstation in administrative cannot reach medical devices. A breached patient portal cannot query production EHR databases directly.
Layer 3 — Endpoint (PR.PT-1): EDR with behavioral detection (CrowdStrike, SentinelOne, or Defender for Endpoint) on every endpoint. CIS Benchmark hardening. Risk-based patching: CVSS 9.0+ within 72 hours, 7.0-8.9 within 14 days. For unpatchable medical devices, compensating controls via network isolation and virtual patching.
Layer 4 — Application (PR.DS-1): SAST in CI/CD and DAST in staging for all internally developed applications. All FHIR and clinical APIs routed through an API gateway enforcing rate limiting, OAuth 2.0 / SMART on FHIR authorization, and request logging.
Layer 5 — Data (PR.DS-2): AES-256 encryption at rest for all databases and backups containing PHI. TLS 1.3 for external traffic, mTLS for service-to-service communication. DLP monitoring for SSN patterns, MRN formats, ICD-10/CPT codes in bulk, and FHIR resource bundles in outbound traffic. Tokenization for non-production environments. This layer would have detected Change Healthcare's 6 TB exfiltration.
Layer 6 — Identity (PR.AC-1): MFA on every system, every user, every time. PAM with just-in-time access for administrators — standing admin access eliminated. RBAC mapped to clinical roles: a billing clerk does not access clinical notes, a lab tech does not access financial records.
Layer 7 — Monitoring (DE.CM-1): Centralized SIEM aggregating logs from every layer with healthcare-specific correlation rules: after-hours PHI access, bulk patient record queries, anomalous FHIR API patterns. SOAR for automated Tier 1 triage — account lockout on suspicious MFA patterns within 60 seconds, no analyst required. 24/7 SOC coverage via MDR providers with healthcare playbooks. The Change Healthcare attackers operated over weekends; 24/7 alerting is not optional.
Zero Trust Architecture for Hospitals
Zero Trust is not a product you buy. It is an architectural philosophy: never trust, always verify. Every access request — regardless of source network, device, or user — is authenticated, authorized, and continuously validated before access is granted. There is no trusted internal network. For hospitals, Zero Trust is both urgently needed and exceptionally difficult to implement because of legacy systems, medical device constraints, and clinical workflow requirements that prioritize speed of access over security friction.
Identity-based access: Centralized IdP (Okta, Entra ID) with MFA at every session. Clinical SSO via tap-and-go badge readers (Imprivata) for speed. Short-lived tokens (15-30 min) with continuous risk re-evaluation.
Device attestation: Every device enrolled in MDM, attesting to patch level, EDR status, and disk encryption before accessing clinical systems. Failed attestation routes to a remediation VLAN.
Network microsegmentation: SDN (Illumio, Guardicore/Akamai, VMware NSX) enforces workload-level allowlists. Lateral movement between microsegments requires re-authentication.
Application-level enforcement: SMART on FHIR scoped access — a cardiologist's token grants access to cardiac patients in their panel, not the entire population. A lab service account writes DiagnosticReports but cannot read MedicationRequests.
Continuous adaptive risk: Policy engine evaluates location changes, time anomalies, impossible travel. Physician logs in from Chicago at 2:00 PM, request from Mumbai at 2:05 PM — session terminated, account locked.
Phased Implementation
- Months 1-3: MFA on all remote access and privileged accounts. Identity inventory. (This alone prevents the Change Healthcare attack vector.)
- Months 3-6: Network segmentation between clinical, administrative, device, and backup zones. EDR on all endpoints.
- Months 6-12: Identity-based SSO, device attestation, microsegmentation for critical workloads.
- Months 12-18: Continuous adaptive risk, SOAR playbooks, full Zero Trust coverage.
Healthcare-Specific Attack Surfaces
Healthcare organizations face attack surfaces that do not exist in other industries. Medical devices, clinical interoperability standards, and legacy imaging systems create unique vulnerabilities that generic cybersecurity frameworks do not adequately address.
EHR APIs (FHIR/SMART): The 21st Century Cures Act mandates FHIR API exposure, expanding the attack surface. Risks include token scope escalation (patient app receiving user/*.read instead of patient/*.read), FHIR search parameter injection via _include and chained searches to enumerate populations, and improperly secured bulk export endpoints — the healthcare equivalent of an open S3 bucket.
Medical devices (IoMT): Infusion pumps, monitors, and imaging systems run unpatchable embedded OS (Windows XP Embedded, VxWorks), ship with published default credentials, and cannot be rebooted mid-treatment. Compensating controls (network isolation, traffic inspection) must substitute for endpoint security.
PACS/DICOM: DICOM was designed in the 1990s with zero security considerations. Traffic is unencrypted by default, DICOM objects contain embedded PHI (patient name, MRN, date of birth) in file headers, and DICOMweb APIs expose imaging data over HTTP. Many PACS servers are accessible from clinical networks without additional authentication. The Stryker wiper attack specifically targeted medical device infrastructure — while full details are still emerging, the attack vector likely exploited this category of unpatched, poorly segmented systems.
Cloud and SaaS: The shared responsibility model is widely misunderstood. Customer-managed encryption keys (CMEK) are essential — PHI must be encrypted with keys the healthcare organization controls. For multi-tenant platforms, verify row-level security or schema isolation. Every vendor with PHI access requires a BAA and SOC 2 Type II or HITRUST CSF attestation. Automated compliance monitoring ensures attestations stay current.
Encryption Architecture
Encryption is healthcare security's most fundamental technical control — and one of the most commonly misconfigured. The HIPAA Security Rule's "addressable" designation for encryption has led many organizations to document it as "not reasonable and appropriate" rather than implementing it. The proposed HIPAA update eliminates this loophole by making encryption at rest and in transit mandatory, with no exceptions.
At rest: AES-256 via TDE for SQL Server/Oracle, pgcrypto for PostgreSQL. Full-disk encryption on all endpoints. Immutable encrypted backups in a separate account/region — the last defense against ransomware.
In transit: TLS 1.3 for all HTTPS and FHIR traffic (disable TLS 1.0/1.1 entirely). mTLS for service-to-service communication within clinical zones. Legacy HL7v2 over MLLP wrapped in TLS via stunnel or modern integration engines.
Key management: Master keys never leave the HSM/KMS boundary. Data encryption keys wrapped by key encryption keys in HSM. 90-day rotation for DEKs, annual for KEKs, automated. Separation of duties: the DBA managing databases cannot access encryption keys. For HIPAA-compliant AI systems processing FHIR resources, apply field-level encryption to Patient.identifier, Patient.name, and Patient.address while leaving Resource.meta in cleartext for indexing.
Incident Response Playbook
The difference between a contained security event and a Change Healthcare-scale catastrophe is the incident response playbook — and whether anyone has actually rehearsed it. An IR plan that exists only as a 200-page PDF on the CISO's SharePoint is not a plan. It is a liability. The following six-phase framework is based on NIST SP 800-61r2, adapted for healthcare-specific requirements including HIPAA breach notification, patient safety, and clinical system continuity.
Phase 1 — Prepare: Quarterly tabletop exercises with IT, security, clinical leadership, legal, and communications. Printed IR team roster with after-hours contacts (if ransomware encrypts AD, you cannot look up the team in the corporate directory). Pre-negotiated retainers with IR firms (CrowdStrike, Mandiant). Monthly restore tests from immutable backups — if the documented RTO for the EHR is 4 hours, prove it.
Phase 2 — Identify: SIEM correlation alerts, EDR detections, user reports, dark web credential monitoring. Healthcare triage: Does this affect clinical systems? Is patient safety at risk? Is PHI exposed?
Phase 3 — Contain: Isolate affected segments, disable compromised accounts, preserve forensic evidence. For every affected system: "If we take this offline, does it affect patient care?" If yes, apply compensating controls while maintaining availability, with clinical leadership sign-off on the risk acceptance.
Phase 4 — Eradicate: Root cause identification, complete malware removal, enterprise-wide credential reset (assume credential harvesting), vulnerability patching. Second forensic scan to verify — attackers deploy persistence mechanisms that survive initial cleanup.
Phase 5 — Recover: Restore from verified clean immutable backups. Bring systems back in priority order: critical clinical first. Clinical validation that restored data is accurate — a pharmacy system restored from a 6-hour-old backup has 6 hours of missing medication orders to reconcile.
Phase 6 — Lessons Learned: Post-incident report distributed to executive leadership and board of directors. Every identified control gap gets a remediation task with an owner, deadline, and budget allocation. If the breach occurred because of missing MFA, the remediation plan includes MFA deployment with a 90-day deadline — not a recommendation to "consider MFA." HIPAA breach notification: if unsecured PHI affecting 500+ individuals was exposed, file with HHS OCR within 60 days (72 hours under the proposed rule), notify affected individuals, and notify media if 500+ individuals in a single state or jurisdiction are affected.
The Proposed HIPAA Security Rule: What Engineers Must Build
HHS OCR's proposed NPRM is the most significant HIPAA update since 2003. Over 100 hospitals oppose certain provisions, but the direction is clear: the era of "addressable" controls is ending.
Mandatory MFA: Required for all ePHI access. Every clinical application must integrate with a centralized IdP. Service accounts need certificate-based auth. Medical devices that access ePHI must support MFA or be isolated with documented compensating controls. Break-glass procedures for MFA outages must be defined and audited.
Mandatory encryption: At rest and in transit — no longer addressable. Database-level encryption for all PHI stores, TLS 1.2 minimum for all transmissions, encrypted backups with independently managed keys.
Annual risk analysis: Complete asset inventory, threat/vulnerability assessment per asset, risk rating, and prioritized remediation — not a one-time checkbox.
72-hour incident notification: Down from 60 days. This requires automated detection and classification — you cannot manually triage, engage forensics, determine scope, and file a report in 72 hours with manual processes.
Annual compliance audits: Not self-assessments — documented audits verifying controls function as designed. Continuous compliance monitoring that verifies encryption, MFA, patch levels, and access controls becomes essential infrastructure.
Frequently Asked Questions
What caused the Change Healthcare breach?
Compromised credentials to a Citrix remote access portal without multi-factor authentication. Attackers moved laterally through a flat, unsegmented network for nine days, exfiltrated 6 TB of data without triggering DLP alerts, then deployed Blackcat/ALPHV ransomware. The breach exposed 192.7 million records and disrupted claims processing nationwide. Every failure had a corresponding NIST CSF control that would have prevented or contained it.
How much does a healthcare data breach cost?
$11 million on average per incident (IBM, 2024) — the highest of any industry for fourteen years running. For large-scale breaches, total costs including legal settlements, fines, and remediation can exceed $1 billion. UnitedHealth Group reported over $870 million in direct costs from the Change Healthcare breach in 2024.
What is defense-in-depth architecture?
Multiple independent layers of defense — perimeter, network, endpoint, application, data, identity, and monitoring — so no single failure enables complete compromise. Healthcare needs it because PHI sells for $250-1,000 per record on dark markets (versus $5-50 for credit cards), downtime threatens patient safety, and HIPAA fines reach $2.13 million per violation category per year.
How does Zero Trust apply to hospitals?
Every access request is authenticated, authorized, and continuously validated regardless of origin. Hospitals implement through: identity-based access with MFA, device attestation via MDM, network microsegmentation between clinical zones, SMART on FHIR scope enforcement at the application layer, and continuous adaptive risk monitoring. Typical implementation is phased over 12-18 months.
What are the proposed HIPAA Security Rule changes?
Mandatory MFA for all ePHI access, mandatory encryption at rest and in transit, annual risk analysis, annual compliance audits, and 72-hour incident notification to HHS OCR (down from 60 days). The "addressable" designation for key security controls is eliminated.
How should healthcare organizations prioritize cybersecurity spending?
By actual attack patterns: (1) MFA on remote access and privileged accounts — prevents the majority of initial access vectors, (2) network segmentation between clinical, admin, device, and backup zones, (3) EDR with 24/7 monitoring, (4) encryption at rest and in transit, (5) incident response planning with quarterly tabletops, (6) third-party vendor risk assessment for all SaaS platforms with PHI access.
Building Architecture That Survives the Next Breach
The Change Healthcare breach was a preview. Stryker, CareCloud, and the 36% annual increase in attacks confirm the threat is accelerating faster than most organizations' defenses.
The architecture in this post — seven-layer defense-in-depth, five-pillar Zero Trust, healthcare-specific attack surface hardening, encryption with proper key management, and a rehearsed incident response playbook — maps every control to a NIST CSF function and addresses real attack vectors from documented breaches. Every component uses commercially available technology.
The proposed HIPAA Security Rule will codify many of these requirements into regulation. Organizations that build now will be compliant when it takes effect. Organizations that wait will remain vulnerable to the same basic attack patterns that exposed 192.7 million records.
The question is not whether your organization will face a significant cyberattack. The question is whether your architecture is built to contain it.
Nirmitee builds security-first healthcare platforms with HIPAA-compliant architecture, FHIR-native API security, and defense-in-depth by default. If you are building or modernizing clinical systems and need architecture that meets this security bar, let's talk.